Cisco Understanding Cisco Cybersecurity Operations Fundamentals 200-201 CCNACBR Exam Questions
Refer to the exhibit.
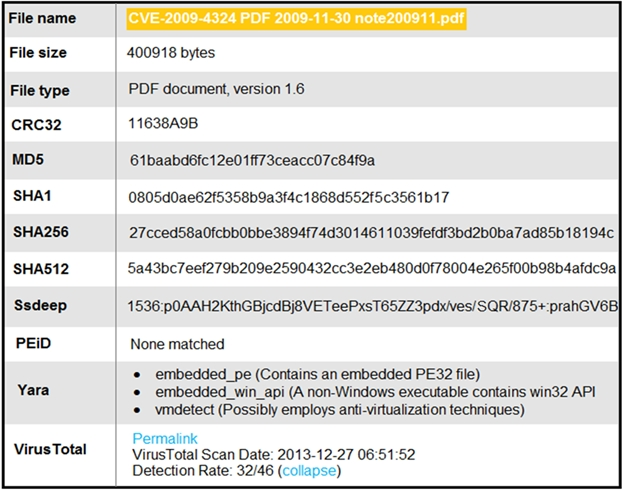
An engineer is analyzing this Cuckoo Sandbox report for a PDF file that has been downloaded from an email. What is the state of this file?
Answer : C
Which option describes indicators of attack?
Answer : D
Indicators of attack (IoAs) are signs that an attack may be in progress or imminent. Malware reinfection within a few minutes of removal (D) is a strong IoA because it suggests that the attacker has a persistent mechanism to redeploy malware, indicating an active compromise of the system.
Which technology should be used to implement a solution that makes routing decisions based on HTTP header, uniform resource identifier, and SSL session ID attributes?
Answer : C
A load balancer is the correct technology to implement a solution that makes routing decisions based on HTTP header, uniform resource identifier (URI), and SSL session ID attributes.Load balancers can inspect incoming traffic and make routing decisions to distribute the traffic across multiple servers based on various attributes, including the ones mentioned, to ensure optimal resource use and efficient traffic management12.
Cisco Unified Border Element Configuration Guide1.
URI based outbound Dial-peer configuration on CUBE - Cisco Community
A threat actor penetrated an organization's network. Using the 5-tuple approach, which data points should the analyst use to isolate the compromised host in a grouped set of logs?
Answer : B
The 5-tuple approach consists of protocol, source IP address, source port number, destination IP address, and destination port number to uniquely identify sessions between endpoints on a network.Reference:=Cisco Cybersecurity Source Documents
How does certificate authority impact a security system?
Answer : B
A Certificate Authority (CA) is responsible for issuing digital certificates to validate the identity of the certificate holder and provide a means to establish secure communications over networks like the Internet.Reference:=Cisco Cybersecurity Source Documents
An engineer received an alert affecting the degraded performance of a critical server Analysis showed a heavy CPU and memory load What is the next step the engineer should take to investigate this resource usage7
Answer : A
When a server is experiencing high CPU and memory load, the first step is to identify the processes that are consuming the most resources. The command ''ps -ef'' is used to display information about all the running processes, including their IDs, memory and CPU usage, and the commands that started them.This allows the engineer to pinpoint which processes are responsible for the high load and take appropriate action, such as terminating unnecessary processes or optimizing resource usage345.Reference: Various resources on server management and troubleshooting recommend using the ''ps -ef'' command as a starting point for investigating high resource usage on servers
What is obtained using NetFlow?
Answer : A
NetFlow is a network protocol developed by Cisco for collecting IP traffic information and monitoring network flow. It provides valuable data about the network sessions occurring within the network, such as source and destination IP addresses, port numbers, and protocols used. This session data is useful for understanding traffic patterns, volume, and usage.