CompTIA PenTest+ Exam PT0-003 Practice Questions
[Tools and Code Analysis]
While performing a penetration testing exercise, a tester executes the following command:
bash
Copy code
PS c:\tools> c:\hacks\PsExec.exe \\server01.comptia.org -accepteula cmd.exe
Which of the following best explains what the tester is trying to do?
Answer : B
Lateral Movement with PsExec:
PsExec is a tool used for executing processes on remote systems.
The command enables the tester to execute cmd.exe on the target host (server01) to achieve lateral movement and potentially escalate privileges.
Why Not Other Options?
A: The command is not testing connectivity; it is executing a remote command.
C: PsExec does not send its binary; it executes commands on remote systems.
D: The command is not enabling cmd.exe; it is using it as a tool for executing commands remotely.
CompTIA Pentest+ Reference:
Domain 3.0 (Attacks and Exploits)
A penetration tester attempts to obtain the preshared key for a client's wireless network. Which of the following actions will most likely aid the tester?
Answer : D
Obtaining a wireless preshared key (PSK) in a WPA/WPA2-Personal environment typically relies on capturing the 4-way handshake (or equivalent key exchange) between a client and the access point. PenTest+ emphasizes that the handshake is captured when a client authenticates or reauthenticates to the network; once the handshake is collected, the tester can attempt an offline password attack to determine the PSK (subject to rules of engagement and authorization).
Using aireplay-ng to perform a deauthentication attack forces connected clients to disconnect and then automatically reconnect, which triggers a new handshake that can be captured by the tester's monitoring interface. This directly supports the goal of acquiring material needed to recover the PSK.
During an assessment, a penetration tester sends the following request:
POST /services/v1/users/create HTTP/1.1
Host: target-application.com
Content-Type: application/json
Content-Length: [dynamic]
Authorization: Bearer (FUZZ)
Which of the following attacks is the penetration tester performing?
Answer : B
This attack attempts to manipulate the API by fuzzing the authorization token (Authorization: Bearer (FUZZ)). This suggests an attempt to bypass authentication or escalate privileges by using an invalid, stolen, or guessed token---a form of API abuse.
Option A (Directory traversal) :
Involves manipulating file paths (e.g., ../../../etc/passwd), but this attack targets API authentication.
Option B (API abuse) :
Correct. Fuzzing the authorization token suggests an attempt to bypass authentication or test for weak API security.
Option C (Server-side request forgery - SSRF) :
SSRF manipulates backend requests to make unauthorized HTTP calls, which is not evident here.
Option D (Privilege escalation) :
While API abuse may lead to privilege escalation, fuzzing the token alone does not directly escalate privileges.
Reference: CompTIA PenTest+ PT0-003 Official Guide -- API Security Testing & Authentication Bypasses
A penetration tester identifies the following vulnerability during a scan of the company's network:
Severity: HIGH
Vulnerability: ABC Load Balancer: Alpha OS httpd TLS vulnerability
An Nmap scan of the affected device produces the following results:
Host is up (0.0000040s latency).
Not shown: 98 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
443/tcp closed https
Which of the following best describes this scenario?
Answer : D
Comprehensive and Detailed
The vulnerability report identifies a TLS vulnerability on port 443 (HTTPS). However, the Nmap scan shows port 443 as closed, meaning the service is not running or reachable.
If the service associated with the vulnerability is not active, the reported issue cannot be valid. Therefore, the scan result contradicts the finding --- making it a false positive (the scanner incorrectly flagged a vulnerability that doesn't exist).
Why not the others:
A . True negative: Would mean no vulnerability exists and none was reported.
B . True positive: Would mean both the scan and vulnerability report agree that the service is running and vulnerable --- not the case here.
C . False negative: Would mean a vulnerability exists but was not detected --- also not the case.
CompTIA PT0-003 Mapping:
Domain 2.0: Information Gathering and Vulnerability Scanning
[Attacks and Exploits]
SIMULATION
Using the output, identify potential attack vectors that should be further investigated.
