Cisco Designing and Implementing Secure Cloud Access for Users and Endpoints 300-740 SCAZT Exam Questions
Refer to the exhibit.
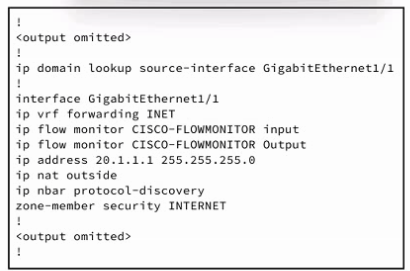
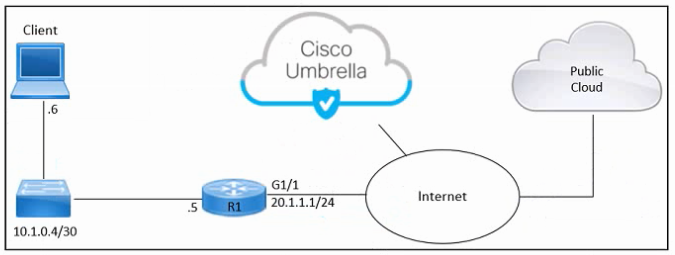
Refer to the exhibit. An engineer must connect an on-premises network to the public cloud using Cisco Umbrella as a Cloud Access Security Broker. The indicated configuration was applied to router R1; however, connectivity to Umbrella fails with this error: %OPENDNS-3-DNS_RES_FAILURE. Which action must be taken on R1 to enable the connection?
Answer : B
Refer to the exhibit.
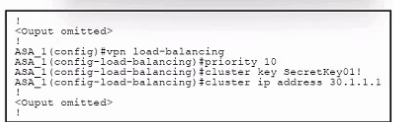
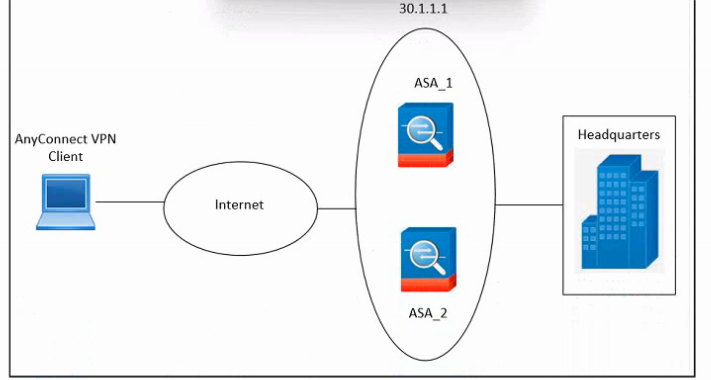
Refer to the exhibit. An engineer must configure VPN load balancing across two Cisco AS
Answer : B, E
An engineer configures trusted endpoints with Active Directory with Device Health to determine if an endpoint complies with the policy posture. After a week, an alert is received by one user, reporting problems accessing an application. When the engineer verifies the authentication report, this error is found:
"Endpoint is not trusted because Cisco Secure Endpoint check failed, Check user's endpoint in Cisco Secure Endpoint."
Which action must the engineer take to permit access to the application again?
Answer : D
Refer to the exhibit.
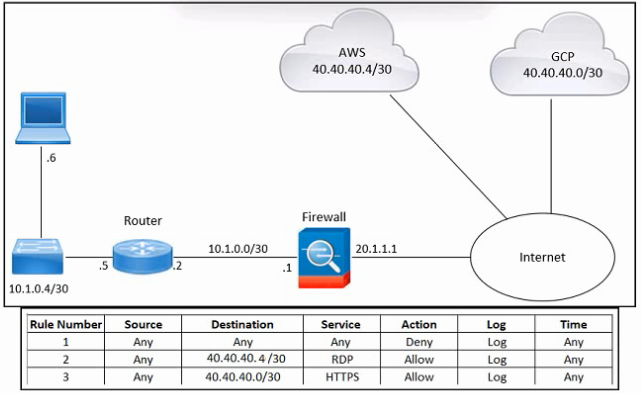
Refer to the exhibit. An engineer must provide RDP access to the AWS virtual machines and HTTPS access to the Google Cloud Platform virtual machines. All other connectivity must be blocked. The indicated rules were applied to the firewall; however, none of the virtual machines in AWS and Google Cloud Platform are accessible. What should be done to meet the requirement?
Answer : A
According to the MITRE ATT&CK framework, which approach should be used to mitigate exploitation risks?
Answer : B
Refer to the exhibit.
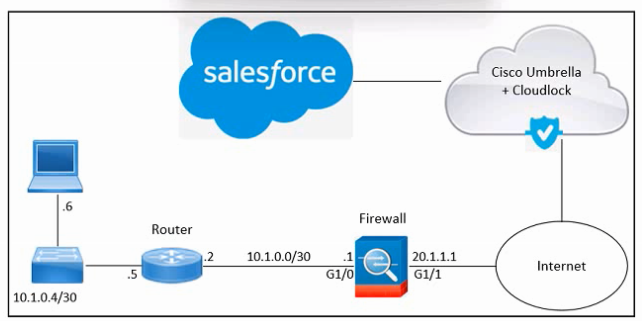
Refer to the exhibit. An engineer must enable access to Salesforce using Cisco Umbrella and Cisco Cloudlock. These actions were performed:
From Salesforce, add the Cloudlock IP address to the allow list
From Cloudlock, authorize Salesforce
However, Salesforce access via Cloudlock is still unauthorized. What should be done to meet the requirements?
Answer : A
Refer to the exhibit.
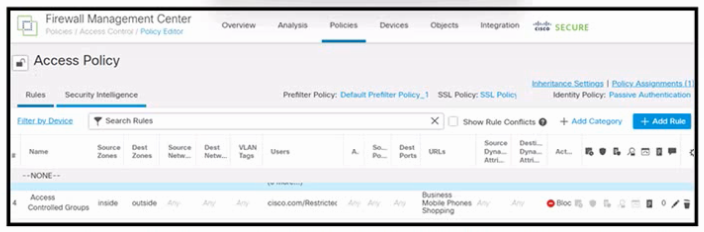
Refer to the exhibit. An engineer must create a policy in Cisco Secure Firewall Management Center to prevent restricted users from being able to browse any business or mobile phone shopping websites. The indicated policy was applied; however, the restricted users still can browse on the mobile phone shopping websites during business hours. What should be done to meet the requirement?
Answer : D