Blockchain BTA Certified Blockchain Solution Architect CBSA Exam Questions
Which of the following cryptocurrencies use an alternate consensus method called "Scrypt" to BTC's Proof of Work (POW) SHA-256 algorithm?
Answer : C
The Scrypt hash function was initially implemented by the Litecoin development team to avoid what are known, ASICs, from being able mine its cryptocurrency. When mining for cryptocurrencies, users typically have an option between: a CPU, GPU or ASIC miner.
The ____________of the tree is the topmost node and hence this tree is represented upside down. The bottommost nodes are called as ________nodes. Each node is simply a cryptographic hash of a transaction.
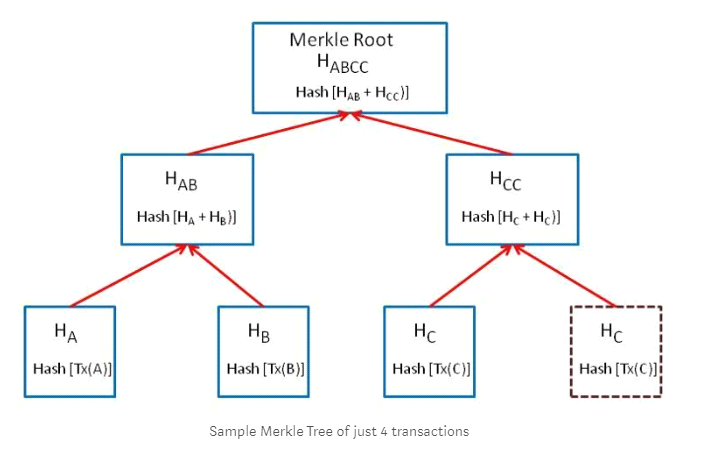
In the above diagram, Transaction A,B, C,C from the leaves of the tree. Select one.
Answer : B
The root of the tree is the topmost node and hence this tree is represented upside down. The bottommost nodes are called as leaf nodes. Each node is simply a cryptographic hash of a transaction. In the above diagram, Transaction A,B,C,C form the leaves of the tree.
Which technical feature of blockchain best promotes the notion of a blockchain being ''censorship resistant''?
Answer : A
In its simplest form, user identity on a blockchain can be unique and secure:
Answer : C
Which of the following scenarios and databases is least suited to be utilized by a blockchain solution?
Answer : A
What are two cryptocurrencies that you would expect to see mining equipment with ASICS? (Select two.)
Answer : A, D
Select the two kinds of accounts in Ethereum which share the same address space. (Select two.)
Answer : B, C