CompTIA SecurityX Certification Exam CAS-005 Practice Questions
A security architect for a global organization with a distributed workforce recently received funding lo deploy a CASB solution Which of the following most likely explains the choice to use a proxy-based CASB?
Answer : A
A proxy-based Cloud Access Security Broker (CASB) is chosen primarily for its ability to block unapproved applications and services. Here's why:
Application and Service Control: Proxy-based CASBs can monitor and control the use of applications and services by inspecting traffic as it passes through the proxy. This allows the organization to enforce policies that block unapproved applications and services, ensuring compliance with security policies.
Visibility and Monitoring: By routing traffic through the proxy, the CASB can provide detailed visibility into user activities and data flows, enabling better monitoring and threat detection.
Real-Time Protection: Proxy-based CASBs can provide real-time protection against threats by analyzing and controlling traffic before it reaches the end user, thus preventing the use of risky applications and services.
CompTIA Security+ SY0-601 Study Guide by Mike Chapple and David Seidl
NIST Special Publication 800-125: Guide to Security for Full Virtualization Technologies
Gartner CASB Market Guide
As part of a security audit in the software development life cycle, a product manager must demonstrate and provide evidence of a complete representation of the code and modules used within the production-deployed application prior to the build. Which of the following best provides the required evidence?
Answer : A
Software Composition Analysis (SCA) is the best method for identifying all components, dependencies, and open-source libraries used inan application. It ensures that organizations track and manage vulnerabilities in third-party code before deployment.
SCA tools generate a Software Bill of Materials (SBOM), which provides a full representation of the code and modules used in the application.
Other options:
Static Application Security Testing (SAST) (C) checks for vulnerabilities but does not map dependencies.
Interactive Application Security Testing (IAST) (D) works at runtime, not before deployment.
Runtime Application Self-Protection (RASP) (B) works while the application is running.
A company designs policies and procedures for hardening containers deployed in the production environment. However, a security assessment reveals that deployed containers are not complying with the security baseline. Which of the following solutions best addresses this issue throughout early life-cycle stages?
Answer : C
SecurityX CAS-005 secure DevOps guidance recommends integrating security controls into the CI/CD pipeline. By validating container security baselines at security gates before deployment, noncompliant builds are stopped early, ensuring consistency across environments.
Option B is useful but does not ensure compliance if changes are made after image creation.
Option A detects drift but only after deployment.
Option D is reactive and does not prevent insecure deployments.
A company SIEM collects information about the log sources. Given the following report information:
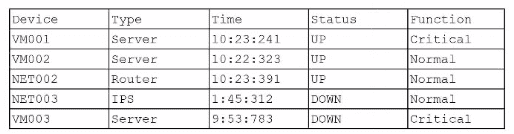
Which of the following actions should a security engineer take to enhance the security monitoring posture?
Answer : C
The SIEM report shows that some devices, such as VM003 (Critical server) and NET003 (IPS), are DOWN and therefore not reporting logs. In security monitoring, the absence of log data from critical systems creates dangerous blind spots. If logs are missing, attacks can proceed undetected, or investigations may lack the data needed for incident response.
The most effective action is to perform a non-reporting device assessment (C). This means identifying and correcting issues where devices fail to send logs, whether due to outages, misconfigurations, or integration gaps. Ensuring all critical devices, especially servers and intrusion prevention systems, consistently send logs to the SIEM strengthens overall visibility and monitoring posture.
Option A (time calibration) is important for correlation accuracy but does not address missing log feeds. Option B (centralized use case library) enhances detection but only works if the SIEM is receiving complete data. Option D (resiliency plan) helps protect log retention but is irrelevant if logs are never received in the first place.
Therefore, fixing non-reporting log sources is the highest priority to improve monitoring effectiveness.
An organization is looking for gaps in its detection capabilities based on the APTs that may target the industry Which of the following should the security analyst use to perform threatmodeling?
Answer : D
The ATT&CK (Adversarial Tactics, Techniques, and Common Knowledge) framework is the best tool for a security analyst to use for threat modeling when looking for gaps in detection capabilities based on Advanced Persistent Threats (APTs) that may target the industry. Here's why:
Comprehensive Framework: ATT&CK provides a detailed and structured repository of known adversary tactics and techniques based on real-world observations. It helps organizations understand how attackers operate and what techniques they might use.
Gap Analysis: By mapping existing security controls against the ATT&CK matrix, analysts can identify which tactics and techniques are not adequately covered by current detection and mitigation measures.
Industry Relevance: The ATT&CK framework is continuously updated with the latest threat intelligence, making it highly relevant for industries facing APT threats. It provides insights into specific APT groups and their preferred methods of attack.
CompTIA Security+ SY0-601 Study Guide by Mike Chapple and David Seidl
MITRE ATT&CK Framework Official Documentation
NIST Special Publication 800-150: Guide to Cyber Threat Information Sharing
Which of the following best describes the reason PQC preparation is important?
Answer : A
Post-Quantum Cryptography (PQC) preparation is critical to protect data against future quantum computing attacks that could break current cryptographic algorithms (e.g., RSA, ECC). According to the CompTIA SecurityX CAS-005 study guide (Domain 3: Cybersecurity Technology, 3.3), quantum computers with sufficient computational power could perform calculations (e.g., Shor's algorithm) to decrypt data protected by traditional algorithms. PQC focuses on developing algorithms resistant to such increases in computational resources, ensuring long-term data security.
Option B:Key stretching is a technique to strengthen passwords, not related to PQC.
Option C:PQC algorithms often have higher computational costs, not improved performance.
Option D:Asymmetric encryption is not ideal for large data sets, and PQC is not specifically about this use case.
Option A:This accurately describes PQC's purpose to safeguard data against quantum-driven decryption.
CompTIA SecurityX CAS-005 Official Study Guide, Domain 3: Cybersecurity Technology, Section 3.3: 'Prepare for post-quantum cryptography challenges.'
CAS-005 Exam Objectives, 3.3: 'Evaluate the need for PQC in response to quantum computing advancements.'
While investigating a security event an analyst finds evidence that a user opened an email attachment from an unknown source. Shortly after the user opened the attachment, a group of servers experienced a large amount of network and resource activity. Upon investigating the servers, the analyst discovers the servers were encrypted by ransomware that is demanding payment within 48 hours or all data will be destroyed. The company has no response plans for ransomware. Which of the following is the next step the analyst should take after reporting the incident to the management team?
Answer : B
The immediate action after discovering ransomware is toisolate the affected serversto prevent further spread of the malware to other systems in the network. Paying the ransom is not recommended as it does not guarantee data recovery and encourages criminal behavior. Notifying law enforcement is necessary, but containment must happen first to limit damage. Requesting server restoration should only occur after containment and a thorough investigation to ensure no remnants of ransomware remain.