Cisco Conducting Threat Hunting and Defending using Cisco Technologies for CyberOps 300-220 CBRTHD Exam Questions
During a structured hunt, analysts using Cisco SIEM tools complete hypothesis testing and confirm malicious activity. What is the NEXT step in the Cisco threat hunting lifecycle?
Answer : B
The correct answer is document findings and operationalize detections. In Cisco's threat hunting methodology, confirmation of malicious activity is not the end of the hunt.
The most critical next step is to:
Document attacker behavior
Identify detection gaps
Create or improve SIEM, EDR, or NDR detection rules
This ensures the organization does not repeatedly rediscover the same threat. Options C and D are incident response and communication activities, not threat hunting lifecycle steps. Option A skips the crucial improvement phase.
The CBRTHD blueprint strongly emphasizes:
Continuous improvement
Feedback loops
Detection engineering
By operationalizing findings, the SOC increases maturity and forces adversaries to change tactics.
Therefore, Option B is correct.
The SOC team receives an alert about a user sign-in from an unusual country. After investigating the SIEM logs, the team confirms the user never signed in from that country. The incident is reported to the IT administrator who resets the user's password. Which threat hunting phase was initially used?
Answer : A
The correct answer is Collect and process intelligence and data. In this scenario, the initial threat hunting phase occurred when the SOC team received the alert and began analyzing SIEM logs to validate whether the activity was legitimate or malicious. This aligns directly with the first phase of the threat hunting lifecycle, which focuses on gathering, normalizing, and analyzing security-relevant data.
Threat hunting is a structured, hypothesis-driven process, but it always begins with data collection and intelligence processing. This includes ingesting logs from identity providers, authentication systems, cloud platforms, VPNs, and endpoint telemetry into a SIEM. In this case, the alert regarding a sign-in from an unusual country triggered analysts to examine historical login patterns and geolocation data. By confirming that the user had never authenticated from that country, the team established that the event was anomalous and likely malicious.
Option B (Response and resolution) occurred after the initial phase, when the IT administrator reset the user's password to contain the threat. Option C (Hypothesis) would involve formulating a theory such as ''the account may be compromised due to credential theft,'' but this step requires validated data first. Option D (Post-incident review) only happens after the incident has been fully resolved and lessons learned are documented.
From a professional cybersecurity operations perspective, this phase is critical because high-quality data determines hunt effectiveness. Poor log coverage or incomplete identity telemetry would prevent analysts from confidently confirming the anomaly. This example also highlights why identity-related telemetry is foundational to modern threat hunting---compromised credentials remain one of the most common initial access vectors.
In short, before a SOC can hypothesize, respond, or improve controls, it must first collect and process accurate intelligence and data, making option A the correct answer.
A threat hunting team wants to ensure hunts are repeatable, scalable, and less dependent on individual analyst intuition. What is the MOST important process improvement?
Answer : C
The correct answer is standardizing hunt documentation and hypotheses. Mature threat hunting programs move beyond ad-hoc, intuition-driven efforts.
Standardization enables:
Knowledge sharing
Consistent methodology
Repeatable hunts
Easier onboarding of new analysts
Option A and B support operations but do not improve hunting maturity. Option D is unrealistic and risky.
By documenting hypotheses, data sources, queries, findings, and outcomes, organizations institutionalize knowledge and continuously improve detection capabilities.
This is a defining characteristic of high-maturity threat hunting programs.
Therefore, option C is correct.
Refer to the exhibit.
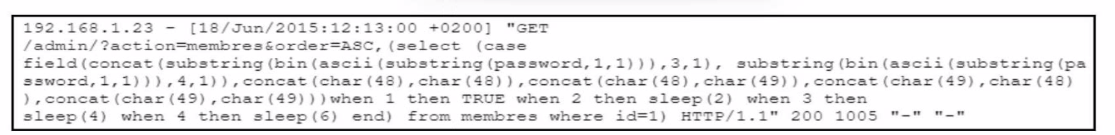
The cybersecurity team at a company detects an ongoing attack directed at the web server that hosts the company website. The team analyzes the logs of the web application firewall and discovers several HTTP requests encoded in Base64. The team decodes the payloads and retrieves the HTTP requests. What did the attackers use to exploit the server?
