CheckPoint Check Point Certified Security Expert - R81.20 156-315.81 Exam Questions
What is the protocol and port used for Health Check and State Synchronization in ClusterXL?
Answer : C
ClusterXL is a clustering technology that provides high availability and load sharing for Security Gateways. ClusterXL uses a proprietary protocol called Check Point Cluster Protocol (CCP) to communicate between cluster members. CCP has two main functions: Health Check and State Synchronization. Health Check is the mechanism that monitors the status and availability of each cluster member and determines which member is the active one. State Synchronization is the mechanism that synchronizes the connection and NAT tables between cluster members to ensure a smooth failover in case of a member failure. CCP uses UDP port 8116 for both Health Check and State Synchronization messages. The other options are not correct because:
A) CCP and 18190: This option is incorrect because CCP does not use port 18190. Port 18190 is used by Secure Internal Communication (SIC) between Security Gateways and Management Servers.
B) CCP and 257: This option is incorrect because CCP does not use port 257. Port 257 is used by Check Point Security Management Protocol (CPM) for communication between SmartConsole and Management Servers.
D) CPC and 8116: This option is incorrect because there is no such protocol as CPC in ClusterXL.
Which of the following cannot be configured in an Access Role Object?
Answer : D
The verified answer is D) Time.
An Access Role object is a logical representation of a set of users, machines, or networks that can be used in the security policy1. An Access Role object can include the following components1:
Networks: IP addresses or network objects that define the source or destination of the traffic.
Machines: Specific hosts or machine groups that are identified by their MAC addresses or certificates.
Users: Specific users or user groups that are authenticated by one or more identity sources, such as Active Directory, LDAP, or Identity Awareness.
Time is not a component of an Access Role object, and it cannot be configured in it. Time is a separate object type that can be used to define the validity period of a rule or a policy2.
LDAP group vs Access role objects - Check Point CheckMates3
THE IMPORTANCE OF ACCESS ROLES - Check Point Software1
Time Objects - Check Point Software2
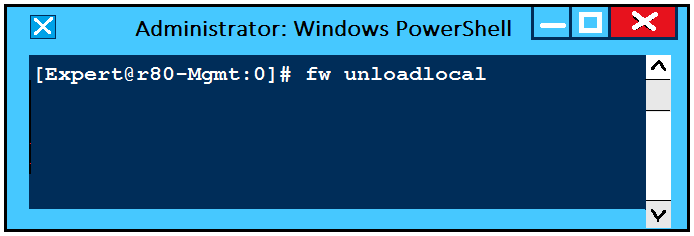
What will be the effect of running the following command on the Security Management Server?
Answer : A
Running the command fw unloadlocal on the Security Management Server will remove the installed Security Policy from the local firewall module. This command is useful for troubleshooting purposes when there is a problem with the policy installation or enforcement. However, it will also expose the Security Management Server to potential attacks, so it should be used with caution. Reference:Training & Certification | Check Point Software, R81 CCSA & CCSE exams released featuring Promo for... - Check Point ...
SmartEvent has several components that function together to track security threats. What is the function of the Correlation Unit as a component of this architecture?
Answer : A
The Correlation Unit in SmartEvent architecture has the function of analyzing each log entry as it arrives at the log server according to the Event Policy. When it identifies a threat pattern, it forwards an event to the SmartEvent Server. This is an essential function in threat detection and analysis, as it helps in identifying and alerting about security threats based on the configured policies.
Option A correctly describes the function of the Correlation Unit, making it the verified answer.
Which of the following type of authentication on Mobile Access can NOT be used as the first authentication method?
Answer : A
What is the default size of NAT table fwx_alloc?
Answer : C
What is the default size of NAT table fwx_alloc? The default size of NAT table fwx_alloc is25000. This table stores the connections that require NAT translation by the Security Gateway. The size of this table can be changed by using the commandfw ctl set int fwx_alloc <value>, where <value> is the desired number of connections. The maximum value is 65535. To make this change permanent, you need to add this command to the file$FWDIR/conf/fwaffinity.confon the Security Gateway. Reference: [R81 Performance Tuning Administration Guide], page 126.
As an administrator, you may be required to add the company logo to reports. To do this, you would save the logo as a PNG file with the name 'cover-company-logo.png' and then copy that image file to which directory on the SmartEvent server?
Answer : C
To add the company logo to reports, you would save the logo as a PNG file with the name 'cover-company-logo.png' and then copy that image file to the $RTDIR/smartview/conf directory on the SmartEvent server. The $RTDIR is an environment variable that points to the runtime directory of the SmartEvent server, which is usually /opt/CPrt-R81. The smartview/conf directory contains the configuration files for SmartView, which is a web-based interface for viewing reports and dashboards generated by SmartEvent. Reference:SmartEvent Administration Guide,SK120193 - How to add a company logo to SmartView reports