CompTIA Data+ Exam (2025) DA0-002 Practice Questions
Which of the following is the most efficient to use when programming repeatable tasks?
Answer : D
This question pertains to the Data Acquisition and Preparation domain, focusing on tools for automating repeatable tasks in data processes. The task is to identify the most efficient programming method.
LLM (Option A): Large Language Models (e.g., GPT) are for text generation, not efficient for repeatable data tasks.
Deep learning (Option B): Deep learning is for complex pattern recognition (e.g., image classification), not efficient for simple repeatable tasks.
NLP (Option C): Natural Language Processing is for text analysis, not general repeatable tasks.
RPA (Option D): Robotic Process Automation (RPA) automates repetitive, rule-based tasks (e.g., data entry, file processing), making it the most efficient for programming repeatable tasks.
The DA0-002 Data Acquisition and Preparation domain includes 'executing data manipulation,' and RPA is a widely used method for automating repeatable data tasks.
==============
A data analyst needs to create a report that anticipates the number of calls received daily. Which of the following is the best statistical method to use?
Answer : A
This question falls under the Data Analysis domain, focusing on statistical methods for forecasting. The task is to anticipate (predict) the number of daily calls, which involves looking into the future.
Predictive (Option A): Predictive analytics uses historical data to forecast future outcomes (e.g., number of calls), which matches the requirement.
Diagnostic (Option B): Diagnostic analytics identifies causes and patterns in historical data, not future predictions.
Inferential (Option C): Inferential statistics make generalizations about a population, not specific forecasts.
Descriptive (Option D): Descriptive analytics summarizes past data, not suitable for anticipating future values.
The DA0-002 Data Analysis domain includes 'applying the appropriate descriptive statistical methods,' and predictive analytics is the best method for forecasting future call volumes.
==============
An administrator needs to design a table that will include foreign words. Which of the following is the best option for storing non-native language characters?
Answer : B
This question falls under the Data Concepts and Environments domain, focusing on selecting appropriate data types for storing specific kinds of data. The task requires storing foreign words, which often include non-native characters (e.g., accents, Unicode characters).
VARCHAR (Option A): VARCHAR stores variable-length strings but typically uses ASCII or single-byte encoding, which may not support all foreign characters.
NVARCHAR (Option B): NVARCHAR (National VARCHAR) stores variable-length strings in Unicode, supporting a wide range of non-native characters, making it the best choice.
CLOB (Option C): CLOB (Character Large Object) is for large text data, but it's overkill for most foreign words and not specifically designed for Unicode.
CHAR (Option D): CHAR stores fixed-length strings, but like VARCHAR, it often uses single-byte encoding, which may not support foreign characters.
The DA0-002 Data Concepts and Environments domain includes understanding 'data schemas and dimensions,' such as selecting data types like NVARCHAR for Unicode support.
==============
A data analyst wants to find the mean score that students received in science classes. Given the following tables:
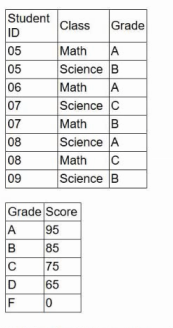
Which of the following will produce the desired results?
Answer : A
A user needs a report that shows the main causes of customer churn rate in a three-year period. Which of the following methods provides this information?
Answer : B
This question falls under the Data Analysis domain, focusing on analytical methods for reporting. The task is to identify the causes of customer churn over three years, which involves analyzing historical data.
Inferential (Option A): Inferential statistics make predictions or generalizations about a population, not focused on identifying causes in historical data.
Descriptive (Option B): Descriptive analytics summarizes historical data to identify patterns and causes (e.g., reasons for churn), which fits the task.
Prescriptive (Option C): Prescriptive analytics provides recommendations, which goes beyond identifying causes.
Predictive (Option D): Predictive analytics forecasts future outcomes, not focused on historical causes.
The DA0-002 Data Analysis domain includes 'applying the appropriate descriptive statistical methods,' and descriptive analytics is best for identifying causes in historical data.
==============
A data analyst needs to remove all duplicate values between two tables, "Employees" and "Managers," using SQL SELECT statements. Which of the following should the analyst use for this task?
Answer : B
This question pertains to the Data Acquisition and Preparation domain, focusing on combining and deduplicating data using SQL. The task is to remove duplicates between two tables, meaning the analyst needs a unique set of records from both.
SELECT * FROM Employees UNION ALL SELECT * FROM Managers (Option A): UNION ALL combines all rows from both tables, including duplicates, which doesn't meet the requirement.
SELECT * FROM Employees UNION SELECT * FROM Managers (Option B): UNION combines rows from both tables and automatically removes duplicates, providing a unique set of records, which fits the task.
SELECT * FROM Employees JOIN SELECT * FROM Managers (Option C): This syntax is incorrect; a JOIN requires an ON clause, and it wouldn't remove duplicates.
SELECT * FROM Employees CROSS JOIN SELECT * FROM Managers (Option D): A CROSS JOIN creates a Cartesian product, resulting in all possible combinations, not removing duplicates.
The DA0-002 Data Acquisition and Preparation domain includes 'executing data manipulation,' and UNION is the correct SQL operation for combining tables while removing duplicates.
==============
The human resources department wants to understand the relationship between the ages and incomes of all employees. Which of the following graphics is the most appropriate to present the analysis?
Answer : A
This question pertains to the Visualization and Reporting domain, focusing on selecting the appropriate visualization to show a relationship between two continuous variables (ages and incomes).
Scatter plot (Option A): A scatter plot displays individual data points on two axes (age vs. income), making it ideal for showing the relationship and potential correlation between two continuous variables.
Area plot (Option B): Area plots are used for showing trends over time, not relationships between two variables.
Bar chart (Option C): Bar charts are better for categorical data comparisons, not continuous variable relationships.
Pie chart (Option D): Pie charts show proportions of a whole, not suitable for showing relationships between variables.
The DA0-002 Visualization and Reporting domain emphasizes 'translating business requirements to form the appropriate visualization,' and a scatter plot is best for showing the relationship between age and income.
==============