Cisco Certified Support Technician (CCST) IT Support 100-140 CCST IT Support Exam Questions
Which three pieces of information would be considered Personally Identifiable Information (PII)? (Choose three.)
Note: You will receive partial credit for each correct selection.
Answer : B, C
Fingerprint is a unique biometric identifier and qualifies as PII.
Email Address directly identifies or contacts an individual.
Date of Birth is a personal datum that, when combined with other data, identifies someone.
Which two of the following are supported operating systems for Remote Desktop client connections? (Choose two.)
Note: You will receive partial credit for each correct selection.
Answer : A, B
Windows 11 Pro and Windows 10 Enterprise include the Remote Desktop Host feature and fully support incoming Remote Desktop client connections.
The Home editions (Windows 11 Home and Windows 10 Home) can initiate Remote Desktop sessions as clients but cannot act as a host to accept incoming connections.
You receive an email from a user with the display name of the President of your company. The email requests that you do them a favor and purchase gift cards and send the gift cards to an email address provided.
What should you do?
Answer : C
This scenario is a classic example of email spoofing and a social engineering attack. You should contact the IT department immediately using internal communication methods to verify the legitimacy of the request. Never respond or take action based on suspicious emails.
You are working from home over a weekend to resolve a backlog of employee help desk tickets. A user issue requires you to access their Windows 11 computer in the home office to check its settings. You have verified that the machine is available, but the user is not present.
Which remote access application is best suited for this task?
Answer : C
A user who has been on vacation for the past 30 days calls the help desk and reaches you. The user reports the following:
Before I left for vacation, I changed my password and made sure it worked. My password is not due to be reset for another 60 days, but I can't log in to the network.
While the user was gone, the company established a requirement for Multi-Factor Authentication (MFA).
Which two actions could you take to resolve the problem? (Choose two.)
Note: Each correct answer presents a complete solution.
Answer : A, C
Installing the company's authenticator app enrolls the user in MFA as now required.
Adding a phone number enables SMS-based second-factor validation.
You receive an email request for personal information.
You need to make sure you are working with the right individual to avoid a social engineering attempt.
Which step should you take?
Answer : C
The safest and most professional approach is to use company-approved methods to verify identity, such as callback procedures, employee ID verification, or multi-factor authentication. This helps prevent falling victim to phishing or social engineering.
An employee is having problems reaching URLs on the World Wide Web. You examine the addressing configuration for the employee's PC that is shown as follows:
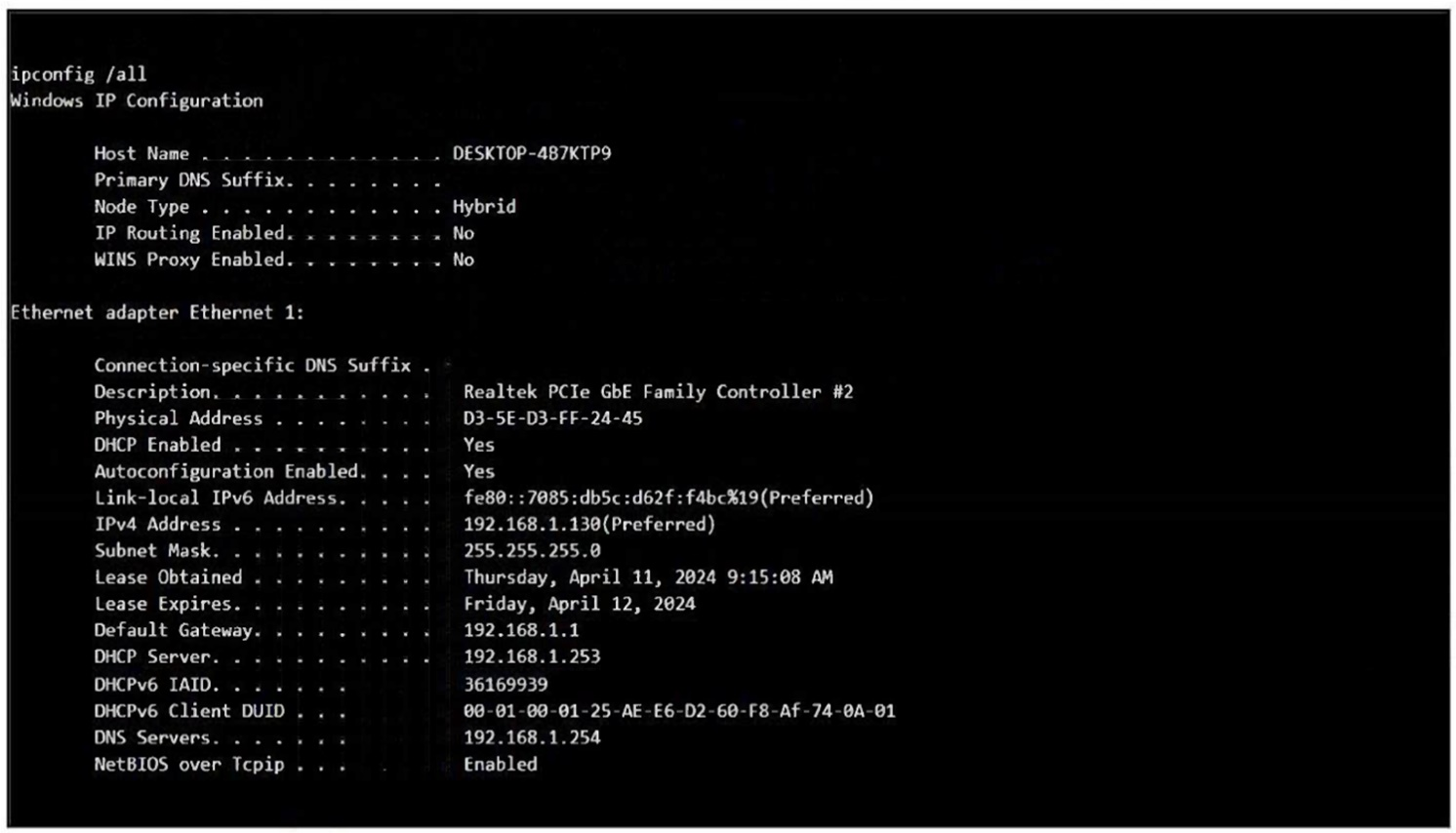
You have verified that you can open a website on the employee's PC by entering the website's IP address in their browser.
Which IP address should you ping to determine what the problem is?
Answer : D
Since you can access websites by IP but not by name, the issue lies with name resolution. Pinging the configured DNS server (192.168.1.254) will verify whether the DNS service is reachable and functioning.