Fortinet NSE 6 - FortiClient EMS 7.4 Administrator FCP_FCT_AD-7.4 Exam Questions
Why does FortiGate need the root CA certificate of FortiCient EMS?
Answer : A
Understanding the Need for Root CA Certificate:
The root CA certificate of FortiClient EMS is necessary for FortiGate to trust certificates issued by FortiClient EMS.
Evaluating Use Cases:
FortiGate needs the root CA certificate to establish trust and validate certificates issued by FortiClient EMS.
Conclusion:
The primary reason FortiGate needs the root CA certificate of FortiClient EMS is to trust certificates issued by FortiClient EMS.
FortiClient EMS and FortiGate certificate management documentation from the study guides.
Which statement about the FortiClient enterprise management server is true?
Answer : C
Which two statements about ZTNA destinations are true? (Choose two.)
Answer : C, D
When multitenancy is enabled on FortiClient EMS, which administrator role can provide access to the global site only? (Choose one answer)
Answer : B
According to the FortiClient EMS Administration Guide (specifically the sections on Multitenancy), when multitenancy is enabled, the system introduces specific administrator roles to manage the separation between global settings and individual sites.
1. The Settings Administrator Role (Answer B)
Specific Scope: The Settings administrator is a specialized role designed to have access to the global site only.
Permissions: This role can access all configuration options on the global site, with the notable exception of administrator configuration (they cannot create or manage other admin accounts).
Use Case: This is typically used for auditors or system managers who need to oversee global-level configurations without needing access to specific endpoint data within individual sites or the power to modify administrative users.
2. Comparison with Other Multitenancy Roles
Super administrator: This role has unlimited access to the global site and all other sites within the EMS instance.
Site administrator: This role is restricted to specified sites only and has no access to the global site.
Standard administrator (Answer C): This is a generic role level within a site or a single-tenant environment but is not the role that defines 'global-only' access in a multitenant setup.
Tenant administrator / Global administrator: While these terms are common in general IT, FortiClient EMS documentation specifically uses the titles Super, Settings, and Site administrators for multitenancy management.
3. Curriculum Reference
FortiClient EMS 7.2/7.4 Study Guide (Multitenancy Chapter): Explicitly lists 'Settings administrator' as the role providing access to the global site only.
Admin Roles Table: The documentation provides a comparison table where the Settings Administrator's scope is strictly defined as 'Global site only'.
Refer to the exhibit.
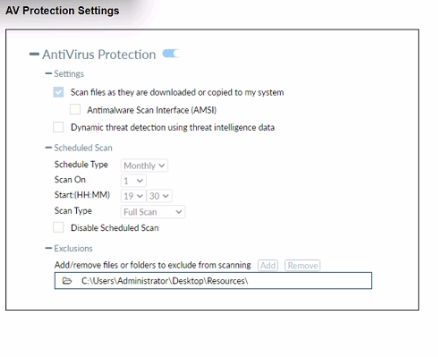
Based on The settings shown in The exhibit, which statement about FortiClient behaviour is Hue?
Answer : A
Based on the settings shown in the exhibit, FortiClient is configured toscan files as they are downloaded or copiedto the system. This means that if a user copies files to the ''Resources'' folder, which is not listed under exclusions, FortiClient will scan these files for infections. The exclusion path mentioned in the settings, 'C:\Users\Administrator\Desktop\Resources', indicates that any files copied to this specific folder will not be scanned, but since the question implies that the ''Resources'' folder is not the same as the excluded path, FortiClient will indeed scan the files for infections.
Which security attribute is verified during the SSL connection negotiation between FortiClient and FortiClient EMS to mitigate man-in-the-middle (MITM) attacks? (Choose one answer)
Answer : B
According to the FortiClient EMS Administrator Study Guide (7.2/7.4 versions) and the Fortinet Document Library regarding SSL/TLS Endpoint Communication Security, the primary attribute verified during the SSL connection negotiation to mitigate Man-in-the-Middle (MITM) attacks is the Common Name (CN).
1. SSL Connection Negotiation & MITM Mitigation
Verification Process: When FortiClient attempts to establish a Telemetry connection with the FortiClient EMS server, an SSL handshake occurs. To ensure it is communicating with the legitimate server and not a malicious interceptor (MITM), FortiClient verifies the server's certificate.
Role of the Common Name (CN): The Common Name (or the Subject Alternative Name - SAN) in the certificate must match the FQDN (Fully Qualified Domain Name) or the IP address that the client intended to connect to.
Security Enforcement: If the CN/SAN does not match the server's expected address, FortiClient will detect a discrepancy. Depending on the Invalid Certificate Action setting in the profile (e.g., Warn or Block), it will prevent the establishment of a secure session to stop the MITM attacker from masquerading as the EMS server.
2. Why Other Options are Incorrect/Secondary
A . Serial Number (SN): While every certificate has a unique Serial Number, it is primarily used by the Certificate Authority (CA) for tracking and revocation purposes. While FortiOS 7.2.4+ can use SN for certain restricted VPN checks, the core SSL negotiation mechanism for identifying a specific host to prevent spoofing relies on the CN/SAN fields.
C . Location (L) and D. Organization (O): These are descriptive fields within the certificate's Subject that provide geographical and corporate information. They are not functionally used by the SSL/TLS protocol to verify the identity of the host during the connection negotiation or to mitigate MITM attacks.
3. Curriculum Reference
EMS Administration Guide (System Settings Profile): Details how the client verifies the EMS server certificate. It specifies that for a connection to be trusted, the server address must align with the certificate's identity fields (CN/SAN).
FortiGate/FortiOS 7.2.4 New Features: Highlights the specific enhancement where FortiClient EMS connectors now 'trust EMS server certificate renewals based on the CN field' to ensure continuous secure communication.
Which two statements apply to FortiClient forensics analysis? (Choose two answers)
Answer : B, D
Based on the FortiClient EMS 7.2/7.4 Administrator Study Guide and the FortiGuard Forensics Service User Guide, the forensics analysis feature is a specialized service that requires specific administrative actions and configuration.
1. The Administrator Must Request Analysis (Answer B)
Manual Initiation: Unlike standard Antivirus or Sandbox scans which occur automatically upon detection, the FortiGuard Forensics Analysis is a service-based investigation.
Workflow: Once a threat is detected or a device is suspected of being compromised, the administrator must navigate to the Endpoints pane, select the specific device, and click the Request Analysis button.
Escalation: The administrator then fills out a questionnaire (providing the reason for escalation and issue summary) to submit the logs to the FortiGuard Labs forensic team for manual review.
2. Forensics Features Must be Enabled in the Profile (Answer D)
Two-Step Enabling:
Global Level: First, the feature must be toggled on under System Settings > Feature Select > FortiGuard Forensics Analysis.
Profile Level: Crucially, it must be enabled within the Endpoint Profile (specifically under System Settings) that is applied to the target endpoints.
Agent Deployment: Toggling this in the profile ensures the FortiClient endpoint prepares the 'forensics agent' components required to collect deep-system data (such as the Master File Table, Windows Event Logs, and registry hives) when a request is eventually made.
3. Why Other Options are Incorrect
A . FortiClient sends an alert notification: While FortiClient does send alerts for malicious activity, this is part of the standard Endpoint Control and Malware Protection modules. The forensics analysis itself is the follow-up investigation performed after such an alert is received and reviewed by an admin.
C . The endpoint is quarantined until completed: Although it is a security 'Best Practice' to quarantine a compromised endpoint during an investigation, the forensics analysis process does not programmatically force or require a quarantine state to function. The forensics agent can collect logs from an online, non-quarantined device as long as it has EMS connectivity.