Cisco Designing and Implementing Cloud Connectivity 300-440 ENCC Exam Questions
Refer to the exhibits.
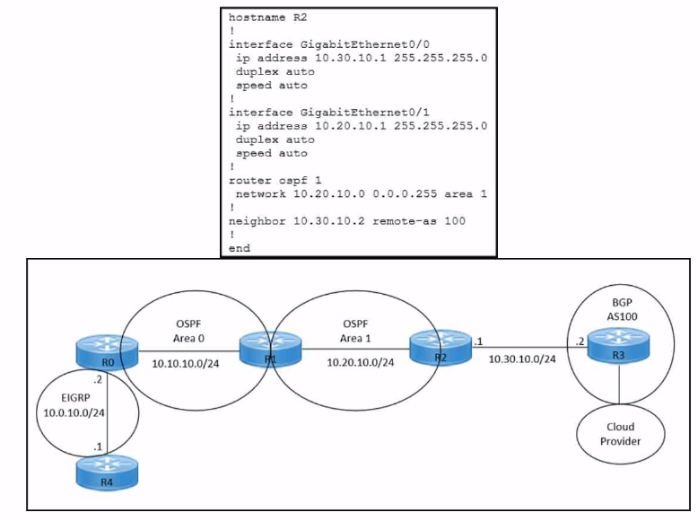
Refer to the exhibits. An engineer must redistribute OSPF internal routes into BGP to connect an on-premises network to a cloud provider without introducing extra routes. Which two commands must be configured on router R2? (Choose two.)
Answer : B, E
To redistribute OSPF internal routes into BGP, the engineer needs to configure two commands on router R2. The first command isrouter bgp 100, which enables BGP routing process and specifies the autonomous system number of 100. The second command isredistribute ospf 1 match internal external, which redistributes the routes from OSPF process 1 into BGP, and matches both internal and external OSPF routes. This way, the engineer can avoid introducing extra routes that are not part of OSPF process 1, such as the default route or the connected routes.Reference: =Designing and Implementing Cloud Connectivity (ENCC) v1.0, [ENCC: Configuring IPsec VPN from Cisco IOS XE to AWS], [Deploying Cisco IOS VTI-Based Point-to-Point IPsec VPNs]
Refer to the exhibits.
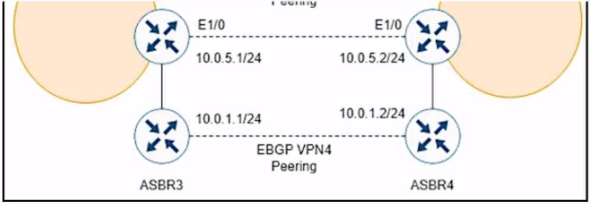
While troubleshooting, a network engineer discovers that the backup path fails between ASBR3 and ASBR4 for traffic between BGP AS6000 and BGP AS6500 when the connection between ASBR1 and ASBR2 goes down. The following configurations were performed on ASBR1:
Which command is missing?
Answer : D
The bgp advertise-best-external command is used to enable the advertisement of the best external path to internal BGP peers. This command is useful when there are multiple exit points from the local AS to other ASes, and the local AS wants to use the closest exit point for each destination. By default, BGP only advertises the best path to its peers, and the best path is usually the one with the lowest IGP metric to the next hop. However, this may not be the optimal path for traffic leaving the local AS, as it may result in suboptimal hot-potato routing or MED oscillations. The bgp advertise-best-external command allows BGP to advertise the best external path, which is the path with the lowest MED among the paths from different neighboring ASes, in addition to the best path. This way, the internal BGP peers can choose the best exit point based on the MED value, rather than the IGP metric. In this scenario, ASBR1 is configured to receive additional paths from ASBR2, which is a route reflector. ASBR2 receives two paths for the same prefix from AS6500, one from ASBR3 and one from ASBR4. ASBR2 selects the best path based on the IGP metric to the next hop, and advertises it to ASBR1. However, this path may not be the best external path, as it may have a higher MED value than the other path. If the connection between ASBR1 and ASBR2 goes down, ASBR1 will not have any backup path to reach AS6500, as it does not know the other path from ASBR4. To prevent this situation, ASBR1 should be configured with the bgp advertise-best-external command, so that it can receive the best external path from ASBR2, along with the best path. This way, ASBR1 will have a backup path to reach AS6500, in case the primary path fails.Reference:=IP Routing: BGP Configuration Guide - BGP Additional Paths ... - Cisco,BGP Additional Paths
Refer to the exhibit.
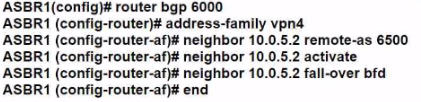
A company uses Cisco SD-WAN in the data center. All devices have the default configuration. An engineer attempts to add a new centralized control policy in Cisco vManage but receives an error message. What is the problem?
Answer : D
The problem is that the site-list ''All-Site'' has a higher match sequence than the site-list ''Hub'', which means that the policy for ''All-Site'' will take precedence over the policy for ''Hub'' for any site that belongs to both lists. This creates a conflict and prevents the engineer from adding a new centralized control policy in Cisco vManage. To resolve this issue, the site-list ''All-Site'' should be configured with a new match sequence that is lower than the sequence for site-list ''Hub'', so that the policy for ''Hub'' will be applied first and then the policy for ''All-Site'' will be applied only to the remaining sites that are not in the ''Hub'' list.Reference:=
Designing and Implementing Cloud Connectivity (ENCC, Track 1 of 5), Module 3: Cisco SD-WAN Cloud OnRamp for Colocation, Lesson 3: Cisco SD-WAN Cloud OnRamp for Colocation - Centralized Control Policies
Cisco SD-WAN Cloud OnRamp for Colocation Deployment Guide, Chapter 4: Configuring Centralized Control Policies
Cisco SD-WAN Configuration Guide, Release 20.3, Chapter: Centralized Policy Framework, Section: Policy Configuration Overview
Refer to the exhibits.
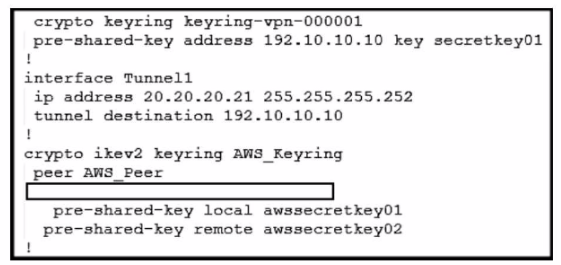
Refer to the exhibit. An engineer needs to configure a site-to-site IPsec VPN connection between an on-premises Cisco IOS XE router and Amazon Web Services (AWS). Which configuration command must be placed in the blank in the code to complete the tunnel configuration?
Answer : C
In the given scenario, an engineer is configuring a site-to-site IPsec VPN connection between an on-premises Cisco IOS XE router and AWS. The correct command to complete the tunnel configuration is ''tunnel source 20.20.20.21''.This command specifies the source IP address for the tunnel, which is essential for establishing a secure connection between two endpoints over the internet or another network1.Reference:
Configure IOS-XE Site-to-Site VPN Connection to Amazon Web Services - Cisco Community
[Security for VPNs with IPsec Configuration Guide, Cisco IOS XE Release 3S - Config
An engineer is implementing a highly secure multitier application in AWS that includes S3. RDS, and some additional private links. What is critical to keep the traffic safe?
Answer : B
A highly secure multitier application in AWS that includes S3, RDS, and some additional private links requires specific routing and bucket policies to keep the traffic safe. The reasons are as follows:
Specific routing policies are needed to ensure that the traffic between the tiers is routed through the private links, which provide secure and low-latency connectivity between AWS services and on-premises resources12.The private links can also prevent the exposure of the data and the application logic to the public internet12.
Bucket policies are needed to control the access to the S3 buckets that store the application data34.Bucket policies can specify the conditions under which the requests are allowed or denied, such as the source IP address, the encryption status, the request time, etc.34.Bucket policies can also enforce encryption in transit and at rest for the data in S334.
1: AWS PrivateLink
2: AWS PrivateLink FAQs
3: Using Bucket Policies and User Policies
4: Bucket Policy Examples
Refer to the exhibit.
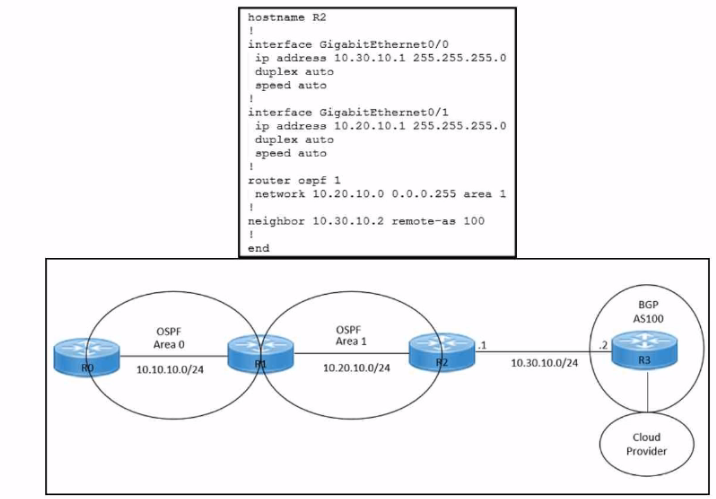
Refer to the exhibits. An engineer must redistribute IBGP routes into OSPF to connect an on-premises network to a cloud provider. Which command must be configured on router R2?
Answer : B
This command redistributes the routes learned from BGP AS100 into OSPF Area 1, which allows router R2 to advertise those routes to router R1 and connect the on-premises network to the cloud provider.The other options are incorrect because they either redistribute the wrong routes or use the wrong syntax5.
I hope this helps you understand the question and the answer. If you have any other questions or requests, please let me know. I am always happy to help.
Refer to the exhibit.
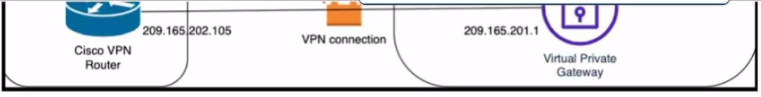
Which Cisco lKEv2 configuration brings up the IPsec tunnel between the remote office router and the AWS virtual private gateway?
A)
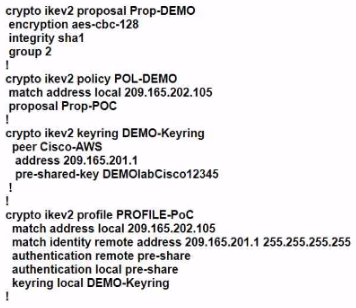
B)
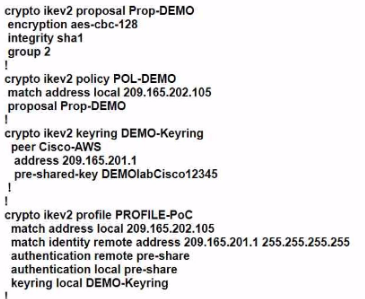
C)
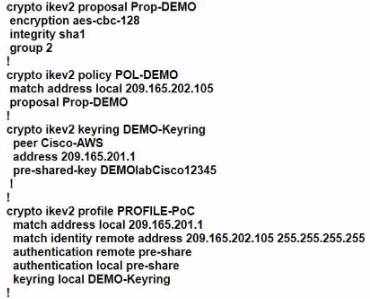
Answer : C
Option C is the correct answer because it configures the IKEv2 profile with the correct match identity, authentication, and keyring parameters. It also configures the IPsec profile with the correct transform set and lifetime parameters. Option A is incorrect because it does not specify the match identity remote address in the IKEv2 profile, which is required to match the AWS virtual private gateway IP address. Option B is incorrect because it does not specify the authentication pre-share in the IKEv2 profile, which is required to authenticate the IKEv2 peers using a pre-shared key.Option C also matches the configuration example provided by AWS1and Cisco2for setting up an IKEv2 IPsec site-to-site VPN between a Cisco IOS-XE router and an AWS virtual private gateway.Reference:=
1: AWS VPN Configuration Guide for Cisco IOS-XE
2: Configure IOS-XE Site-to-Site VPN Connection to Amazon Web Services