F5 Networks BIG-IP Administration Support and Troubleshooting F5CAB5 Exam Questions
Exhibit:
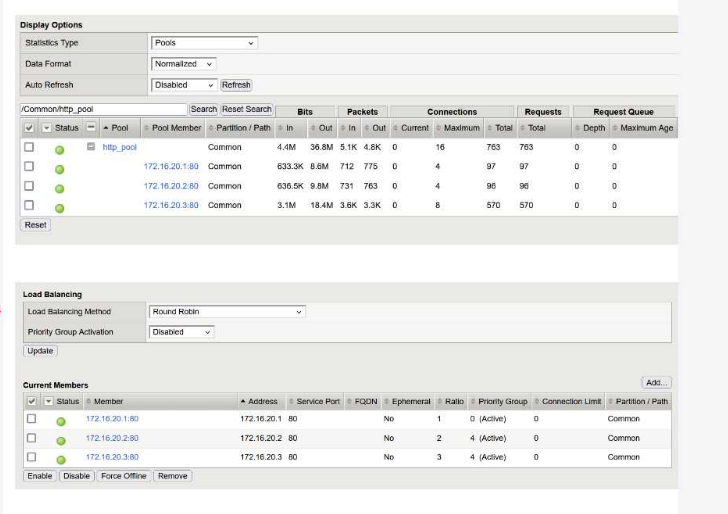
A BIG-IP Administrator configured a virtual server with a pool of 3 members and selected the Round Robin load balancing method to evenly distribute traffic across the pool members. During initial testing, traffic was not evenly distributed and the pool member 172.16.20.3 received more traffic than the other pool members.
Refer to the exhibit and the virtual server configuration provided below:
Plaintext
ltm virtual http.vs {
destination 10.10.1.100:http
ip-protocol tcp
mask 255.255.255.255
persist {
source_addr { default yes }
}
pool http.pool
profiles {
tcp{}
}
serverssl-use-sni disabled
source 0.0.0.0/0
source-address-translation {
type automap
}
translate-address enabled
}
What is the most likely cause of this behavior?
Answer : D
The primary reason for the uneven traffic distribution is the presence of a Persistence Profile in the virtual server configuration.
Load Balancing vs. Persistence: While the Round Robin method is designed to distribute new connections sequentially among pool members, Persistence overrides this logic for existing clients.
Source Address Persistence: The configuration shows source_addr persistence is enabled. This ensures that once a client (identified by their source IP) is mapped to a pool member, all subsequent connections from that same IP will be sent to the same member for the duration of the persistence record.
Uneven Distribution Logic: If one source IP address generates significantly more connections or longer-lived sessions than others---or if many clients appear behind a single NAT/Proxy IP---that specific pool member (in this case, 172.16.20.3) will receive a disproportionate amount of traffic compared to the others.
Evaluating Other Options:
Automap (Option A): SNAT Automap changes the source IP between the BIG-IP and the pool member. It does not impact the BIG-IP's ability to load balance incoming client requests.
Ratio Settings (Option B): In the provided exhibit, the pool members have a Ratio of 1, 2, and 3 respectively. While a higher ratio does direct more traffic to a member, the question asks for the 'most likely cause' in the context of the provided ltm virtual configuration, which explicitly highlights the persistence override.
HTTP Profile (Option C): Round Robin is a Layer 4 load balancing algorithm and does not require a Layer 7 HTTP profile to function.
Which file should the BIG-IP Administrator check to determine when a Virtual Server changed its status from RED to GREEN?
Answer : B
Status changes for local traffic objects (Virtual Servers, Pools, Nodes) are recorded in the Local Traffic Manager (LTM) log.
Health State Logging: When a health monitor marks a resource as available (Green) or unavailable (Red), the system generates a log message in /var/log/ltm.
Log Entry Example: A transition from Red to Green will appear as a message similar to: 01010027:3: Pool /Common/my_pool member /Common/10.0.0.1:80 monitor status up.
Evaluation of Other Options:
/var/log/audit (Option A) logs who changed a configuration, not automated state changes from health monitors.
/var/log/lastlog (Option C) is a standard Linux file that tracks the last login time of users.
/var/log/monitors (Option D) is not a standard log file on the BIG-IP system.
A BIG-IP Administrator is receiving intermittent reports from users that SSL connections to the BIG-IP device are failing. Upon checking the log files, the administrator notices: SSL transaction (TPS) rate limit reached. Reviewing stats shows a max of 1200 client-side SSL TPS and 800 server-side SSL TPS. What is the minimum SSL license limit capacity required to handle this peak?
Answer : D
Troubleshooting SSL connection resets often involves verifying license limits against actual resource utilization. F5 devices use a 'Transactions Per Second' (TPS) license to control the amount of SSL processing the device can handle. The log entry SSL transaction (TPS) rate limit reached is a clear indicator that the traffic volume has exceeded the licensed capacity. When determining the necessary license level, it is important to know that F5 primarily licenses and limits the 'Client-side' SSL TPS---which represents the encrypted connections between the users and the virtual servers. In this specific scenario, the peak demand reached 1200 client-side transactions per second. Although there were also 800 server-side transactions (re-encryption from the BIG-IP to the pool), these typically do not count against the primary TPS license limit in the same manner. Therefore, to ensure that the virtual server works as expected during peak load, the administrator must upgrade the license to at least 1200 TPS. This troubleshooting process links system log errors to license-enforced resource constraints.
