Fortinet FCP - FortiSIEM 7.2 Analyst FCP_FSM_AN-7.2 Exam Questions
Refer to the exhibit.
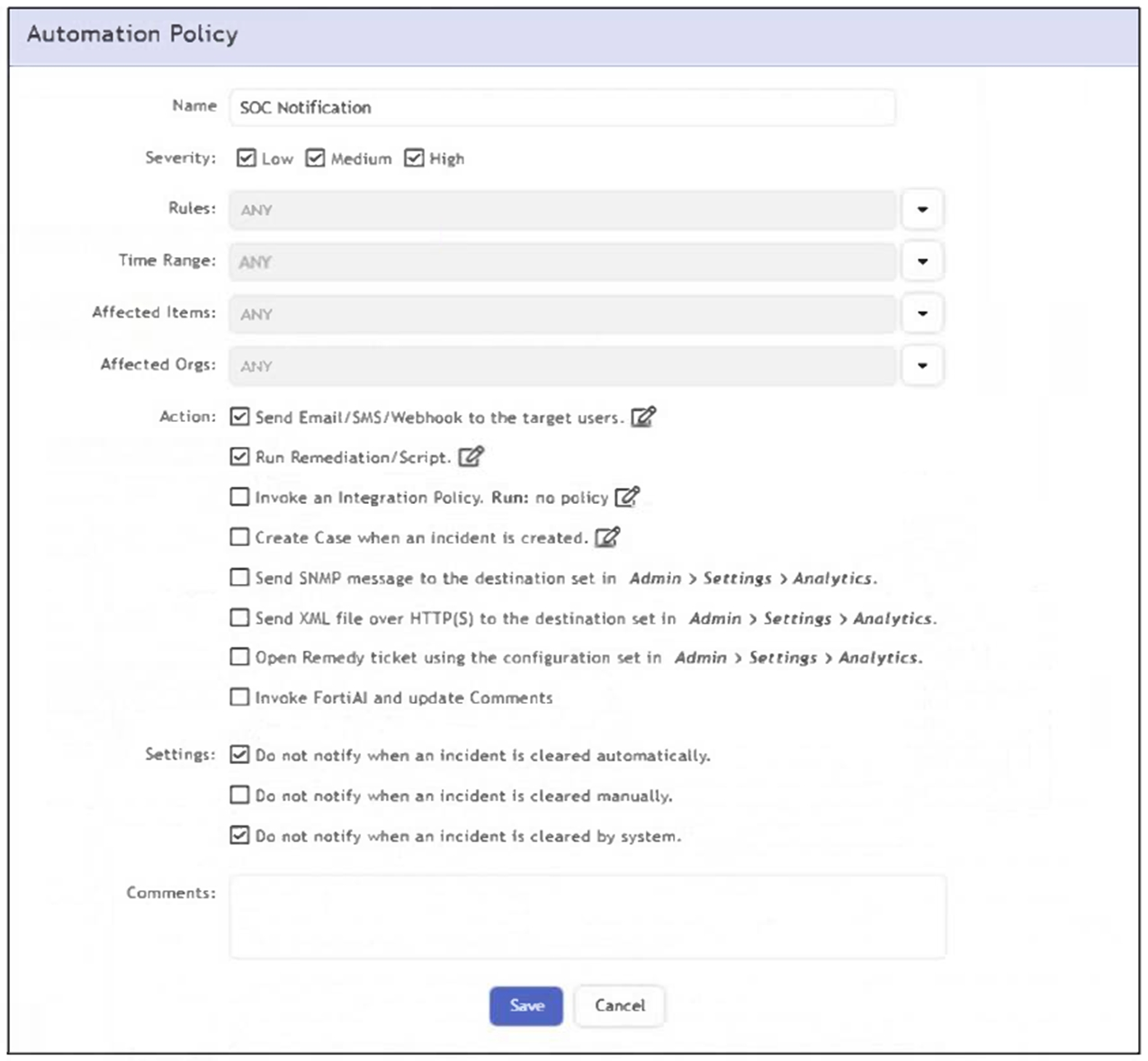
What happens when an analyst clears an incident generated by a rule containing the automation policy shown in the exhibit?