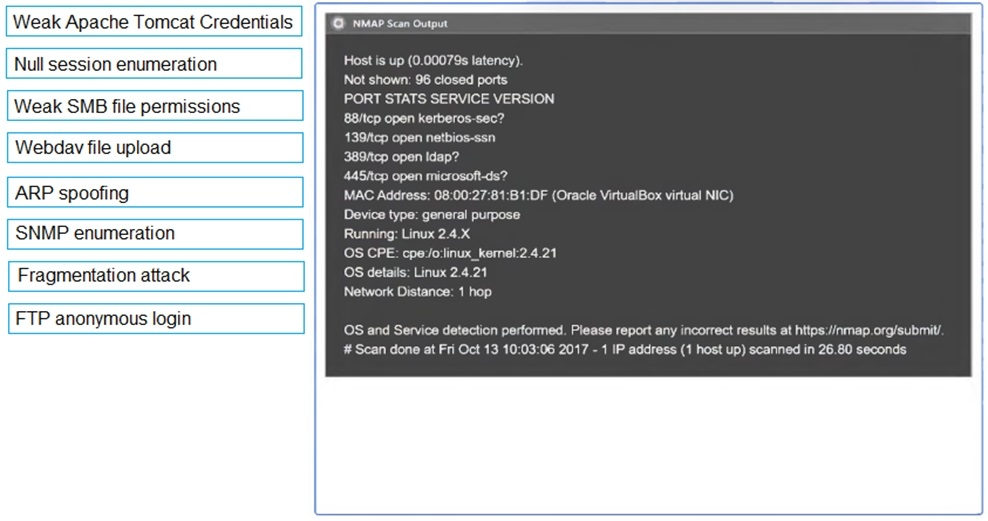
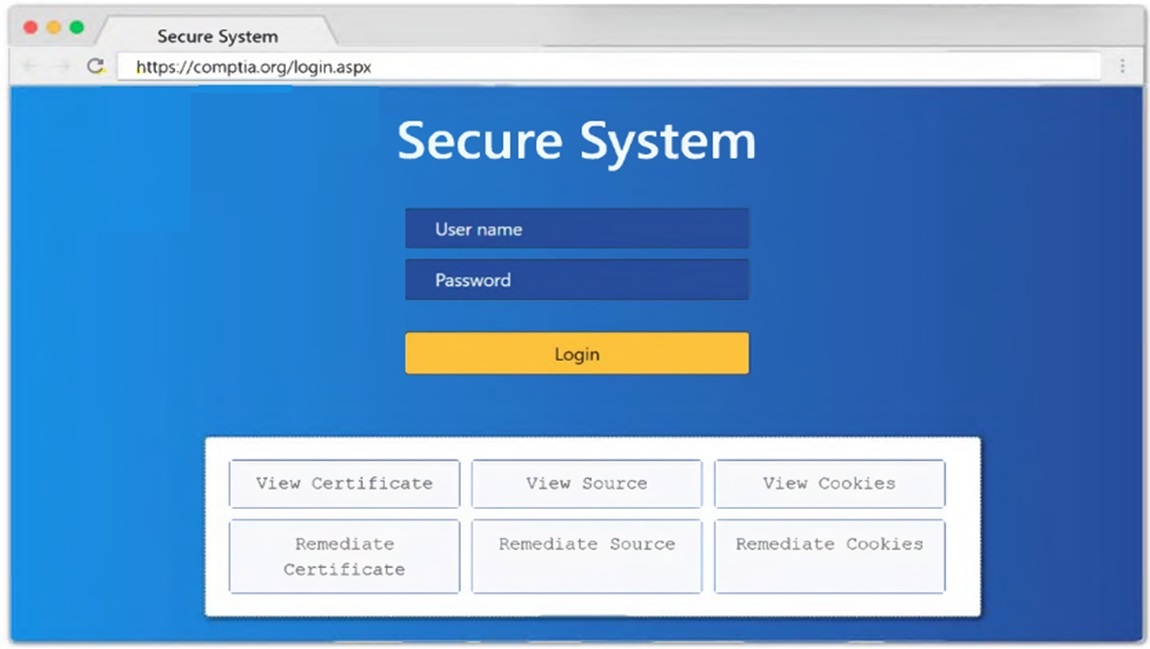
Answer : A
1: Null session enumeration
Weak SMB file permissions
Fragmentation attack
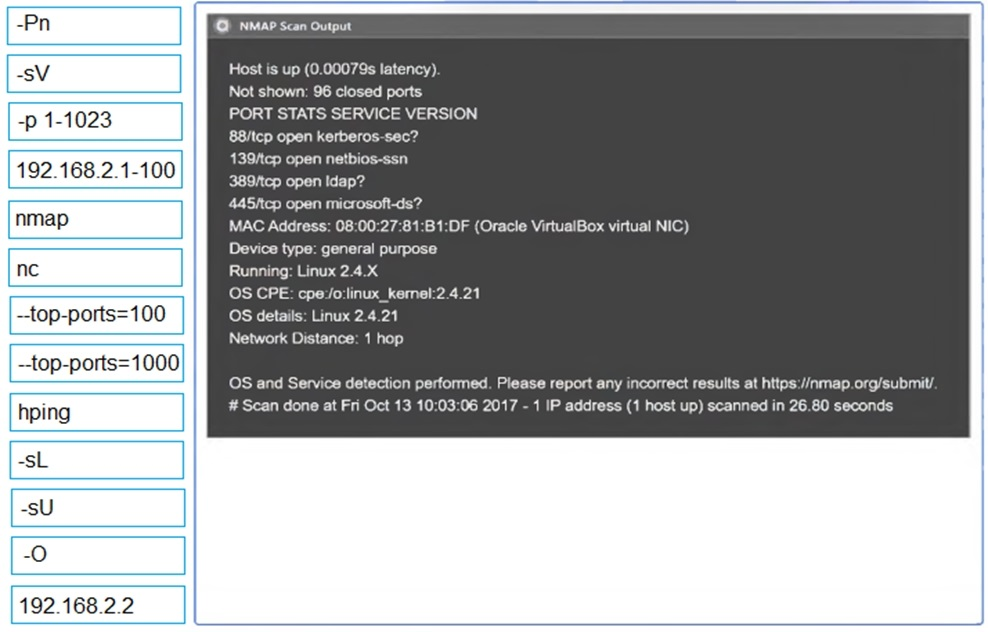
2: nmap
-sV
-p 1-1023
192.168.2.2
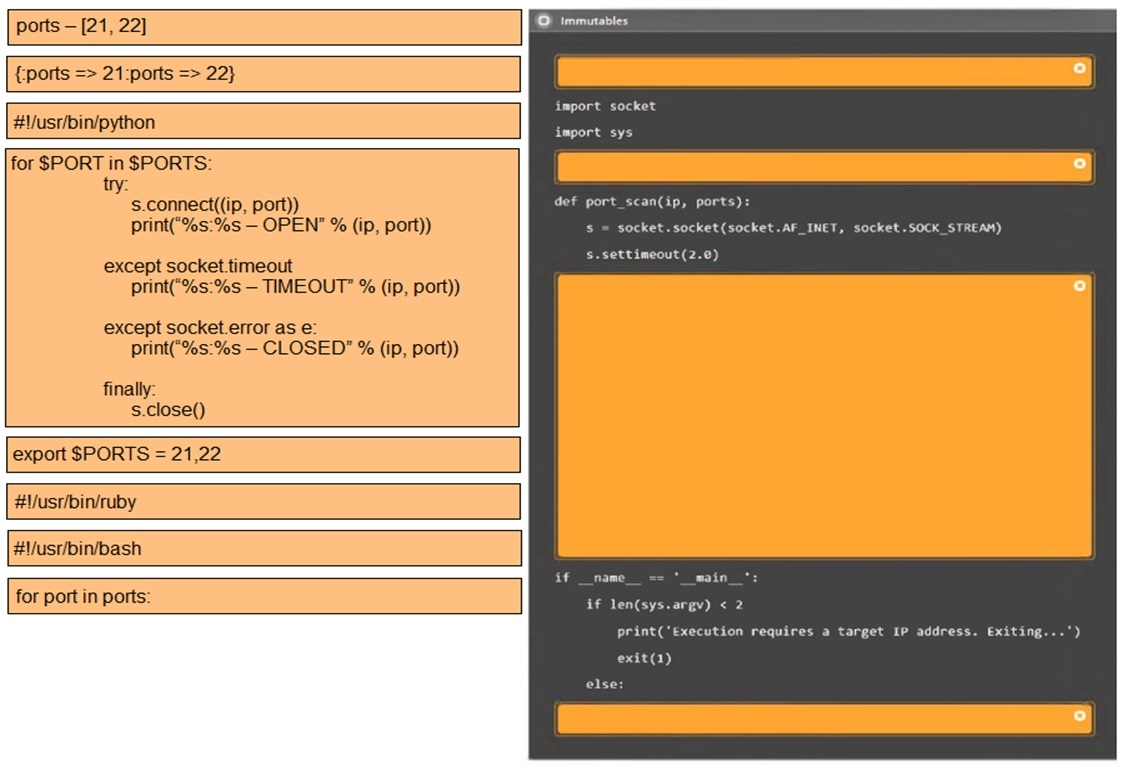
3: #!/usr/bin/python
export $PORTS = 21,22
for $PORT in $PORTS:
try:
s.connect((ip, port))
print(''%s:%s -- OPEN'' % (ip, port))
except socket.timeout
print(''%:%s -- TIMEOUT'' % (ip, port))
except socket.error as e:
print(''%:%s -- CLOSED'' % (ip, port))
finally
s.close()
port_scan(sys.argv[1], ports)
A penetration tester must identify hosts without alerting an IPS. The tester has access to a local network segment. Which of the following is the most logical action?
Answer : A
When the objective is to identify hosts while minimizing the chance of triggering an IPS, PenTest+ prioritizes low-noise reconnaissance techniques over active probing. A reverse DNS lookup queries DNS PTR records for IP addresses and can reveal hostnames for systems that are already registered in internal DNS. This often generates traffic that appears similar to normal enterprise name-resolution activity and is typically less suspicious than broad ICMP echo sweeps or repeated port probes.
