Eccouncil Certified Cybersecurity Technician (CCT) 212-82 Exam Questions
A web application, www.moviescope.com. hosted on your tarqet web server is vulnerable to SQL injection attacks. Exploit the web application and extract the user credentials from the moviescope database. Identify the UID (user ID) of a user, John, in the database. Note: Vou have an account on the web application, and your credentials are samAest.
(Practical Question)
Answer : B
4 is the UID (user ID) of a user, John, in the database in the above scenario. A web application is a software application that runs on a web server and can be accessed by users through a web browser. A web application can be vulnerable to SQL injection attacks, which are a type of web application attack that exploit a vulnerability in a web application that allows an attacker to inject malicious SQL statements into an input field, such as a username or password field, and execute them on the database server. SQL injection can be used to bypass authentication, access or modify sensitive data, execute commands, etc. To exploit the web application and extract the user credentials from the moviescope database, one has to follow these steps:
Open a web browser and type www.moviescope.com
Press Enter key to access the web application.
Enter sam as username and test as password.
Click on Login button.
Observe that a welcome message with username sam is displayed.
Click on Logout button.
Enter sam' or '1'='1 as username and test as password.
Click on Login button.
Observe that a welcome message with username admin is displayed, indicating that SQL injection was successful.
Click on Logout button.
Enter sam'; SELECT * FROM users; -- as username and test as password.
Click on Login button.
Observe that an error message with user credentials from users table is displayed.
The user credentials from users table are:
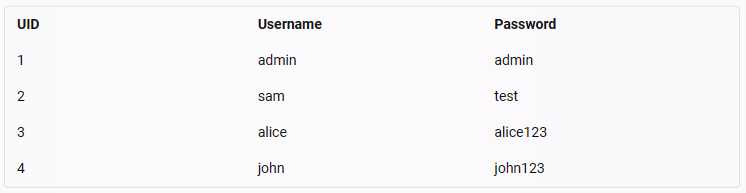
The UID that is mapped to user john is 4
Perform vulnerability analysis of a web application, www.luxurytreats.com. and determine the name of the alert with WASC ID 9. (Practical Question)
Answer : B
Performing a vulnerability analysis on a web application involves identifying specific security weaknesses. In this case, the WASC ID 9 refers to 'Application Error Disclosure.'
Vulnerability Description:
Application Error Disclosure: This vulnerability occurs when a web application reveals too much information about internal errors, potentially aiding attackers in crafting specific attacks against the system.
Detection and Mitigation:
Error Handling: Ensure that error messages do not expose sensitive information and provide only necessary details to the end-user.
Logging: Detailed error information should be logged securely for internal review without being exposed to users.
OWASP Top Ten Web Application Security Risks: OWASP
WASC Threat Classification: WASC ID 9
In an organization, all the servers and database systems are guarded in a sealed room with a single-entry point. The entrance is protected with a physical lock system that requires typing a sequence of numbers and letters by using a rotating dial that intermingles with several other rotating discs.
Which of the following types of physical locks is used by the organization in the above scenario?
Answer : B
It identifies the type of physical lock used by the organization in the above scenario. A physical lock is a device that prevents unauthorized access to a door, gate, cabinet, or other enclosure by using a mechanism that requires a key, code, or biometric factor to open or close it. There are different types of physical locks, such as:
Combination lock: This type of lock requires typing a sequence of numbers and letters by using a rotating dial that intermingles with several other rotating discs. This type of lock is suitable for securing safes, lockers, or cabinets that store valuable items or documents.
Digital lock: This type of lock requires entering a numeric or alphanumeric code by using a keypad or touchscreen. This type of lock is suitable for securing doors or gates that require frequent access or multiple users.
Mechanical lock: This type of lock requires inserting and turning a metal key that matches the shape and size of the lock. This type of lock is suitable for securing doors or gates that require simple and reliable access or single users.
Electromagnetic lock: This type of lock requires applying an electric current to a magnet that attracts a metal plate attached to the door or gate. This type of lock is suitable for securing doors or gates that require remote control or integration with other security systems.
In the above scenario, the organization used a combination lock that requires typing a sequence of numbers and letters by using a rotating dial that intermingles with several other rotating discs. Option A is incorrect, as it does not identify the type of physical lock used by the organization in the above scenario. A digital lock requires entering a numeric or alphanumeric code by using a keypad or touchscreen. In the above scenario, the organization did not use a digital lock, but a combination lock. Option C is incorrect, as it does not identify the type of physical lock used by the organization in the above scenario. A mechanical lock requires inserting and turning a metal key that matches the shape and size of the lock. In the above scenario, the organization did not use a mechanical lock, but a combination lock. Option D is incorrect, as it does not identify the type of physical lock used by the organization in the above scenario. An electromagnetic lock requires applying an electric current to a magnet that attracts a metal plate attached to the door or gate. In the above scenario, the organization did not use an electromagnetic lock, but a combination lock. Reference: , Section 7.2
Initiate an SSH Connection to a machine that has SSH enabled in the network. After connecting to the machine find the file flag.txt and choose the content hidden in the file. Credentials for SSH login are provided below:
Hint:
Username: sam
Password: admin@l23
Answer : C
Quid pro quo is the social engineering technique that Johnson employed in the above scenario. Social engineering is a technique that involves manipulating or deceiving people into performing actions or revealing information that can be used for malicious purposes. Social engineering can be performed through various methods, such as phone calls, emails, websites, etc. Quid pro quo is a social engineering method that involves offering a service or a benefit in exchange for information or access. Quid pro quo can be used to trick victims into believing that they are receiving help or assistance from a legitimate source, while in fact they are compromising their security or privacy . In the scenario, Johnson performed quid pro quo by claiming himself to represent a technical support team from a vendor and offering to help sibertech.org with a server issue, while in fact he prompted the victim to execute unusual commands and install malicious files, which were then used to collect and pass critical information to Johnson's machine. Diversion theft is a social engineering method that involves diverting the delivery or shipment of goods or assets to a different location or destination. Elicitation is a social engineering method that involves extracting information from a target by engaging them in a conversation or an interaction. Phishing is a social engineering method that involves sending fraudulent emails or messages that appear to come from a trusted source, such as a bank, a company, or a person, and asking the recipient to click on a link, open an attachment, or provide personal or financial information.