During a high-demand traffic event, the BIG-IP Administrator needs to limit the number of new connections per second allowed to a Virtual Server. What should the administrator apply to accomplish this task?
Answer : D
F5 BIG-IP provides two distinct ways to throttle traffic on a Virtual Server: total capacity and velocity.
Connection Rate Limit: This setting specifically controls the number of new connection attempts per second. It is the correct tool for managing traffic spikes and protecting backend resources from being overwhelmed by a high frequency of new requests.
Comparison (Connection Limit): A standard Connection Limit (Option C) restricts the total concurrent connections allowed at any one time, regardless of how fast they arrive.
Other Profiles: OneConnect (Option A) is used for connection pooling and reuse to reduce server-side load, and HTTP Compression (Option B) reduces bandwidth usage but does not limit connection counts or rates.
Refer to the exhibit.

The BIG-IP Administrator has modified an iRule on one device of an HA pair. The BIG-IP Administrator notices there is NO traffic on the BIG-IP device in which they are logged into. What should the BIG-IP Administrator do to verify if the iRule works correctly?
Answer : D
Based on the provided exhibits, the BIG-IP device is currently in a Standby state ('ONLINE (STANDBY)') and has a sync status of 'Changes Pending' (Yellow icon).
Understanding Device State and Traffic: In an Active/Standby High Availability (HA) pair, traffic is processed by the Active device. The exhibit confirms the administrator is logged into the Standby device, which explains why there is 'NO traffic' currently observed on this specific unit.
Configuration Synchronization (ConfigSync): When an administrator modifies a local object, such as an iRule, on one member of a device group, the changes must be synchronized to the other members to ensure consistency. The 'Changes Pending' status indicates that the local configuration on this device is newer than the configuration on other group members.
Push vs. Pull: * Push: Sends the configuration from the current device to the other members of the device group.
Pull: Overwrites the current device's configuration with the configuration from another member of the group.
Resolving the Scenario: Since the administrator modified the iRule on 'this device,' they must Push the configuration to the group so the Active device receives the updated iRule. To verify the iRule works, the administrator can then monitor the traffic on the Active device or initiate a manual failover to make 'this device' Active, allowing it to process traffic with the new iRule.
Option D is the correct administrative workflow: synchronize the changes to the group (Push) and then monitor the traffic flow to validate the new logic.
A BIG-IP Administrator needs to collect HTTP status code and HTTP method for traffic flowing through a virtual server. Which default profile provides this information?
Answer : B
To gather granular Layer 7 data such as specific HTTP methods (GET, POST, etc.) and HTTP status codes (200, 404, 500), the BIG-IP system utilizes the Analytics (AVR) profile.
Analytics Profile (Application Visibility and Reporting): While a standard HTTP profile tracks basic byte counts and requests, the Analytics profile is designed specifically to capture, analyze, and display detailed application performance metrics.
Metrics Captured: When attached to a virtual server, it records URL-level statistics, response codes, page load times, and client-side metrics.
Why not others? * HTTP Profile (Option A): This profile handles the parsing of HTTP traffic but does not provide a built-in reporting dashboard for status code distribution.
Statistics Profile (Option C): This is a legacy profile used for custom user-defined counters and does not automatically categorize HTTP methods or status codes.
Request Adapt (Option D): This is used for integrating with ICAP servers (like virus scanners) and does not perform traffic reporting.
Clients report that they cannot reach the virtual server vs-production on port 80, but are able to ping the virtual server address. The configuration is shown below:
Plaintext
ltm virtual vs-production {
destination 10.99.20.50:http
ip-protocol tcp
mask 255.255.255.255
profiles {
http {}
tcp {}
}
source 192.168.0.0/16
translate-address enabled
translate-port enabled
vlans {
external
}
vlans-enabled
}
What is the cause?
Answer : D
The issue is caused by the Source Address restriction configured on the virtual server.
Source Filter: The configuration contains the line source 192.168.0.0/16. This acts as an implicit Access Control List (ACL). The virtual server will only accept and process TCP connections if the client's source IP address falls within the 192.168.x.x range.
Why Ping Works: ICMP (Ping) is handled by the Virtual Address object, not the Virtual Server object. Unless ICMP is specifically disabled on the Virtual Address, it will respond to pings from any subnet, even if the Virtual Server itself is restricted by a source filter or is even disabled.
Evaluation of Other Options:
Disabled (Option A): If the VS were disabled, the configuration would typically show disabled or state down, and the symptoms would be similar, but the source filter is a more specific 'misconfiguration' in this context.
Port 80 (Option C): The configuration destination 10.99.20.50:http explicitly confirms it is listening on port 80.
Unallowed Subnet: If a client from a different network (e.g., 10.10.1.5) tries to connect, the BIG-IP will silently drop the connection or send a reset because it does not match the defined source criteria.