Cisco Certified Support Technician (CCST) Networking 100-150 Exam Questions
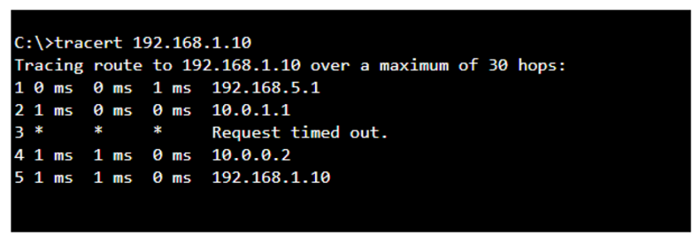
A user reports that a company website is not available. The help desk technician issues a tracert command to determine if the server hosting the website is reachable over the network. The output of the command is shown as follows:
What can you tell from the command output?
Answer : C
The tracert command output shows the path taken to reach the destination IP address, 192.168.1.10. The command output indicates:
* Hops 1 and 2 are successfully reached.
* Hop 3 times out, meaning the router at hop 3 did not respond to the tracert request. However, this does not necessarily indicate a problem with forwarding packets, as some routers may be configured to block or not respond to ICMP requests.
* Hops 4 and 5 are successfully reached, with hop 5 being the destination IP 192.168.1.10, indicating that the server is reachable.
Thus, the correct answer is C. The server with the address 192.168.1.10 is reachable over the network.
* Cisco Traceroute Command
* Understanding Traceroute
The tracert command output indicates that the server with the address 192.168.1.10 is reachable over the network. The asterisk (*) at hop 3 suggests that the probe sent to that hop did not return a response, which could be due to a variety of reasons such as a firewall blocking ICMP packets or the router at that hop being configured not to respond to ICMP requests. However, since the subsequent hops (4 and 5) are showing response times, it means that the packets are indeed getting through and the server is reachable12.
* How to Use Traceroute Command to Read Its Results
* How to Use the Tracert Command in Windows
Which two statements are true about the IPv4 address of the default gateway configured on a host? (Choose 2.)
Note: You will receive partial credit for each correct selection.
Answer : B, D
* Statement B: 'The same default gateway IPv4 address is configured on each host on the local network.' This is true because all hosts on the same local network (subnet) use the same default gateway IP address to send packets destined for other networks.
* Statement D: 'The default gateway is the IPv4 address of the router interface connected to the same local network as the host.' This is true because the default gateway is the IP address of the router's interface that is directly connected to the local network.
* Statement A: 'The IPv4 address of the default gateway must be the first host address in the subnet.' This is not necessarily true. The default gateway can be any address within the subnet range.
* Statement C: 'The default gateway is the Loopback0 interface IPv4 address of the router connected to the same local network as the host.' This is not true; the default gateway is the IP address of the router's physical or logical interface connected to the local network.
* Statement E: 'Hosts learn the default gateway IPv4 address through router advertisement messages.' This is generally true for IPv6 with Router Advertisement (RA) messages, but not typically how IPv4 hosts learn the default gateway address.
* Cisco Default Gateway Configuration: Cisco Default Gateway
A host is given the IP address 172.16.100.25 and the subnet mask 255.255.252.0.
What is the CIDR notation for this address?
Answer : D
The CIDR (Classless Inter-Domain Routing) notation for the subnet mask 255.255.252.0 is /22. This notation indicates that the first 22 bits of the IP address are used for network identification, and the remaining bits are used for host addresses within the network1.
* Subnet Cheat Sheet -- 24 Subnet Mask, 30, 26, 27, 29, and other IP Address CIDR Network Reference
=========================
* Subnet Mask to CIDR Notation: The given subnet mask is 255.255.252.0. To convert this to CIDR notation:
* Convert the subnet mask to binary: 11111111.11111111.11111100.00000000
* Count the number of consecutive 1s in the binary form: There are 22 ones.
* Therefore, the CIDR notation is /22.
* Understanding Subnetting and CIDR: Cisco CIDR Guide
You need to connect a computer's network adapter to a switch using a 1000BASE-T cable.
Which connector should you use?
Answer : D
* 1000BASE-T Cable: This refers to Gigabit Ethernet over twisted-pair cables (Cat 5e or higher).
* Connector: RJ-45 connectors are used for Ethernet cables, including those used for 1000BASE-T.
* Coax: Used for cable TV and older Ethernet standards like 10BASE2.
* RJ-11: Used for telephone connections.
* OS2 LC: Used for fiber optic connections.
* Ethernet Standards and Cables: Ethernet Cable Guide
During the data encapsulation process, which OSI layer adds a header that contains MAC addressing information and a trailer used for error checking?
Answer : C

The Data Link layer ensures that messages are delivered to the proper device on a LAN using hardware addresses and translates messages from the Network layer into bits for the Physical layer to transmit. It also controls how data is placed onto the medium and is received from the medium through the physical hardware.
The OSI Model -- The 7 Layers of Networking Explained in Plain English
Which standard contains the specifications for Wi-Fi networks?
Answer : C
The IEEE 802.11 standard contains the specifications for Wi-Fi networks. It is a set of media access control (MAC) and physical layer (PHY) specifications for implementing wireless local area network (WLAN) computer communication in various frequencies, including but not limited to 2.4 GHz, 5 GHz, and 6 GHz1. This standard is maintained by the Institute of Electrical and Electronics Engineers (IEEE) and is commonly referred to as Wi-Fi. The standard has evolved over time to include several amendments that improve speed, range, and reliability of wireless networks.
* The Most Common Wi-Fi Standards and Types, Explained
* 802.11 Standards Explained: 802.11ax, 802.11ac, 802.11b/g/n, 802.11a
* Wi-Fi Standards Explained - GeeksforGeeks
=========================
Which protocol allows you to securely upload files to another computer on the internet?
Answer : A
SFTP, or Secure File Transfer Protocol, is a protocol that allows for secure file transfer capabilities between networked hosts. It is a secure extension of the File Transfer Protocol (FTP). SFTP encrypts both commands and data, preventing passwords and sensitive information from being transmitted openly over the network. It is typically used for secure file transfers over the internet and is built on the Secure Shell (SSH) protocol1.
* What Is SFTP? (Secure File Transfer Protocol)
* How to Use SFTP to Safely Transfer Files: A Step-by-Step Guide
* Secure File Transfers: Best Practices, Protocols And Tools
The Secure File Transfer Protocol (SFTP) is a secure version of the File Transfer Protocol (FTP) that uses SSH (Secure Shell) to encrypt all commands and data. This ensures that sensitive information, such as usernames, passwords, and files being transferred, are securely transmitted over the network.
* ICMP (Internet Control Message Protocol) is used for network diagnostics and is not designed for file transfer.
* NTP (Network Time Protocol) is used to synchronize clocks between computer systems and is not related to file transfer.
* HTTP (HyperText Transfer Protocol) is used for transmitting web pages over the internet and does not inherently provide secure file transfer capabilities.
Thus, the correct protocol that allows secure uploading of files to another computer on the internet is SFTP.
* Cisco Learning Network
* SFTP Overview (Cisco)