Eccouncil Certified Application Security Engineer (CASE) JAVA 312-96 Exam Questions
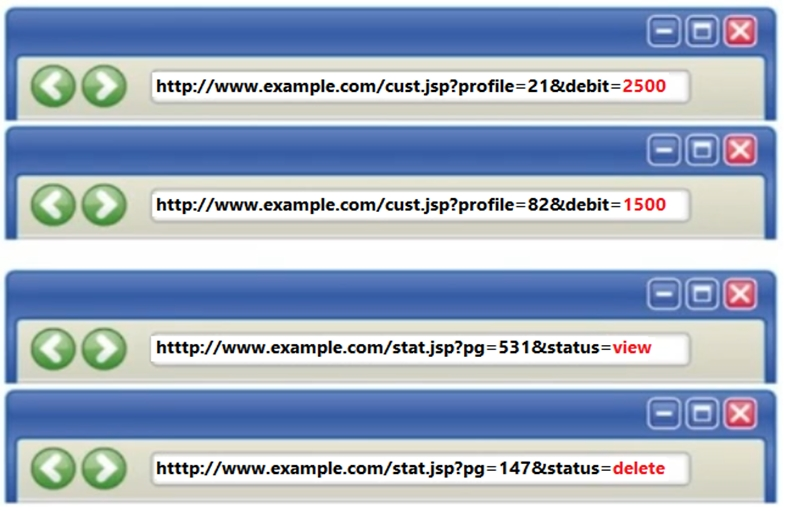
Identify the type of attack depicted in the following figure.
Answer : C
Which of the following can be derived from abuse cases to elicit security requirements for software system?
Answer : D
In which phase of secure development lifecycle the threat modeling is performed?
Answer : D
The software developer has implemented encryption in the code as shown in the following screenshot.
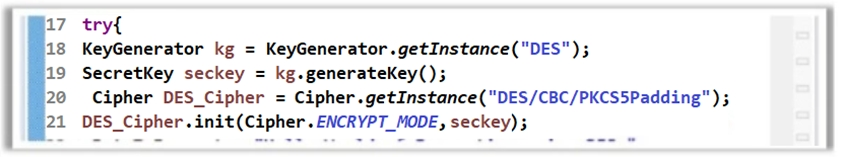
However, using the DES algorithm for encryption is considered to be an insecure coding practice as DES is a weak encryption algorithm. Which of the following symmetric encryption algorithms will you suggest for strong encryption?
Answer : D
Which of the following elements in web.xml file ensures that cookies will be transmitted over an encrypted channel?
Answer : D
Which of the following method will help you check if DEBUG level is enabled?
Answer : A
Which of the following relationship is used to describe abuse case scenarios?
Answer : B