CyberArk Defender Access ACCESS-DEF Exam Questions
The Security Operation Team requested a report to show users who have logged in the last seven days.
Which report in the Builtin Reports Library should you use?
The Security Operation Team requested a report to show users who have logged in the last seven days.
Which report in the Builtin Reports Library should you use?
Answer : D
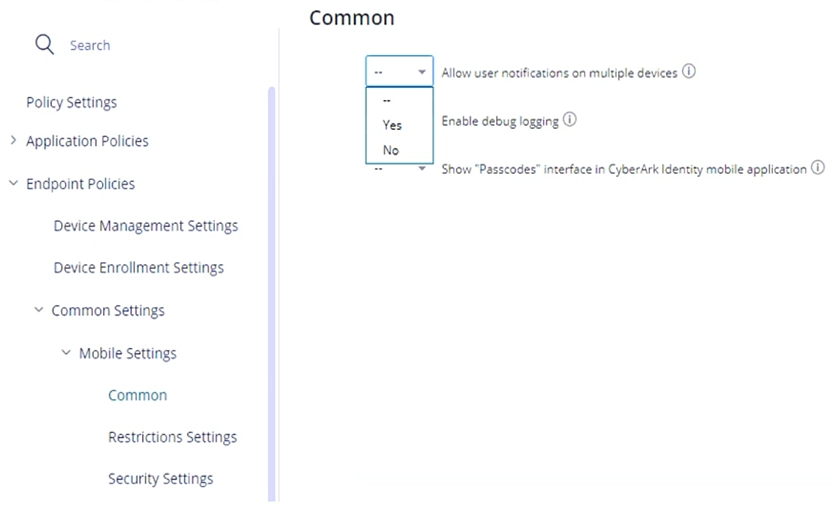
Refer to the exhibit.
Within the "Allow user notifications on multiple devices", if you leave the setting as Default (--), what happens if a user triggers a MFA Push notification and has enrolled three different devices?
Answer : B
CyberArk Identity has created a CLI integration with which vendor?
Answer : A
When can 2FA/MFA be prompted? (Choose two.)
Answer : A, C
Which 2FA/MFA options can be used if users cannot use their mobile device? (Choose two.)
Answer : A, B
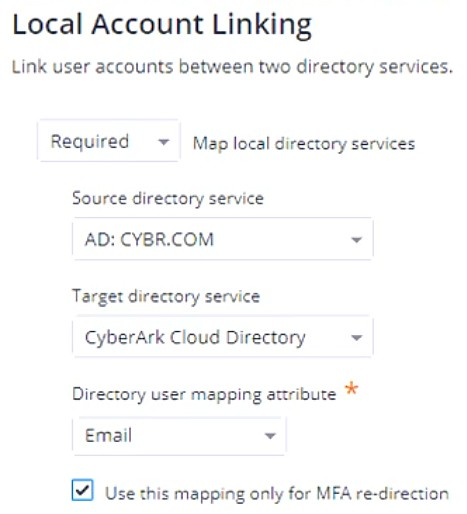
Refer to the exhibit.
If an Authentication Policy is configured as shown in the exhibit, which statement is correct?
Answer : A
When logging on to the User Portal, which authentication methods can enable the user to bypass authentication rules and default profile? (Choose two.)
Answer : B, D