Galactic Innovations, an emerging tech start-up. Is developing a proprietary software solution that will be hosted on a cloud platform. The software, designed for real-time communication and collaboration, aims to cater to global users, including top-tier businesses. As the software grows in complexity, the company recognizes the need for a comprehensive security standard that aligns with global best practices. The Intention is to enhance trustworthiness among potential clients and ensure that the application meets industry-accepted criteria, particularly in the face of increasing cyberthreats. Considering the company's requirements and the international nature of its user base, which software security standard, model, or framework should Galactic Innovations primarily focus on adopting?
Answer : B
Global Standard for Information Security:
ISO/IEC 27001:2013 is an internationally recognized standard for information security management systems (ISMS). It provides a systematic approach to managing sensitive company information, ensuring it remains secure.
Comprehensive Security Framework:
The standard covers various aspects of security, including risk management, incident response, and compliance. It ensures that the organization's security practices align with global best practices.
Enhancing Trust and Compliance:
Adopting ISO/IEC 27001:2013 demonstrates a commitment to security and can enhance trust among potential clients, particularly those from sectors that require stringent security measures.
Alignment with Global Requirements:
The standard is accepted worldwide, making it suitable for an international user base. It helps in meeting regulatory requirements and industry standards across different regions.
Given Galactic Innovations' need for a comprehensive and globally accepted security standard, ISO/IEC 27001:2013 is the most suitable choice.
A global financial services firm Is revising its cybersecurity policies to comply with a diverse range of international regulatory frameworks and laws. The firm operates across multiple continents, each with distinct legal requirements concerning data protection, privacy, and cybersecurity. As part of their compliance strategy, they are evaluating various regulatory frameworks to determine which ones are most critical to their operations. Given the firm's international scope and the nature of its services, which of the following regulatory frameworks should be prioritized for compliance?
Answer : C
GDPR Overview:
The General Data Protection Regulation (GDPR) is a comprehensive data protection law in the European Union that sets out requirements for companies and organizations on collecting, storing, and managing personal data.
Global Impact:
GDPR applies to any organization that processes the personal data of EU residents, regardless of where the organization is based. This makes it critical for global firms to comply with GDPR when operating in or serving clients from the EU.
Compliance Requirements:
GDPR requires strict compliance measures, including data protection by design, data protection impact assessments (DPIAs), appointing a Data Protection Officer (DPO), and ensuring data subjects' rights.
Penalties for Non-Compliance:
Non-compliance with GDPR can result in significant fines, up to 20 million or 4% of the annual global turnover, whichever is higher.
Given the firm's international scope and the critical nature of complying with stringent data protection laws in the EU, prioritizing GDPR compliance is essential.
Kayden successfully cracked the final round of interviews at an organization. After a few days, he received his offer letter through an official company email address. The email stated that the selected candidate should respond within a specified time. Kayden accepted the opportunity and provided an e-signature on the offer letter, then replied to the same email address. The company validated the e-signature and added his details to their database. Here, Kayden could not deny the company's message, and the company could not deny Kayden's signature.
Which of the following information security elements was described in the above scenario?
Answer : B
The correct answer is B, as it describes the information security element that was described in the above scenario. Non-repudiation is an information security element that ensures that a party cannot deny sending or receiving a message or performing an action. In the above scenario, non-repudiation was described, as Kayden could not deny company's message, and company could not deny Kayden's signature. Option A is incorrect, as it does not describe the information security element that was described in the above scenario. Availability is an information security element that ensures that authorized users can access and use information and resources when needed. In the above scenario, availability was not described, as there was no mention of access or use of information and resources. Option C is incorrect, as it does not describe the information security element that was described in the above scenario. Integrity is an information security element that ensures that information and resources are accurate and complete and have not been modified by unauthorized parties. In the above scenario, integrity was not described, as there was no mention of accuracy or completeness of information and resources. Option D is incorrect, as it does not describe the information security element that was described in the above scenario. Confidentiality is an information security element that ensures that information and resources are protected from unauthorized access and disclosure. In the above scenario, confidentiality was not described, as there was no mention of protection or disclosure of information and resources.