Answer : B
The correct answer is SQL injection. The decoded HTTP request shown in the exhibit contains multiple unmistakable indicators of a SQL injection attack, including the use of SQL keywords and functions such as SELECT, CASE, SUBSTRING, ASCII, BIN, and conditional SLEEP() statements. These elements are characteristic of time-based blind SQL injection, a technique attackers use to extract database information when direct query results are not visible.
From a professional cybersecurity perspective, the presence of expressions like:
SELECT (CASE WHEN ... THEN SLEEP(x))
SUBSTRING(password,1,1)
ASCII() and binary conversions
indicates that the attacker is probing the backend database character by character and using response timing to infer whether conditions are true or false. This is a well-known exploitation method used when error messages or query output are suppressed by the application.
The use of Base64 encoding does not represent the attack itself but rather an obfuscation technique to evade basic web application firewall (WAF) signatures and logging visibility. Encoding payloads allows attackers to bypass simple pattern-matching defenses, but once decoded, the underlying SQL injection becomes evident.
Option A (Unicode encoding) is incorrect because Unicode is commonly used for evasion, not exploitation. Option C (directory traversal) typically involves sequences like ../ to access filesystem paths, which are not present. Option D (XSS) targets client-side script execution and would include JavaScript payloads rather than database-focused logic.
According to the MITRE ATT&CK framework, this activity maps to Initial Access -- Exploit Public-Facing Application (T1190). SQL injection remains one of the most exploited vulnerabilities in public-facing applications due to poor input validation and insecure coding practices.
For threat hunters and defenders, this scenario reinforces the importance of deep payload inspection, decoding obfuscated requests, monitoring for anomalous database query behavior, and enforcing secure development practices such as parameterized queries and input sanitization. SQL injection continues to be a high-impact, real-world attack vector despite being well understood, making it a critical focus area in web application threat hunting.
Refer to the exhibit.
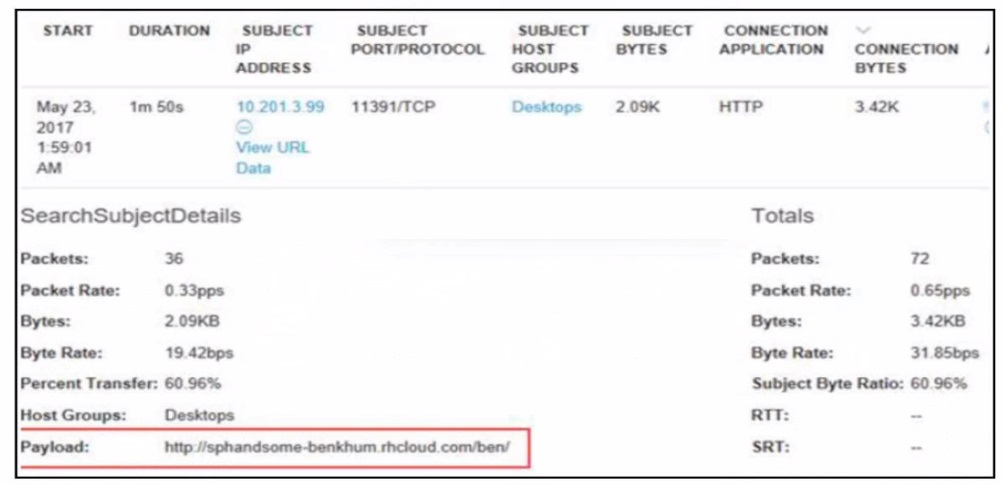
A security analyst receives an alert from Cisco Secure Network Analytics (formerly StealthWatch) with the C2 category. Which information aids the investigation?
Answer : C
The correct answer is C. Host 10.201.3.99 is attempting to contact the C2 server to retrieve the payload.
Cisco Secure Network Analytics (Stealthwatch) detects Command-and-Control (C2) activity by analyzing network behavior, not by relying solely on known malicious indicators. In the exhibit, the critical investigative clue is the HTTP payload containing a suspicious external URL, which strongly suggests outbound communication from an internal host to an external command-and-control infrastructure.