[Attacks and Exploits]
While performing an internal assessment, a tester uses the following command:
crackmapexec smb 192.168.1.0/24 -u user.txt -p Summer123@
Which of the following is the main purpose of the command?
Answer : C
The command crackmapexec smb 192.168.1.0/24 -u user.txt -p Summer123@ is used to perform password spraying on internal systems. CrackMapExec (CME) is a post-exploitation tool that helps automate the process of assessing large Active Directory networks. It supports multiple protocols, including SMB, and can perform various actions like password spraying, command execution, and more.
CrackMapExec:
CrackMapExec: A versatile tool designed for pentesters to facilitate the assessment of large Active Directory networks. It supports various protocols such as SMB, WinRM, and LDAP.
Purpose: Commonly used for tasks like password spraying, credential validation, and command execution.
Command Breakdown:
crackmapexec smb: Specifies the protocol to use, in this case, SMB (Server Message Block), which is commonly used for file sharing and communication between nodes in a network.
192.168.1.0/24: The target IP range, indicating a subnet scan across all IP addresses in the range.
-u user.txt: Specifies the file containing the list of usernames to be used for the attack.
-p Summer123@: Specifies the password to be used for all usernames in the user.txt file.
Password Spraying:
Definition: A technique where a single password (or a small number of passwords) is tried against a large number of usernames to avoid account lockouts that occur when brute-forcing a single account.
Goal: To find valid username-password combinations without triggering account lockout mechanisms.
Pentest Reference:
Password Spraying: An effective method for gaining initial access during penetration tests, particularly against organizations that have weak password policies or commonly used passwords.
CrackMapExec: Widely used in penetration testing for its ability to automate and streamline the process of credential validation and exploitation across large networks.
By using the specified command, the tester performs a password spraying attack, attempting to log in with a common password across multiple usernames, identifying potential weak accounts.