Answer : A
The automation policy has the option 'Do not notify when an incident is cleared manually' enabled. Therefore, when an analyst manually clears an incident, no notification or automation action is triggered.
Refer to the exhibit.
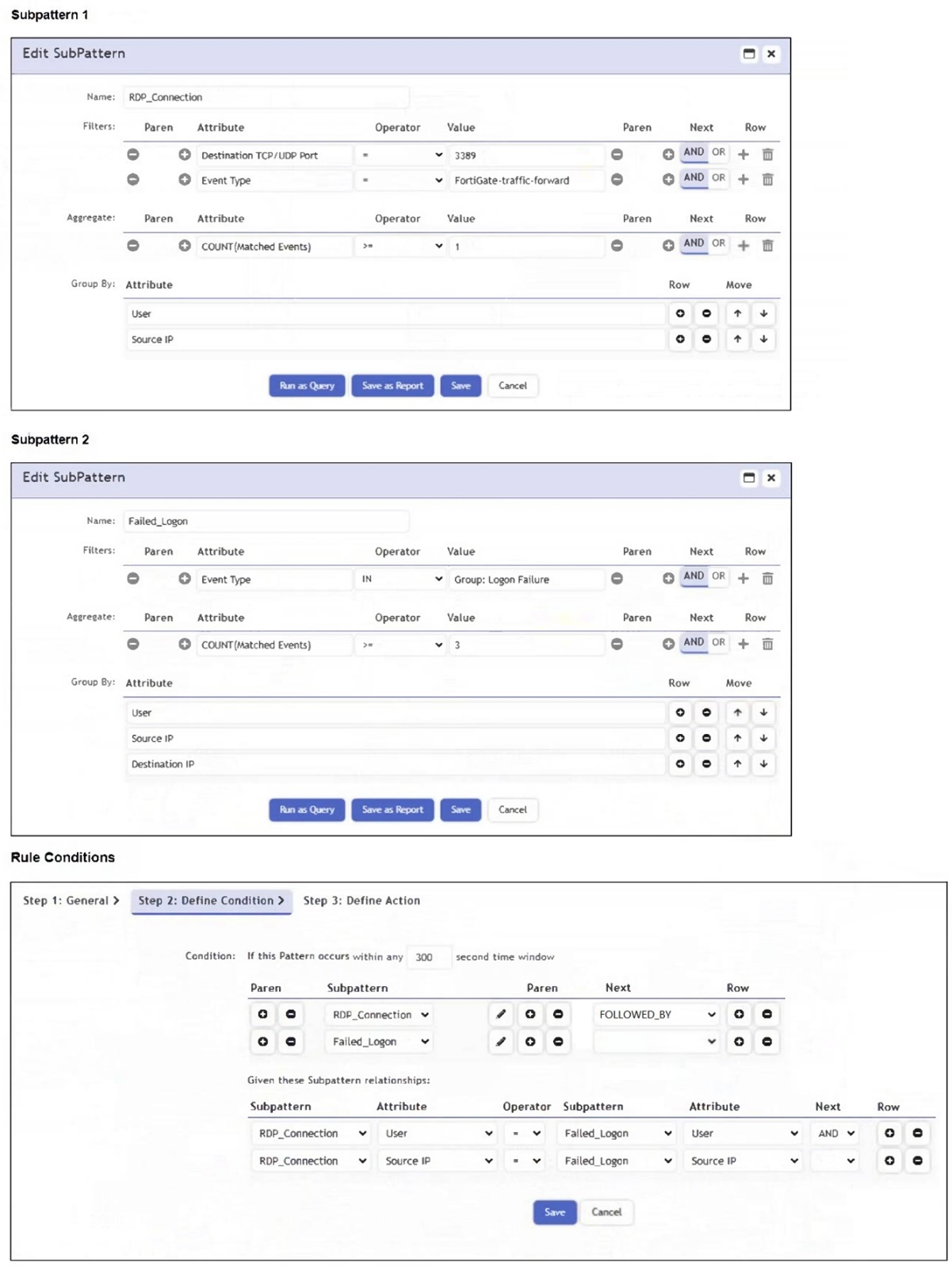
Which two conditions will match this rule and subpatterns? (Choose two.)
