CompTIA SecurityX Certification Exam CAS-005 Practice Questions
A company recently acquired a manufacturing plant. The acquiring company plans to create a unified network that does not impact its security posture. The manufacturing plant has been in operation for more than 30 years and has not followed an equipment replacement life cycle. Which of the following is the best way to meet this objective?
Answer : B
The best answer is B. Extending an SD-WAN with specific policies because the question asks for a way to create a unified network while not weakening the acquiring company's security posture. In CompTIA SecurityX CAS-005, SD-WAN is explicitly part of Security Architecture, under ''Deperimeterization: SASE, SD-WAN, and software-defined networking.'' The same official objective set also lists ''Network architecture: segmentation, microsegmentation, VPN...'' and ''Security boundaries... secure zones.'' Those objective areas support a policy-based integration approach in which the plant can be connected while maintaining segmentation, security zones, and centralized enforcement.
This is especially important because the manufacturing plant is old and has not followed an equipment refresh life cycle. That strongly suggests there may be legacy systems, operational technology, and devices that cannot be rapidly modernized or patched. A policy-driven SD-WAN design is more effective than simply connecting the site because it allows the acquiring company to preserve trust boundaries and apply differentiated controls to plant traffic. That aligns directly with CompTIA's official SecurityX emphasis on segmentation, secure zones, and deperimeterization technologies.
Why the other options are not the best choice:
A is not best because a WAF protects web applications, not an entire acquired manufacturing environment, and the scenario does not say the core issue is a web application stack. Also, ''patching the legacy IT equipment'' is unrealistic in a plant with decades-old infrastructure and does not answer the requirement for a unified but controlled network design. C is weaker because a site-to-site VPN provides connectivity and SIEM provides visibility, but neither by itself gives the same policy-based segmentation and architectural control as SD-WAN. D is too narrow because a proxy server does not solve full-site network integration or architecture-wide posture management.
CompTIA SecurityX (CAS-005) official certification page and exam objectives summary, especially Security Architecture domains covering SD-WAN, segmentation, VPN, and secure zones.
===========
A security engineer wants to enhance the security posture of end-user systems in a Zero Trust environment. Given the following requirements:
. Reduce the ability for potentially compromised endpoints to contact command-and-control infrastructure.
. Track the requests that the malware makes to the IPs.
. Avoid the download of additional payloads.
Which of the following should the engineer deploy to meet these requirements?
Answer : A
Which of the following includes best practices for validating perimeter firewall configurations?
Answer : A
The Center for Internet Security (CIS) Controls provide prescriptive best practices for validating and securing perimeter firewalls. These controls are specifically designed to offer detailed, actionable steps that organizations can follow to ensure firewall rules are configured properly, access is restricted to least privilege, and unnecessary services are disabled. CIS benchmarks also provide specific configuration guidance for different vendors, making them highly practical for real-world implementation and validation.
MITRE ATT&CK (B) is a framework for adversary tactics, techniques, and procedures, valuable for threat modeling but not a direct standard for firewall validation. NIST CSF (C) provides a high-level framework for cybersecurity risk management but lacks specific configuration guidance for firewalls. ISO 27001 (D) defines an information security management system (ISMS) framework, focusing on governance and certification rather than hands-on configuration best practices.
Therefore, the CIS Controls and Benchmarks represent the most direct and practical resource for validating firewall configurations in line with recognized industry best practices.
A building camera is remotely accessed and disabled from the remote console application during off-hours. A security analyst reviews the following logs:
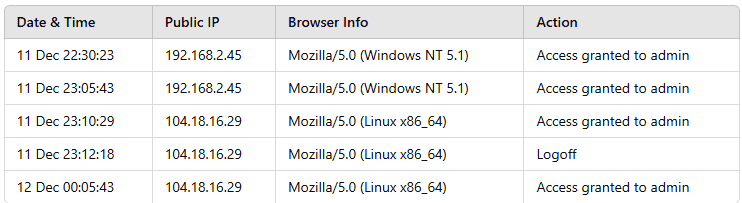
Which of the following actions should the analyst take to best mitigate the threat?
