Palo Alto Networks Certified Security Engineer PAN-OS 11.0 PCNSE Exam Questions
Which three methods are supported for split tunneling in the GlobalProtect Gateway? (Choose three.)
Answer : C, D, E
Which action does a firewall take when a decryption profile allows unsupported modes and unsupported traffic with TLS 1.2 protocol traverses the firewall?
Answer : D
A standalone firewall with local objects and policies needs to be migrated into Panoram
a. What procedure should you use so Panorama is fully managing the firewall?
Answer : C
Based on the images below, and with no configuration inside the Template Stack itself, what access will the device permit on its management port?
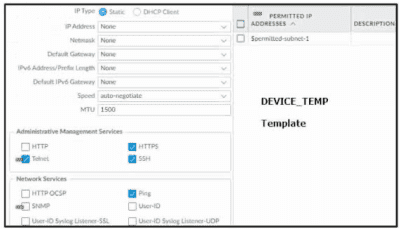
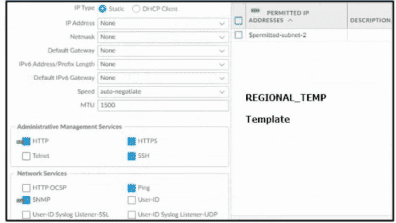

Answer : D
How can a firewall be set up to automatically block users as soon as they are found to exhibit malicious behavior via a threat log?
Answer : B
To block users dynamically based on threat log activity, dynamic user groups (DUGs) with tagging provide an automated solution. Option B configures a DUG with a 'malicious' tag, a Log Forwarding profile to tag users in the threat log (e.g., via threat intelligence), and a Security policy to block the tagged group. This leverages User-ID and is ideal for user-based blocking.
Option A uses dynamic address groups (DAGs), which block IPs, not users. Option C (security profiles) can block traffic but not dynamically tag/block users without additional configuration. Documentation supports DUGs for this use case.
Which type of policy in Palo Alto Networks firewalls can use Device-ID as a match condition?
Answer : C
The type of policy in Palo Alto Networks firewalls that can use Device-ID as a match condition is QoS. This is because Device-ID is a feature that allows the firewall to identify and classify devices on the network based on their characteristics, such as vendor, model, OS, and role1. QoS policies are used to allocate bandwidth and prioritize traffic based on various criteria, such as application, user, source, destination, and device2. By using Device-ID as a match condition in QoS policies, the firewall can apply different QoS actions to different types of devices, such as IoT devices, laptops, smartphones, etc3. This can help optimize the network performance and ensure the quality of service for critical applications and devices.
An administrator would like to determine which action the firewall will take for a specific CVE. Given the screenshot below, where should the administrator navigate to view this information?
Answer : C
The Exceptions settings allows you to change the response to a specific signature. For example, you can block all packets that match a signature, except for the selected one, which generates an alert. The Exception tab supports filtering functions.
If you not believed, then login the firewall go to Vulnerability > Exceptions and select 'Show all signatures'. From there you will see all threat information including specific actions.
More detail: https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000Cm4yCAC