Cisco Implementing and Operating Cisco Wireless Core Technologies 350-101 WLCOR Exam Questions
Refer to the exhibit.
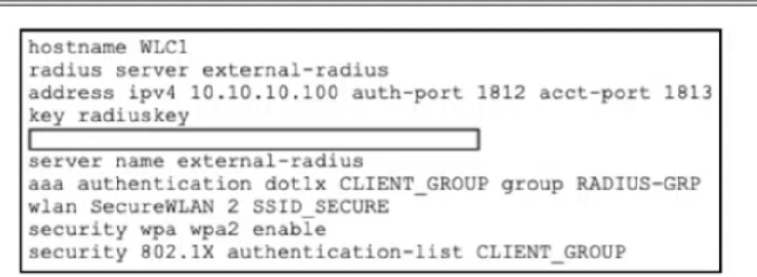
A network administrator is working on a WLC to enable user access for contractor desktops using WPA2-Enterprise using EAP-TTLS. The administrator verified the external authentication configuration and now must test network connectivity. Which code snippet must be added to the box in the code to complete the configuration on the WLC that supports authentication with an external server?
Answer : A
The missing command must create the RADIUS server group context before the existing server name external-radius command can bind the defined RADIUS server into that group. Cisco's Catalyst 9800 802.1X configuration workflow shows the exact CLI sequence: define the RADIUS server, then enter aaa group server radius <radius-grp-name>, then add server name <radius-server-name>. The Catalyst 9800 configuration guide likewise states that the RADIUS server-group identification is created with aaa group server radius server-group, followed by the server name assignment.
In this exhibit, external-radius is already declared under radius server, and aaa authentication dot1x CLIENT_GROUP group RADIUS-GRP already points the 802.1X method list to the server group named RADIUS-GRP. Therefore, the box must contain aaa group server radius RADIUS-GRP so that server name external-radius is syntactically valid and functionally associates the external server with the group. Cisco also identifies dot1x authentication lists as the AAA method type used for 802.1X SSIDs, with ''group'' directing authentication to an external RADIUS server. Reference topics: Client Connectivity Configuration --- WPA2-Enterprise, 802.1X/EAP, AAA method lists, RADIUS server groups, and Catalyst 9800 WLAN security
Refer to the exhibit.
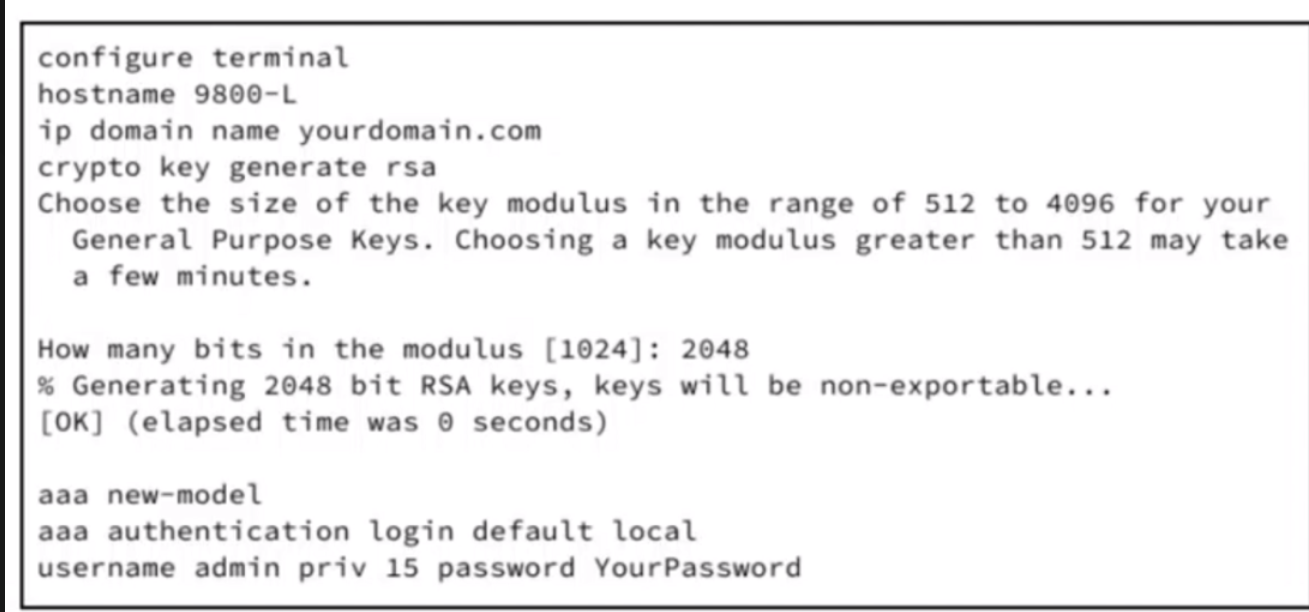
Refer to the exhibit. An engineer is preparing a Cisco 9800-L WLC for deployment in a sensitive area. Only encrypted remote management via SSH is allowed, and all other VTY access methods must be disabled. The 9800-L WLC will be part of a larger deployment, and an external audit will check for any unencrypted management protocols. According to the requirements, only SSH is allowed for remote CLI sessions. Which set of commands must be executed to complete the Cisco IOS XE CLI configuration on the WLC?
