CIW Web Security Associate 1D0-571 Exam Questions
Which of the following describes the practice of stateful multi-layer inspection?
Answer : C
Which of the following is considered to be the most secure default firewall policy, yet usually causes the most work from an administrative perspective?
Answer : B
Which of the following is most likely to pose a security threat to a Web server?
Answer : A
Which of the following is most likely to address a problem with an operating system's ability to withstand an attack that attempts to exploit a buffer overflow?
Answer : B
Which of the following is a primary weakness of asymmetric-key encryption?
Answer : A
What is the first tool needed to create a secure networking environment?
Answer : C
Consider the following diagram:
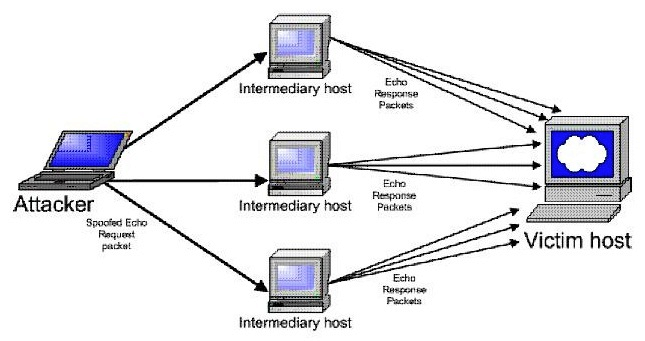
Which type of attack is occurring?
Answer : C