Eccouncil Certified SOC Analyst v2 312-39 Exam Questions
Global Solutions Inc. uses syslog for centralized logging across a geographically diverse network. The SOC team must ensure logs are reliably delivered from remote sites to the central logging server across potentially unreliable network connections. To guarantee consistent and dependable log delivery, which syslog architectural layer should they focus on optimizing and hardening?
Answer : D
Reliable delivery across unreliable networks is primarily a transport-layer concern. The syslog transport layer covers how messages are transmitted between devices, relays, and collectors, including protocol choice and delivery assurance. Many syslog deployments default to UDP for simplicity, but UDP is lossy and does not guarantee delivery---problematic for remote sites and compliance-driven logging. Hardening transport typically involves using TCP (reliable delivery), TLS for encryption and integrity, buffering/queueing at relays, retransmission handling, and monitoring of connection health and backlog. The content layer is about message format and fields; management and filtering is about routing and reduction of noise; application layer relates to the syslog-generating and receiving software. Those are important, but they do not address the fundamental need for dependable delivery under network instability. From a SOC perspective, transport reliability directly impacts forensic completeness, alert accuracy, and compliance evidence. Therefore, optimizing and hardening the syslog transport layer is the correct priority.
Identify the type of attack, an attacker is attempting on www.example.com website.
Answer : A
The scenario depicted suggests an attacker is injecting a script into the URL of the website ''www.example.com'' which triggers an alert message. This behavior is characteristic of a Cross-site Scripting (XSS) attack. In XSS attacks, attackers exploit vulnerabilities in web applications to inject malicious scripts into web pages viewed by other users. The injected scripts can steal user data, deface web pages, or redirect users to malicious sites.
The specific attack vector here involves the attacker adding a script to the URL that causes the website to display an alert message. This indicates that the website is not properly sanitizing its inputs, which is how the attacker is able to execute the script in the context of the user's browser session.
References:The EC-Council's Certified SOC Analyst (CSA) program covers various types of cyberattacks, including XSS attacks. The CSA course materials and study guides provide detailed information on identifying, mitigating, and preventing such attacks, as well as best practices for securing web applications against them.
At a large healthcare organization, the Security Operations Center (SOC) detects a surge of failed login attempts on employee accounts, indicating a possible brute-force attack. To contain the threat, the team quickly takes action to prevent unauthorized access. However, they also need to implement a security measure that strengthens account protection beyond just stopping the current attack, reducing the risk of similar incidents in the future. During the Containment Phase, which action would best enhance long-term account security against brute-force attacks?
Answer : D
MFA is the most effective long-term control among the options because it directly reduces the attacker's ability to succeed even when passwords are guessed, reused, or stolen. Brute-force and credential stuffing attacks exploit the single-factor nature of passwords; MFA adds an additional verification factor (authenticator app prompt, FIDO2 key, certificate-based auth), making account takeover significantly harder. From a containment standpoint, blocking IPs and enabling lockout can reduce immediate attack volume, but attackers commonly rotate IPs, use botnets, or target many accounts in parallel, which can also cause operational impact via account lockouts (denial of service against users). Cross-verifying false positives is important for accuracy, but it does not strengthen security. Notifying users can help awareness but is not a technical control. In SOC operations, the best practice is layered containment: immediate throttling/blocks and lockout tuning for the active attack, followed by durable hardening controls. MFA is the durable hardening step that meaningfully reduces future brute-force success rates and complements conditional access policies (geo/time/device risk) and stronger password protections.
Which of the following attacks causes sudden changes in file extensions or increase in file renames at rapid speed?
Answer : A
Bob is a SOC analyst in a multinational corporation that relies on a centralized file-sharing system for storing confidential project documents. One morning, he notices that a few critical financial records stored on the shared server appear to have been altered without authorization. Version history confirms unexpected changes made outside business hours. Bob must investigate by inspecting logs. Which log should he check to determine who accessed the files and when the modifications occurred?
Answer : A
Security logs are the primary source for auditing access and changes to protected objects, including files and folders, when file auditing is enabled. In Windows environments, this typically maps to ''Object Access'' auditing, which can record who accessed a file, what type of access was attempted (read, write, delete), and when it occurred. For a SOC analyst investigating unauthorized modifications, the goal is attribution (which user/account), timing (outside business hours), and action (write/modify/delete). Authentication logs show who logged in and from where, but they don't reliably indicate which file was modified unless correlated with object access events. Firewall and general network logs can help confirm remote access paths or suspicious connections, but they won't provide authoritative ''who modified which file'' evidence. In practice, the SOC would validate that file/folder auditing is enabled on the file server and that relevant events are being collected centrally. Then they correlate file access/modify events with sign-in activity, source device, and any privilege escalation indicators. Because the question specifically asks for determining ''who accessed the files and when modifications occurred,'' Security logs are the most direct and forensically valuable option.
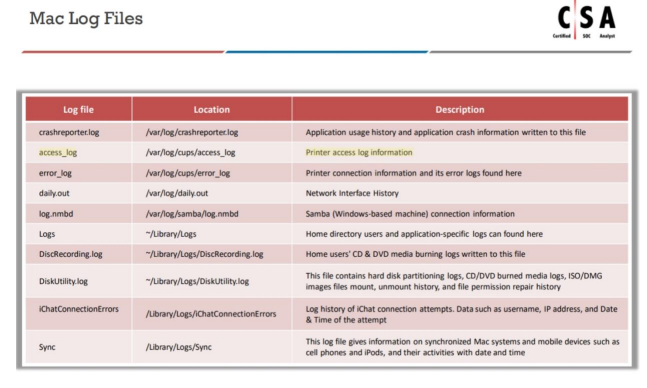
Which of the following directory will contain logs related to printer access?
Answer : B
Planning and budgeting:This is the initial phase where you determine the scope, objectives, and financial resources available for the lab.
Physical location and structural design considerations:Selecting a suitable location and designing the lab to meet operational needs and security requirements.
Work area considerations:Organizing the space efficiently for different tasks such as evidence analysis, storage, and administrative work.
Human resource considerations:Identifying the roles, responsibilities, and qualifications required for lab personnel.
Physical security recommendations:Implementing measures to protect sensitive data and physical assets within the lab.
Forensics lab licensing:Ensuring that the lab and its personnel are compliant with relevant laws, regulations, and industry standards.
References:While I can't refer to specific EC-Council SOC Analyst courses or study guides, these steps are generally accepted as part of the process for setting up a computer forensics lab. For detailed guidance, it's best to consult the official EC-Council resources and materials provided for the SOC Analyst certification.
What is the correct sequence of SOC Workflow?
Answer : D
Collect:The first step involves collecting data from various sources. This data could be logs, alerts, or other relevant information.
Ingest:The collected data is then ingested into the SOC's systems for processing. This typically involves parsing and normalizing the data to make it usable for analysis.
Validate:Once ingested, the data must be validated to ensure its integrity and relevance. This step helps in filtering out false positives and focusing on genuine security events.
Report:After validation, the relevant findings are compiled into reports. These reports may be used internally within the SOC or shared with other stakeholders.
Respond:Based on the reports, the SOC team responds to the identified incidents. This response could involve mitigating threats, patching vulnerabilities, or other remediation actions.
Document:Finally, all actions and findings are thoroughly documented. This documentation is crucial for audit trails, compliance, and improving future SOC operations.
References:The sequence provided is aligned with the SOC operations as described in EC-Council's Certified SOC Analyst (CSA) training and certification program, which covers the fundamentals of SOC operations, including the workflow of SOC analysts123.