Dell EMC Dell PowerStore Deploy 2023 D-PST-DY-23 Exam Questions
A PowerStore appliance is running out of storage capacity. The cluster consists of a PowerStore 5000T appliance with three NVMe expansion enclosures.
How can this issue be resolved?
Answer : B
PowerStore 5000T and Expansion: The PowerStore 5000T model supports a maximum of three NVMe expansion enclosures. Since the appliance already has three, adding more is not an option.
Scaling Out: To increase capacity in this scenario, you need to scale out by adding another PowerStore appliance to the cluster. This will provide additional storage resources and processing power.
Which of me following is true statement?
Answer : B
Which two methods would a customer use to migrate their legacy block thick and thin clones to PowerStore? (Choose two.)
Answer : C, E
Which two pieces of information are required to create a new remote system connection? (Choose two.)
Answer : B, C
In the Add Remote System slide-out panel, configure the following fields:
- Remote system type - Select PowerStore.
- Management IP address
- Description (optional)
- Network latency
https://www.dell.com/support/manuals/en-us/powerstore-7000/pwrstr-protect-data/add-a-remote-system-connection-for-replication-and-metro?guid=guid-937b06e1-2a74-40e1-a8b6-9aae6f72e27d&lang=en-us
Which two NAS servers must be configured with DNS support? (Choose two.)
Answer : B, D
B . Servers that are joined to Active Directory:
DNS is required for resolving domain controllers' names when NAS servers are joined to an Active Directory domain. Proper DNS support ensures seamless integration and authentication within the domain.
D . Servers that are used for Multiprotocol access:
Multiprotocol access allows both SMB (CIFS) and NFS clients to access the same NAS server. DNS is essential for name resolution, especially in environments where SMB relies on domain-based configurations.
SIMULATION
Use the simulator to create an SMB NAS server using the following information:
* NAS and SMB computer name: payrollserver
* Network interface: BaseEnclosure-bond1
* IP address: 192.168.2.20
* Subnet: /24
* Gateway: 192.168.2.254
* VLAN: 1504
* AD/DNS: 192.168.2.50
* Windows domain name: company.com
* Domain administrator credentials: Administrator/password
When you have finished continue to the next question.
Answer : A
1. Open the simulator and log in with the default credentials: admin/Password123#.
2. SelectStorage>NAS Serversfrom the left menu.
3. Click+ CREATEto launch the Create NAS Server wizard.
4. Enterpayrollserveras the NAS and SMB computer name and clickNext.
5. SelectBaseEnclosure-bond1as the network interface and clickNext.
6. Enter192.168.2.20as the IP address,/24as the subnet,192.168.2.254as the gateway, and1504as the VLAN ID. ClickNext.
7. SelectJoin a Windows domainas the SMB server type and clickNext.
8. Enter192.168.2.50as the AD/DNS server,company.comas the Windows domain name,Administratoras the domain administrator username, andpasswordas the domain administrator password. ClickNext.
9. Review the summary and clickFinishto create the SMB NAS server.
SIMULATION
A storage admin is setting up a new protection policy with only snapshot rule for a new file system in PowerStore.
The administrator is given the below parameters.
Use the simulator to perform the configuration task.
When you have finished continue to the next question.
Answer : A
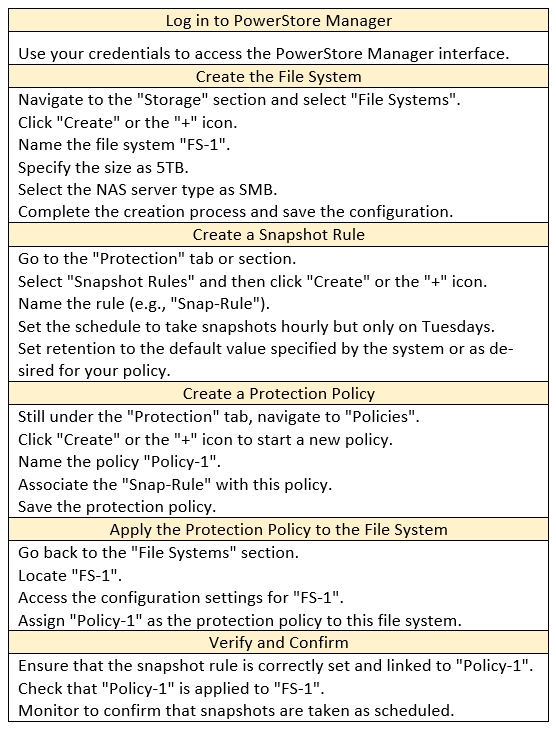
1. Create the File System
Navigate to Storage > File Systems.
Click Add File System.
Enter the file system name: FS-1
Set the file system size to 5 TB.
Select the appropriate NAS Server (SMB-NAS Server in this case).
Click Add.
2. Create the Protection Policy
Navigate to Protection > Protection Policies.
Click Add Protection Policy.
Enter the policy name: Policy-1
Click Next.
3. Configure the Snapshot Rule
In the 'Snapshot Rules' section, click Add Rule.
Enter a name for the rule (e.g., 'Snap-Rule').
Set the Days to Tuesday.
Set the Every field to 1 Hour.
Ensure that Retention is set to the default value.
Click Add.
Click Next.
4. Review and Finish
Review the protection policy summary.
Click Finish.
5. Apply the Protection Policy to the File System
Navigate back to Storage > File Systems.
Locate the FS-1 file system.
Click the More Actions button (three vertical dots) and select Edit.
In the 'Protection Policy' field, select the newly created Policy-1 from the dropdown list.
Click Save.
Verification
To verify the configuration, go to Protection > Protection Policies.
Select Policy-1.
You should see the configured snapshot rule ('Snap-Rule') with the specified settings.
Key Considerations
Default Retention: The default retention for snapshots in PowerStore will vary depending on your system configuration. Ensure that the default retention meets your data protection needs.
Snapshot Schedule: The snapshot rule you created will take hourly snapshots of the file system every Tuesday.
By following these steps, you'll successfully create the protection policy with the specified snapshot rule and apply it to the new file system, meeting all the requirements of the simulation task.