Answer : C
The logs indicate unauthorized access from104.18.16.29, an external IP, to the building camera's administrative console during off-hours.Restricting access only to approved IPsensures that only authorized personnel can remotely control the cameras, reducing the risk of unauthorized access and manipulation.
Implementing WAF protection (A)secures against web application attacks but does not restrict unauthorized administrative access.
Upgrading the firmware (B)is good security hygiene but does not immediately mitigate the active threat.
Blocking IP 104.18.16.29 (D)is a temporary measure, as an attacker can switch to another IP. A better long-term solution is whitelisting trusted IPs.
A penetration tester reviews the following router configuration:
set-system services ssh root login-allow
set-system services web-management https allow
set-system services syslog file interactive
set-system services log mode stream
set-interfaces 0 family inet address 10.12.14.1/8
Which of the following changes is the best way to enhance security?
Answer : C
The best answer is C. Enabling network segmentation controls. The most obvious security weakness shown in the configuration is the interface address 10.12.14.1/8, which places the device in an extremely broad network range instead of a tightly bounded segment. From a SecurityX perspective, the strongest improvement is to reduce unnecessary trust exposure by applying segmentation and tighter network boundaries. CompTIA's official SecurityX objectives explicitly call out ''Network architecture: segmentation, microsegmentation, virtual local area networks (VLANs), virtual routing and forwarding (VRF), software-defined networking (SDN)'' and also emphasize ''Security boundaries: secure zones, access control lists (ACLs), virtual private network (VPN)'' under Security Architecture.
Why the other options are not the best choice:
A may improve cryptographic strength, but the configuration already shows SSH and HTTPS, so encrypted management access is already present. B is not the best answer because no unencrypted terminal service such as Telnet is shown in the configuration. D is generally useful operationally, but automatic patching and rebooting is not the main architectural weakness indicated by the config excerpt. The clearest risk visible in the router snippet is inadequate network scoping and boundary control, which points to segmentation as the best improvement.
CompTIA SecurityX official exam objectives summary, Security Architecture domain.
CompTIA SecurityX CAS-005 exam objectives PDF mirror containing the domain details for segmentation and security boundaries.
===========
A security analyst is reviewingsuspicious log-in activity and sees the following data in the SICM:
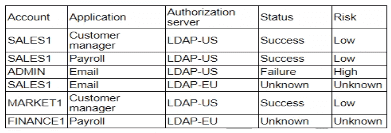
Which of the following is the most appropriate action for the analyst to take?
Answer : D
The log-in activity indicates a security threat, particularly involving the ADMIN account with a high-risk failure status. This suggests that the account may be targeted by malicious activities such as credential stuffing or brute force attacks.
Updating log configuration settings (A) may help in better logging future activities but does not address the immediate threat.
Changing the admin account password (B) is a good practice but may not fully mitigate the ongoing threat if the account has already been compromised.
Blocking employees (C) from logging into non-business applications might help in reducing attack surfaces but doesn't directly address the compromised account issue.
Implementing automation to disable accounts associated with high-risk activities ensures an immediate response to the detected threat, preventing further unauthorized access and allowing time for thorough investigation and remediation.
CompTIA SecurityX guide on incident response and account management.
Best practices for handling compromised accounts.
Automation tools and techniques for security operations centers (SOCs).
A company experienced a data breach, resulting in the disclosure of extremely sensitive data regarding a merger. As a regulated entity, the company must comply with reporting and disclosure requirements. The company is concerned about its public image and shareholder values. Which of the following best supports the organization in addressing its concerns?
Answer : D
A crisis management plan defines coordinated communication and response strategies for high-profile incidents that may harm an organization's public reputation and shareholder confidence. CAS-005 GRC content includes crisis communication planning for regulatory compliance and public relations in the wake of breaches.
A Data Subject Access Request (A) addresses individual data rights, not overall crisis handling.
Business Impact Analysis (B) helps assess potential operational and financial impacts but does not manage public perception during an incident.
Supply chain management (C) is preventative for vendor risks, not responsive to current crises.