Cisco Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies 300-215 CBRFIR Exam Questions
In a secure government communication network, an automated alert indicates the presence of anomalous DLL files injected into the system memory during a routine update of communication protocols. These DLL files are exhibiting beaconing behavior to a satellite IP known for signal interception risks. Concurrently, there is an uptick in encrypted traffic volumes that suggests possible data exfiltration. Which set of actions should the security engineer prioritize?
Answer : A
In highly sensitive environments such as secure government networks, the presence of anomalous DLL injection, beaconing to known interception points, and signs of encrypted data exfiltration constitutes a critical incident. The appropriate response in such classified contexts involves:
Invoking a pre-established, classified incident response protocol,
Immediately notifying national cyber defense operatives (such as national CERT or military cyber command),
Prioritizing containment to stop lateral spread,
Proceeding with eradication of malware or backdoors.
This response sequence aligns with the high-severity, immediate-response model described in the Cisco CyberOps Associate v1.2 curriculum under national defense and classified incident frameworks. The study guide emphasizes the importance of stakeholder communication and multi-agency coordination during advanced persistent threat (APT) intrusions involving critical infrastructure or defense systems.
Refer to the exhibit.

An engineer received a ticket to analyze a recent breach on a company blog. Every time users visit the blog, they are greeted with a message box. The blog allows users to register, log in, create, and provide comments on various topics. Due to the legacy build of the application, it stores user information in the outdated MySQL database. What is the recommended action that an engineer should take?
Answer : A
The alert box in the screenshot ('HACKED BY 1337') is a classic sign of Cross-Site Scripting (XSS). This occurs when unvalidated input is executed as code in a browser.
To prevent this:
The Cisco CyberOps Associate guide recommends strict input validation as the primary defense against XSS and similar web-based injection attacks.
An organization recovered from a recent ransomware outbreak that resulted in significant business damage. Leadership requested a report that identifies the problems that triggered the incident and the security team's approach to address these problems to prevent a reoccurrence. Which components of the incident should an engineer analyze first for this report?
Answer : B
To prepare a post-incident report, the cause of the incident (what enabled it) and the effect (what damage was done) are the primary components analyzed first. This allows teams to understand vulnerabilities exploited and the consequences, forming the basis for corrective action.
The Cisco CyberOps guide recommends beginning with root cause analysis followed by impact assessment to guide future prevention strategies.
Refer to the exhibit.
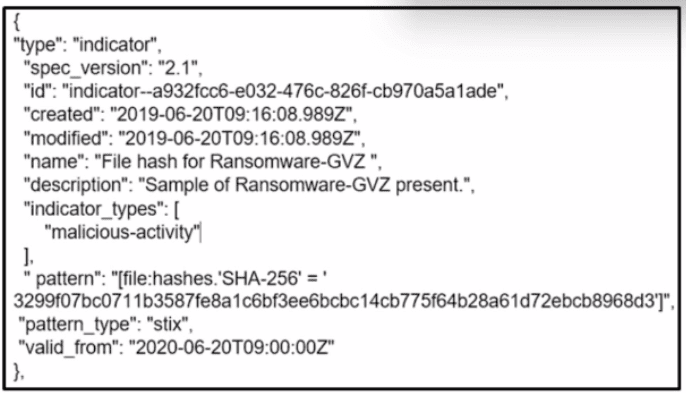
What is the indicator of compromise?
Answer : A
The STIX data structure shows a pattern field with this entry:
file:hashes.'SHA-256' = '3299f07bc0711b3587fe8a1c6bf3ee6cbcc14cb775f64b28a61d72ebcb8968d3'
This value is a SHA-256 file hash, a well-known indicator of compromise (IoC) for identifying malicious files.
Therefore, the correct answer is:
A . SHA256 file hash.
Snort detects traffic that is targeting vulnerabilities in files that belong to software in the Microsoft Office suite. On a SIEM tool, the SOC analyst sees an alert from Cisco FMC. Cisco FMC is implemented with Snort IDs. Which alert message is shown?
Answer : D
Cisco Firepower Management Center (FMC), when configured with Snort rules, classifies attacks with signature categories such as FILE-OFFICE for Microsoft Office-based exploits. One of the critical threats involving Microsoft Office is a known vector involving Microsoft Graphics, which attackers exploit for remote code execution (RCE). RCE vulnerabilities enable attackers to execute arbitrary commands or code on the target machine---making this classification high-severity.
The alert 'FILE-OFFICE Microsoft Graphics remote code execution attempt' is consistent with what Cisco and Snort define for such threats and appears in rulesets addressing vulnerabilities like CVE-2017-0001.
---
What is the transmogrify anti-forensics technique?
Answer : D
The transmogrify anti-forensics technique refers specifically to the act of modifying the file header of a malicious file to disguise it as another file type. This type of manipulation helps evade detection by signature-based security tools and forensics analysis systems that rely on file headers to determine file type and purpose.
For example, a malicious .exe file might have its header changed to appear as a .jpg or .pdf to trick analysts or automated systems into treating it as benign. This tactic is particularly effective in bypassing content filtering and malware detection solutions that do not perform deep inspection beyond headers.
Refer to the exhibit.
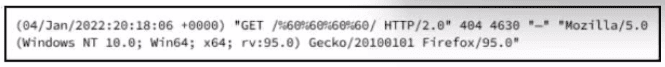
What is occurring?
Answer : D
Comprehensive and Detailed
The log entry contains the following key elements:
The timestamp: (04/Jan/2022:20:18:06 +0000)
HTTP method and URI: 'GET /%60%60%60%60%60%60/ HTTP/2.0'
HTTP status code: 404
User-Agent: Mozilla/5.0 ... Firefox/95.0
The status code 404 indicates that the requested resource was not found on the server. This is a standard HTTP response that signifies the server could not locate the requested URI (in this case, likely due to a malformed or invalid path /\`````/, where %60 is the URL-encoded form of the backtick character '').
There is no clear evidence of SQL injection, WAF detection, or redirection in this log. The use of encoded backticks may suggest probing behavior, but the log does not show a definitive attack signature.
Therefore, the correct interpretation is: