Cisco Implementing Cisco Application Centric Infrastructure 300-620 DCACI Exam Questions
Which setting prevents the learning of Endpoint IP addresses whose subnet does not match the bridge domain subnet?
Answer : D
The setting that prevents the learning of Endpoint IP addresses whose subnet does not match the bridge domain subnet is the''Limit IP learning to subnet''setting within the bridge domain1.This setting ensures that only IP addresses belonging to the subnets configured on the bridge domain are learned, preventing mis-learning of IP addresses that may not belong to the fabric1.
Refer to the exhibit.
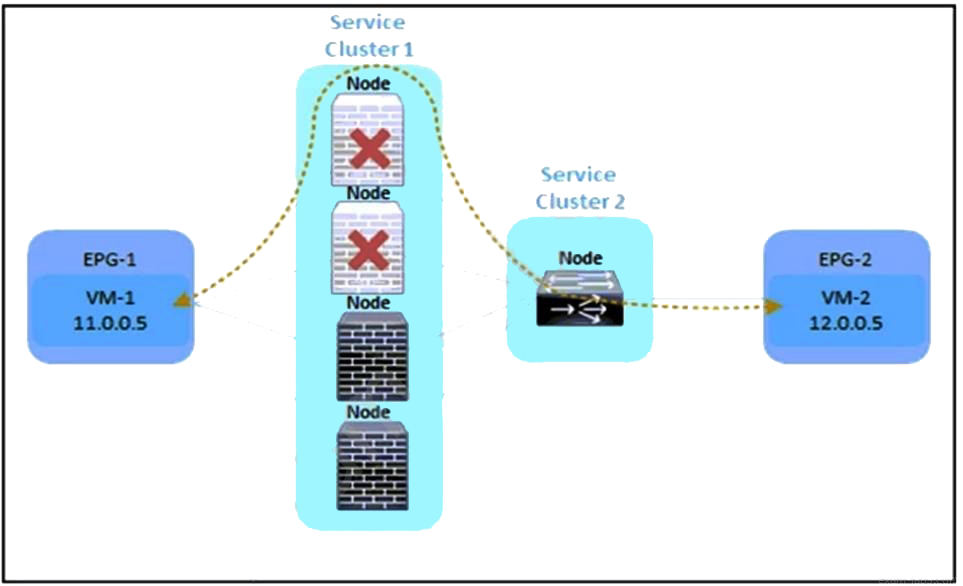
Refer to the exhibit. An engineer must divert the traffic between VM-1 and VM-2 by using a Multi-Node service graph. The solution should prevent an insufficient number of available Layer 4 to Layer 7 devices in the first cluster. Which configuration set accomplishes this goal?
Answer : A
To divert traffic between VM-1 and VM-2 using a Multi-Node service graph while preventing an insufficient number of available Layer 4 to Layer 7 devices in the first cluster, the following configuration set should be used:
PBR node tracking: This feature monitors the health of the nodes (Layer 4 to Layer 7 devices) in the service graph.If a node becomes unavailable, the system can take action based on the tracking threshold1.
Tracking threshold with action bypass: When the number of healthy nodes falls below the tracking threshold, the action 'bypass' ensures that traffic is not sent to the unhealthy nodes, thus preventing service disruption1.
Symmetric PBR: This ensures that return traffic follows the same path as the original traffic, maintaining session consistency and avoiding asymmetric routing issues1.
Resilient hashing: This hashing mechanism provides a consistent and optimal distribution of traffic across the available Layer 4 to Layer 7 devices, even when the number of nodes changes due to a failure or maintenance1.
Cisco APIC Layer 4 to Layer 7 Services Deployment Guide, Release 5.2(x)
Refer to the exhibit.
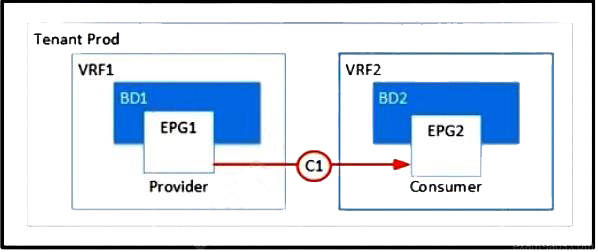
Refer to the exhibit. Which two configurations enable inter-VRF communication? (Choose two.)
Answer : A, C
To enable inter-VRF communication, the following configurations are necessary:
Set the subnet scope to Shared Between VRFs: This allows the subnets to be shared across different VRFs within the same tenant or across tenants, enabling communication between EPGs that are in different VRFs1.
Export the contract and import as a contract interface: By exporting a contract from the provider tenant and importing it as a contract interface in the consumer tenant, you establish a relationship that allows for controlled communication between EPGs in separate VRFs or tenants1.
ACI Inter VRF/Tenant Route Leaking Configuration Example1
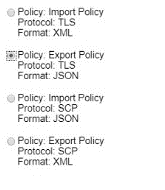
An engineer must securely export Cisco APIC configuration snapshots to a secure, offsite location The exported configuration must be transferred using an encrypted tunnel and encoded with a platform-agnostic data format that provides namespace support Which configuration set must be used?
Answer : B
To securely export Cisco APIC configuration snapshots to a secure, offsite location using an encrypted tunnel and a platform-agnostic data format that provides namespace support, the following configuration set must be used:
Choose a Platform-Agnostic Data Format: Export the configuration in a data format like JSON or XML, which are platform-agnostic and support namespaces1.
Use an Encrypted Tunnel: Transfer the configuration snapshot over a secure protocol such as SFTP or SCP, which provides an encrypted tunnel for the data transfer1.
Schedule the Export: Set up a scheduled export of the configuration in the Cisco APIC to occur at regular intervals, ensuring the process is automated1.
Enable Encryption: Make sure the configuration export policy includes encryption settings.Cisco APIC supports AES-256 encryption for securing exported configuration files2.
Verify Namespace Support: Ensure that the chosen data format and the method of export support the use of namespaces, which are essential for organizing elements and attributes in XML documents1.
By following these steps and choosing Option B, the engineer can meet the requirements for securely exporting Cisco APIC configuration snapshots to an offsite location.
Regarding the MTU value of MP-BGP EVPN control plane packets in Cisco ACI, which statement about communication between spine nodes in different sites is true?
Answer : A
The statement about the MTU value of MP-BGP EVPN control plane packets in Cisco ACI that is true for communication between spine nodes in different sites is that by default, spine nodes generate9000-bytes packetsto exchange endpoints routing information.As a result, the Inter-Site network should be able to carry9000-bytes packets2.This ensures that the control plane traffic, which is not VXLAN encapsulated, can be properly handled across the sites2.
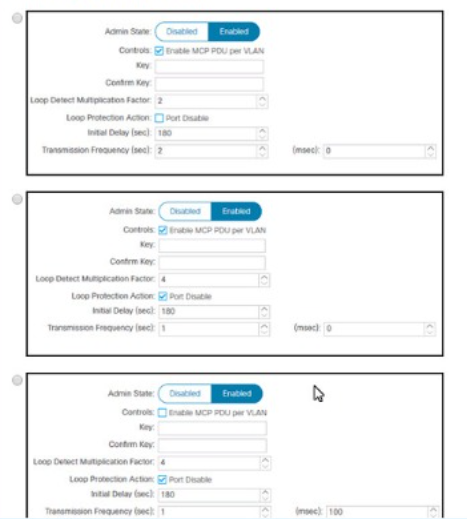
A network engineer must configure a Cisco ACI system to detect network loops for untagged and tagged traffic The loop must be detected and slopped by disabling an interface within 4 seconds Which configuration must be used?
Answer : B
To configure a Cisco ACI system to detect network loops for both untagged and tagged traffic and to stop the loop by disabling an interface within 4 seconds, the following configuration must be used:
Enable Mis-Cabling Protocol (MCP): MCP detects loops from external sources and will err-disable the interface on which Cisco ACI receives its own packet.This is crucial for preventing loops in the network1.
Configure MCP Transmit Frequency: Set the MCP transmit frequency to a value that allows for quick loop detection. The Cisco ACI fabric provides faster loop detection with transmit frequencies from 100 milliseconds to 300 seconds.To meet the requirement of detecting and stopping a loop within 4 seconds, you would set the transmit frequency to a value less than 4 seconds2.
Set Action on Loop Detection: Configure the MCP policies to identify loops and decide how to act upon them.You can set the policy to generate a syslog message or disable the port upon loop detection2.
Implement Error Disabled Recovery Policy: Configure an error disabled recovery policy to automatically re-enable ports that were disabled due to loop detection after a configurable interval2.
By implementing these configurations, the Cisco ACI system will be able to detect and stop network loops quickly and efficiently, ensuring network stability and preventing potential disruptions.
Cisco APIC Online Help - Loop Detection2
Cisco ACI Best Practices Quick Summary
Refer to the exhibit.
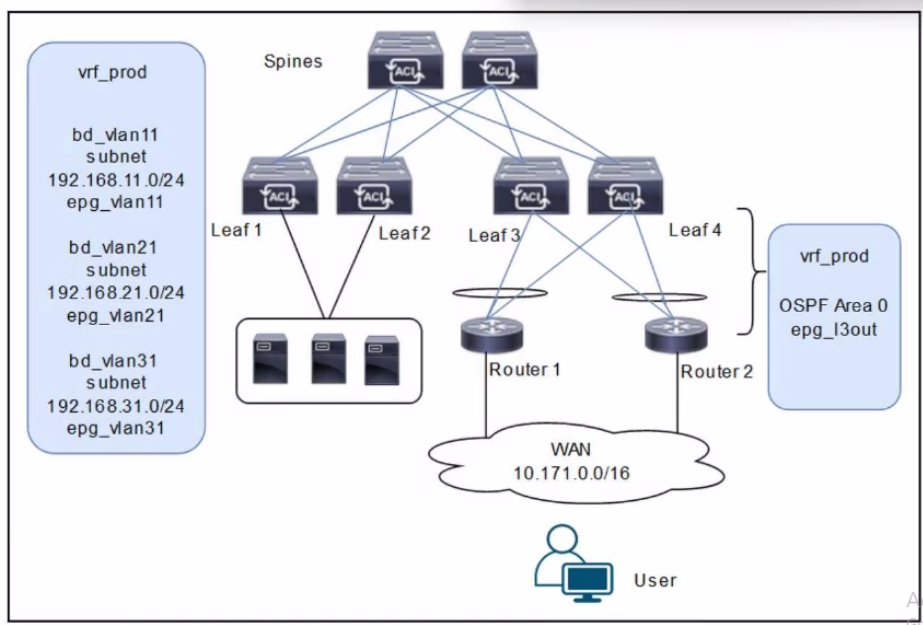
A customer is deploying a WAN with these requirements: *Routers 1 and 2 must receive only routes 192.168.11.0/24 and 192.168.21.0724 from the Cisco ACI fabric *Reachability to the WAN users must be permitted only for the servers that are located in vrf_prod.
Which settings must be configured to meet these objectives?
Answer : D
The scenario involves deploying a WAN with Cisco ACI, where Routers 1 and 2 (connected via an L3Out with OSPF Area 0) must receive specific routes (192.168.11.0/24 and 192.168.21.0/24) from the ACI fabric, and reachability to WAN users must be permitted only for servers in vrf_prod. The diagram shows three bridge domains (bd_vlan11, bd_vlan21, bd_vlan31) with their respective subnets and EPGs, all under vrf_prod, along with an L3Out (epg_l3out) for WAN connectivity.
Requirement Analysis
Routers 1 and 2 must receive only routes 192.168.11.0/24 and 192.168.21.0/24:
These subnets belong to bd_vlan11 and bd_vlan21, respectively. To advertise these routes to Routers 1 and 2 via the L3Out, they must be marked with the appropriate scope in the bridge domain configuration.
In ACI, the 'Advertised Externally' scope on a subnet ensures that it is advertised to external routers via the L3Out routing protocol (OSPF in this case).
Reachability to WAN users must be permitted only for servers in vrf_prod:
This implies that only the subnets in vrf_prod (192.168.11.0/24, 192.168.21.0/24, and 192.168.31.0/24) should be accessible, but WAN users should only reach specific subnets based on policy.
The external EPG (epg_l3out) represents the WAN users (10.171.0.0/16), and its subnet scope must control inbound reachability.
The subnet 192.168.31.0/24 (bd_vlan31) should not be advertised to the WAN, as it is not listed in the routes Routers 1 and 2 should receive.
Option Evaluation
A . Configure the subnets 192.168.11.0/24 and 192.168.21.0/24 as Private to VRF. Configure the subnet 192.168.31.0/24 as Advertised Externally. Configure an EPG subnet 0.0.0.0/0 as External Subnets for External EPG:
Setting 192.168.11.0/24 and 192.168.21.0/24 as 'Private to VRF' means they are not advertised externally, which fails the requirement for Routers 1 and 2 to receive these routes.
Setting 192.168.31.0/24 as 'Advertised Externally' incorrectly advertises this subnet to the WAN, which is not desired.
The 'External Subnets for External EPG' scope on 0.0.0.0/0 allows WAN users to reach all subnets in vrf_prod, which is correct for reachability.
Conclusion: Fails the first requirement (route advertisement).
B . Configure the subnets 192.168.11.0/24 and 192.168.21.0/24 as Private to VRF. Configure the subnet 192.168.31.0/24 as Advertised Externally. Configure an EPG subnet 0.0.0.0/0 as Shared Route Control Subnet:
Similar to Option A, setting 192.168.11.0/24 and 192.168.21.0/24 as 'Private to VRF' prevents their advertisement to the WAN, failing the first requirement.
Setting 192.168.31.0/24 as 'Advertised Externally' incorrectly advertises this subnet.
The 'Shared Route Control Subnet' scope allows route leaking between VRFs, which is irrelevant here since there is only one VRF (vrf_prod) and no route leaking is required.
Conclusion: Fails both requirements (route advertisement and reachability control).
C . Configure the subnets 192.168.11.0/24 and 192.168.21.0/24 as Advertised Externally. Configure the subnet 192.168.31.0/24 as Private to VRF. Configure an EPG subnet 0.0.0.0/0 as Shared Route Control Subnet:
Setting 192.168.11.0/24 and 192.168.21.0/24 as 'Advertised Externally' ensures these subnets are advertised to Routers 1 and 2 via OSPF, meeting the first requirement.
Setting 192.168.31.0/24 as 'Private to VRF' prevents its advertisement to the WAN, which aligns with the requirement since only 192.168.11.0/24 and 192.168.21.0/24 should be advertised.
The 'Shared Route Control Subnet' scope on 0.0.0.0/0 in the external EPG is incorrect for controlling reachability. This scope is used for route leaking, not for defining which subnets are accessible from the external EPG.
Conclusion: Meets the first requirement but fails the second (reachability control).
D . Configure the subnets 192.168.11.0/24 and 192.168.21.0/24 as Advertised Externally. Configure the subnet 192.168.31.0/24 as Private to VRF. Configure an EPG subnet 0.0.0.0/0 as External Subnets for External EPG:
Setting 192.168.11.0/24 and 192.168.21.0/24 as 'Advertised Externally' ensures these subnets are advertised to Routers 1 and 2 via OSPF, meeting the first requirement.
Setting 192.168.31.0/24 as 'Private to VRF' prevents its advertisement to the WAN, which is correct since only the specified subnets should be advertised.
The 'External Subnets for External EPG' scope on 0.0.0.0/0 in the external EPG (epg_l3out) allows WAN users (10.171.0.0/16) to reach all subnets in vrf_prod, which includes 192.168.11.0/24, 192.168.21.0/24, and 192.168.31.0/24. This satisfies the second requirement, as servers in vrf_prod are accessible, and contracts can further restrict access if needed (though not specified in the question).
Conclusion: Meets both requirements (route advertisement and reachability).
Final Answer Justification
D is correct because:
It ensures that only 192.168.11.0/24 and 192.168.21.0/24 are advertised to Routers 1 and 2 by setting their scope to 'Advertised Externally.'
It keeps 192.168.31.0/24 private to vrf_prod by setting its scope to 'Private to VRF.'
It allows WAN users to reach all vrf_prod subnets (including servers) by setting 0.0.0.0/0 as 'External Subnets for External EPG,' fulfilling the reachability requirement.
Primary Cisco Reference:
Cisco APIC Layer 3 Configuration Guide, 'Configuring Subnets for L3Out.'
Cisco ACI Routing and Forwarding Guide, 'External EPG and Subnet Scopes.'
Cisco ACI Best Practices, 'Controlling Route Advertisement and Reachability.'