Answer : C
The correct configuration is option C because Cisco IOS XE restricts inbound protocols on VTY lines with the transport input command. Cisco's Catalyst 9800 best-practice guidance states that administrators should confirm SSH is enabled and Telnet is disabled for better controller security, and that the Catalyst 9800 follows standard Cisco IOS XE behavior for enabling or disabling Telnet and SSH. Cisco IOS XE SSH documentation explicitly shows line vty line_number [ending_line_number] followed by transport input ssh, and explains that this prevents non-SSH Telnet connections, limiting access to SSH only.
The existing exhibit already includes the SSH prerequisites: hostname, domain name, RSA key generation, AAA new-model, a default login method using local credentials, and a local privileged user. The missing VTY configuration must therefore apply that default AAA login list to the VTY lines with login authentication default and restrict inbound transport to SSH. Cisco AAA documentation confirms that login authentication default applies the configured default authentication list to the line or set of lines. Option A is incomplete and does not explicitly permit SSH. Option B uses invalid syntax. Option D omits the required input keyword. Reference topics: Catalyst 9800 secure management, VTY access control, SSH, Telnet hardening, AAA login authentication, and IOS XE device administration.
A business is deploying Cisco Catalyst 9100 APs managed by Catalyst 9800 WLCs. The IT team needs policies that adapt based on user identity and device posture and also provide visibility into device activity and location. Which configuration meets these requirements?
Answer : A
To enforce adaptive policies based on user identity, device posture, and provide comprehensive visibility into device activity and location, Cisco recommends integrating Cisco Catalyst Center, Cisco ISE, and Cisco Spaces. Cisco ISE provides identity-based access control and posture assessment, allowing dynamic policy enforcement for users and devices. Mobile device management integration further extends posture checks for endpoint compliance. Cisco Catalyst Center enables real-time assurance and monitoring of network performance, device activity, and service health, while Cisco Spaces provides location analytics and visibility of client devices across the wireless environment. Option B relies solely on ACLs and MDM, which cannot provide full network-wide visibility or context-aware policy enforcement. Option C enables visibility via Catalyst Center but lacks dynamic identity and posture-based policies because it omits ISE integration. Option D integrates ISE but neglects device posture and location visibility, failing to meet all requirements. The combination in Option A ensures that adaptive policies can respond to real-time user and device conditions, enforce compliance, and provide actionable insights for network operations. Reference topics: Wireless Monitoring and Management --- Catalyst Center assurance, Cisco ISE integration, mobile device posture, Cisco Spaces location analytics.
What happens when a radio wave bends around objects?
Answer : D
When a radio wave bends around an obstacle in its path, this phenomenon is called diffraction. Diffraction allows the RF signal to reach areas that are not in the direct line of sight of the transmitter, such as behind walls, corners, or other obstructions. The amount of bending depends on the wavelength of the signal relative to the size of the obstacle---longer wavelengths (lower frequencies) diffract more effectively than shorter wavelengths.
This property is crucial in wireless network design, especially in enterprise or mesh deployments, because it enables coverage in complex indoor environments and around obstructions where direct line-of-sight communication is impossible. Diffraction differs from other RF phenomena: absorption (option A) occurs when RF energy is partially absorbed by materials, reducing signal strength; diffusion (option B) refers to scattering of the signal in multiple directions; and reflection (option C) occurs when RF waves bounce off surfaces like walls or ceilings, which can lead to multipath interference.
Cisco wireless design guides emphasize understanding diffraction for coverage planning, AP placement, and optimizing signal propagation in indoor and campus deployments, ensuring that signals can adequately reach shadowed or obstructed areas without excessive loss or dead spots. Reference topic: RF Fundamentals --- diffraction, reflection, absorption, and indoor wireless propagation.
A network engineer must isolate all guest users connected to the WLAN on a Cisco 9800 WLC so they cannot communicate with each other but can access the internet. The WLAN must meet these requirements:
*SSID named VisitorAccess assigned to VLAN 30
*guests prohibited from sharing files with other guests
*must be scalable to multiple access points in the building
Which action must the network engineer take to meet the requirements?
