Amazon AWS Certified Security - Specialty (old) SCS-C02 Exam Questions
[Identity and Access Management]
A company is using Amazon Elastic Container Service (Amazon ECS) to deploy an application that deals with sensitive data During a recent security audit, the company identified a security issue in which Amazon RDS credentials were stored with the application code In the company's source code repository
A security engineer needs to develop a solution to ensure that database credentials are stored securely and rotated periodically. The credentials should be accessible to the application only The engineer also needs to prevent database administrators from sharing database credentials as plaintext with other teammates. The solution must also minimize administrate overhead
Which solution meets these requirements?
Answer : D
To ensure that database credentials are stored securely and rotated periodically, the security engineer should do the following:
Use AWS Secrets Manager to store database credentials. This allows the security engineer to encrypt and manage secrets centrally, and to configure automatic rotation schedules for them.
Use IAM roles for ECS tasks to restrict access to database credentials to specific containers only. This allows the security engineer to grant fine-grained permissions to ECS tasks based on their roles, and to avoid sharing credentials as plaintext with other teammates.
[Incident Response]
A security engineer needs to develop a process to investigate and respond to po-tential security events on a company's Amazon EC2 instances. All the EC2 in-stances are backed by Amazon Elastic Block Store (Amazon EBS). The company uses AWS Systems Manager to manage all the EC2 instances and has installed Systems Manager Agent (SSM Agent) on all the EC2 instances.
The process that the security engineer is developing must comply with AWS secu-rity best practices and must meet the following requirements:
* A compromised EC2 instance's volatile memory and non-volatile memory must be preserved for forensic purposes.
* A compromised EC2 instance's metadata must be updated with corresponding inci-dent ticket information.
* A compromised EC2 instance must remain online during the investigation but must be isolated to prevent the spread of malware.
* Any investigative activity during the collection of volatile data must be cap-tured as part of the process.
Which combination of steps should the security engineer take to meet these re-quirements with the LEAST operational overhead? (Select THREE.)
Answer : A, C, E
[Identity and Access Management]
A security engineer needs to implement a write-once-read-many (WORM) model for data that a company will store in Amazon S3 buckets. The company uses the S3 Standard storage class for all of its S3 buckets. The security engineer must en-sure that objects cannot be overwritten or deleted by any user, including the AWS account root user.
Which solution will meet these requirements?
Answer : A
[Identity and Access Management]
For compliance reasons a Security Engineer must produce a weekly report that lists any instance that does not have the latest approved patches applied. The Engineer must also ensure that no system goes more than 30 days without the latest approved updates being applied
What would the MOST efficient way to achieve these goals?
Answer : B
Amazon EC2 Systems Manager is a service that helps you automatically collect software inventory, apply OS patches, create system images, and configure Windows and Linux operating systems3.You can use Systems Manager to report on instance patch compliance and enforce updates during the defined maintenance windows4. The other options are either inefficient or not feasible for achieving the goals.
[Logging and Monitoring]
A company has a strict policy against using root credentials. The company's security team wants to be alerted as soon as possible when root credentials are used to sign in to the AWS Management Console.
How should the security team achieve this goal?
Answer : B
[Logging and Monitoring]
AWS CloudTrail is being used to monitor API calls in an organization. An audit revealed that CloudTrail is failing to deliver events to Amazon S3 as expected.
What initial actions should be taken to allow delivery of CloudTrail events to S3? (Select TWO.)
Answer : A, D
To resolve CloudTrail's failure to deliver events to S3, verifying the S3 bucket policy for CloudTrail's write permissions (A) and ensuring the existence of the specified S3 bucket (D) are critical initial steps. These actions ensure that CloudTrail has the necessary permissions and a valid destination for log file delivery, addressing common configuration issues that can interrupt event logging.
[Identity and Access Management]
A company's Security Auditor discovers that users are able to assume roles without using multi-factor authentication (MFA). An example of a current policy being applied to these users is as follows:
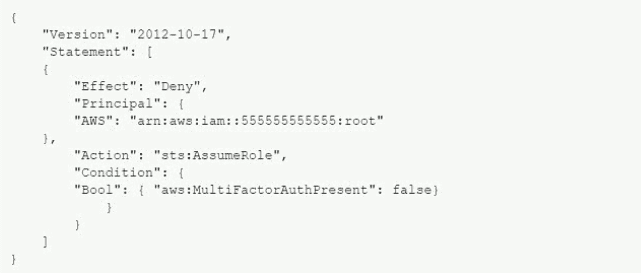
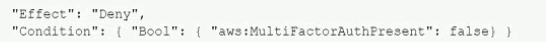
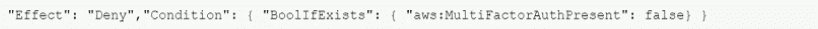
The Security Auditor finds that the users who are able to assume roles without MFA are alt coming from the IAM CLI. These users are using long-term IAM credentials. Which changes should a Security Engineer implement to resolve this security issue?(Select TWO.)
A)
B)
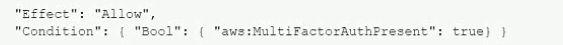
C)

D)
E)

Answer : A, D