The internal IP address 10.201.3.99 belongs to a workstation group (''Desktops''), indicating it is an internal endpoint, not a C2 server. This immediately rules out option B. Instead, the endpoint is acting as a compromised host (zombie) attempting to reach a remote server controlled by an attacker. This outbound beaconing behavior is a classic hallmark of C2 communication.
Option A is incorrect because packet count alone does not confirm C2 activity. C2 traffic is often low-and-slow, intentionally designed to blend in with normal traffic patterns. Option D is also incorrect because the payload does not describe the zombie endpoint; rather, it shows a remote URL, which is likely part of malware staging or command retrieval.
From a threat hunting and SOC perspective, the most valuable information is directionality and intent:
Internal host external suspicious domain
HTTP-based communication over an unusual port
Low data volume consistent with beaconing or payload retrieval
This aligns with MITRE ATT&CK -- Command and Control (TA0011) techniques such as Application Layer Protocols (T1071). Identifying which internal host is reaching out---and why---is essential for containment, endpoint isolation, and scope expansion.
Professionally, this insight enables the analyst to:
Quarantine host 10.201.3.99
Pivot to EDR telemetry on that endpoint
Block the external domain or IP
Hunt for similar beaconing patterns across the environment
In summary, the investigation is aided most by understanding that an internal host is actively communicating with a C2 server, making Option C the correct and operationally meaningful answer.
According to the MITRE ATT&CK framework, how is the password spraying technique classified?
Answer : D
The correct answer is Credential Access. In the MITRE ATT&CK framework, password spraying is classified under the Credential Access tactic (TA0006), specifically technique T1110.003 -- Password Spraying. This classification is based on the attacker's primary objective: gaining valid credentials by systematically attempting a small number of common or weak passwords across many user accounts.
Password spraying differs from brute-force attacks in that it intentionally avoids rapid or repeated attempts against a single account, thereby evading account lockout controls and basic detection mechanisms. Instead, attackers ''spray'' one password (for example, Winter2025! or Password123) across a large number of users, exploiting the likelihood that at least one account will use that password.
Although successful password spraying often leads to initial access, MITRE classifies it under Credential Access because the technique's defining action is the acquisition of credentials, not the system entry itself. Initial access is the outcome, while credential theft is the method. This distinction is critical for threat hunters, as it guides where detections and controls should be focused.
From a professional threat hunting perspective, defenders monitor authentication telemetry such as failed and successful logins across identity providers, VPNs, cloud services, and email platforms. Indicators include multiple authentication failures across many accounts from a single source IP, followed by one or more successful logins. Identity-centric logging and anomaly detection are foundational here, reinforcing the principle that identity is the primary attack surface in modern environments.
Understanding password spraying as a credential access technique helps organizations prioritize protections such as strong password policies, MFA enforcement, adaptive authentication, and detection logic tuned for low-and-slow authentication abuse.
What is a limitation of automated dynamic malware analysis tools?
Answer : B
The correct answer is They produce false positives and false negatives. Automated dynamic malware analysis tools, such as sandboxes, execute suspicious files in isolated environments to observe runtime behavior. While these tools are extremely valuable in modern SOCs, they are not infallible and have well-known limitations.
False positives occur when benign software exhibits behaviors that resemble malicious activity, such as creating registry keys, spawning child processes, or making network connections. Conversely, false negatives occur when malware intentionally evades detection by altering its behavior. Many modern malware samples include sandbox evasion techniques such as checking for virtualized environments, delaying execution, requiring user interaction, or disabling malicious functionality when analysis artifacts are detected.
Option A is incorrect because dynamic analysis can, in fact, uncover runtime vulnerabilities and exploit behavior. Option C is misleading; while tooling coverage varies, language support is not the primary limitation. Option D refers to manual analysis, whereas the question explicitly addresses automated tools.
From a threat hunting and malware analysis standpoint, professionals understand that sandbox results must be correlated with other telemetry, including endpoint behavior, network traffic, and threat intelligence. Automated tools are best used as part of a layered analysis strategy, not as a single source of truth.
This limitation reinforces a core security principle: automation accelerates detection, but human judgment validates impact. Skilled analysts interpret sandbox results, investigate anomalies, and determine real-world risk. Understanding the strengths and weaknesses of dynamic analysis tools allows SOC teams to avoid overreliance on automation while still benefiting from its speed and scale.