Answer : A
The requirement is guest client isolation, not merely guest authentication or internet breakout. On a Catalyst 9800 WLC, peer-to-peer blocking is the correct control because it prevents wireless clients associated to the same WLAN from communicating directly with one another. Cisco defines peer-to-peer blocking as a WLAN security feature applied to individual WLANs, where each client inherits the WLAN's P2P blocking behavior, and traffic can be bridged locally, dropped, or forwarded upstream. For this scenario, the appropriate action is the drop behavior, because guest-to-guest file sharing must be prohibited while upstream internet access remains available.
The dedicated guest VLAN, VLAN 30, provides traffic segmentation from production networks and creates a clean policy boundary for VisitorAccess. Cisco's Catalyst 9800 configuration model maps WLANs to policy profiles, and the policy profile defines client network and switching policy, including VLAN association. Options B, C, and D do not solve client isolation: local authentication validates users, FlexConnect/local switching changes traffic forwarding behavior, and multicast/RADIUS does not block unicast guest-to-guest traffic. Reference topics: Client Connectivity Configuration --- guest WLAN design, P2P blocking, VLAN segmentation, and Catalyst 9800 WLAN-to-policy mapping.
Refer to the exhibit.
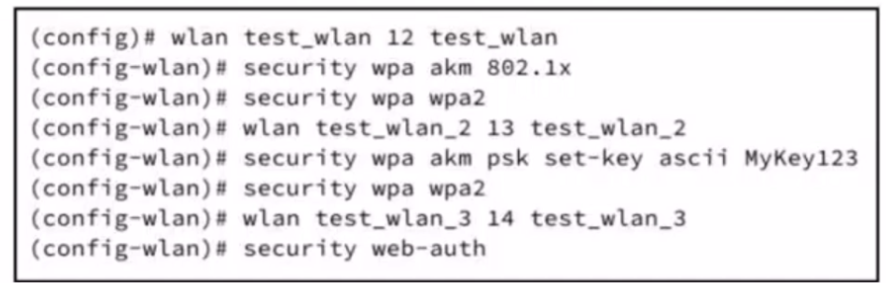
A wireless controller is deployed at a branch location to facilitate secure client connectivity. A network engineer configures one WLAN using WPA2 Personal authentication and activates the preshared key method to align with company security policies. Which action must be taken to enable the client to connect to the WLAN?
Answer : A
WPA2 Personal (PSK) authentication relies on a shared secret (preshared key) configured on both the wireless LAN controller (WLC) and the client device. In the exhibit, the WLAN is configured with WPA2 and PSK (set-key ascii MyKey123), which means the network expects clients to use the same preshared key to authenticate. To enable client connectivity, the preshared key must be manually entered on each client device; this aligns the client and WLC authentication parameters. Options B, C, and D are unrelated to WPA2 Personal: MAC filtering is a security policy mechanism, Active Directory integration supports WPA2 Enterprise with 802.1X authentication, and client certificates are used for certificate-based EAP methods, not PSK. Cisco Wireless Core Technologies emphasize that PSK deployments require consistent key configuration across the WLAN and clients, and that the preshared key is the critical element for successful authentication. This ensures secure, encrypted communication while providing simple setup for small or branch deployments without an enterprise RADIUS infrastructure. Reference topics: Client Connectivity Configuration --- WPA2 Personal, preshared key authentication, WLAN configuration, branch deployment WLAN security.
To double the range of a transmitter, which value must the transmitter be changed to if it is currently at 17 dBm?
Answer : B
Doubling the range of a wireless transmitter does not require a linear increase in power due to the inverse-square law of RF propagation. Free-space path loss (FSPL) increases with the square of the distance, meaning to double the distance, the required power must increase by a factor of four in linear terms. In decibel units, power increases are logarithmic: 10log10(4)610 \log_{10}(4) \approx 610log10(4)6 dB.
Given a transmitter at 17 dBm, increasing its output by 6 dB to 23 dBm would theoretically double the coverage in free-space conditions. However, due to environmental factors like multipath, absorption, and antenna efficiency, Cisco RF design guides often round to practical increments, suggesting an increase from 17 dBm to 27 dBm to achieve a robust doubling of coverage under real-world conditions.
Options A (20 dBm) and D (17 dBm) are insufficient because they do not provide the necessary power increase to overcome the logarithmic path loss for doubling range. Option C (100 dBm) is unrealistic and exceeds regulatory limits for enterprise wireless deployments. Proper power planning must balance coverage, interference, and regulatory compliance. Reference topic: RF Fundamentals --- Free-space path loss, power control, and transmitter range planning in enterprise WLAN design.