Answer : A, B
The user initiates an RDP session (Subpattern 1) and then fails to log in multiple times (Subpattern 2 with COUNT(Matched Events) >= 3) - both from the same Source IP and User within 300 seconds.
The brute force attempts typically involve a successful RDP connection followed by multiple failed logins, satisfying the sequence and grouping conditions in the rule.
Refer to the exhibit.
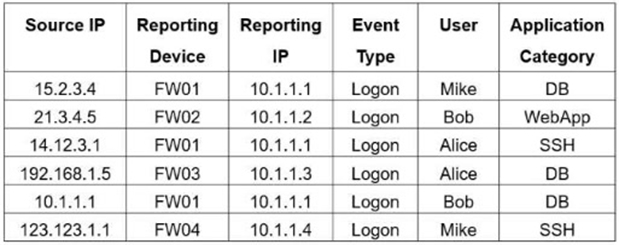
If you group the events by Reporting Device, Reporting IP, and Application Category, how many results will FortiSIEM display?
Answer : B
Grouping by Reporting Device, Reporting IP, and Application Category yields five unique tuples: (FW01, 10.1.1.1, DB), (FW02, 10.1.1.2, WebApp), (FW01, 10.1.1.1, SSH), (FW03, 10.1.1.3, DB), and (FW04, 10.1.1.4, SSH).
Refer to the exhibit.
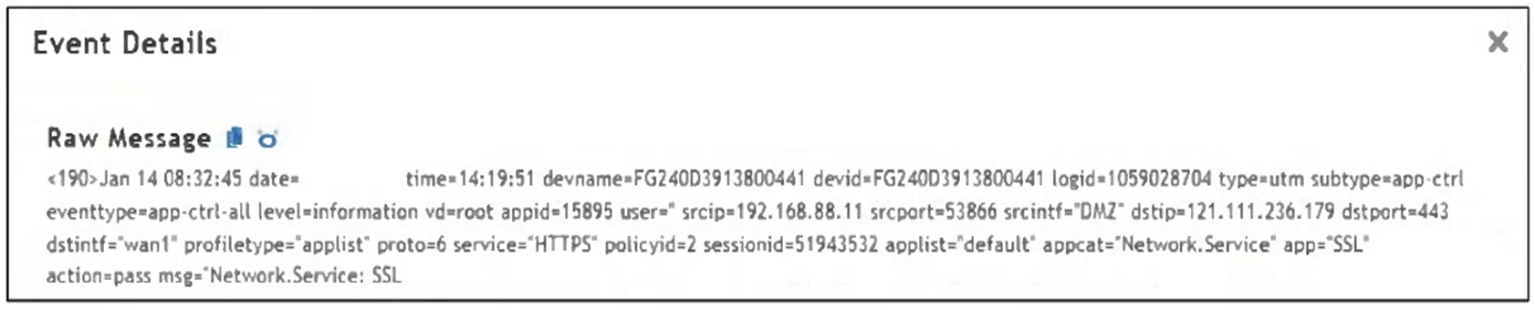
Which value would you expect the FortiSIEM parser to use to populate the Application Name field?
Answer : C
The Application Name field in FortiSIEM is typically populated using the value of the app field in the raw log. In this event, app='SSL', so 'SSL' is the expected application name parsed by FortiSIEM.
When configuring anomaly detection machine learning, in which step must you select the fields to analyze?
Answer : C
In the Prepare Data step of configuring anomaly detection in FortiSIEM, you must select the fields to analyze. This step defines the input features that the machine learning model will evaluate during training and detection.
Refer to the exhibit.
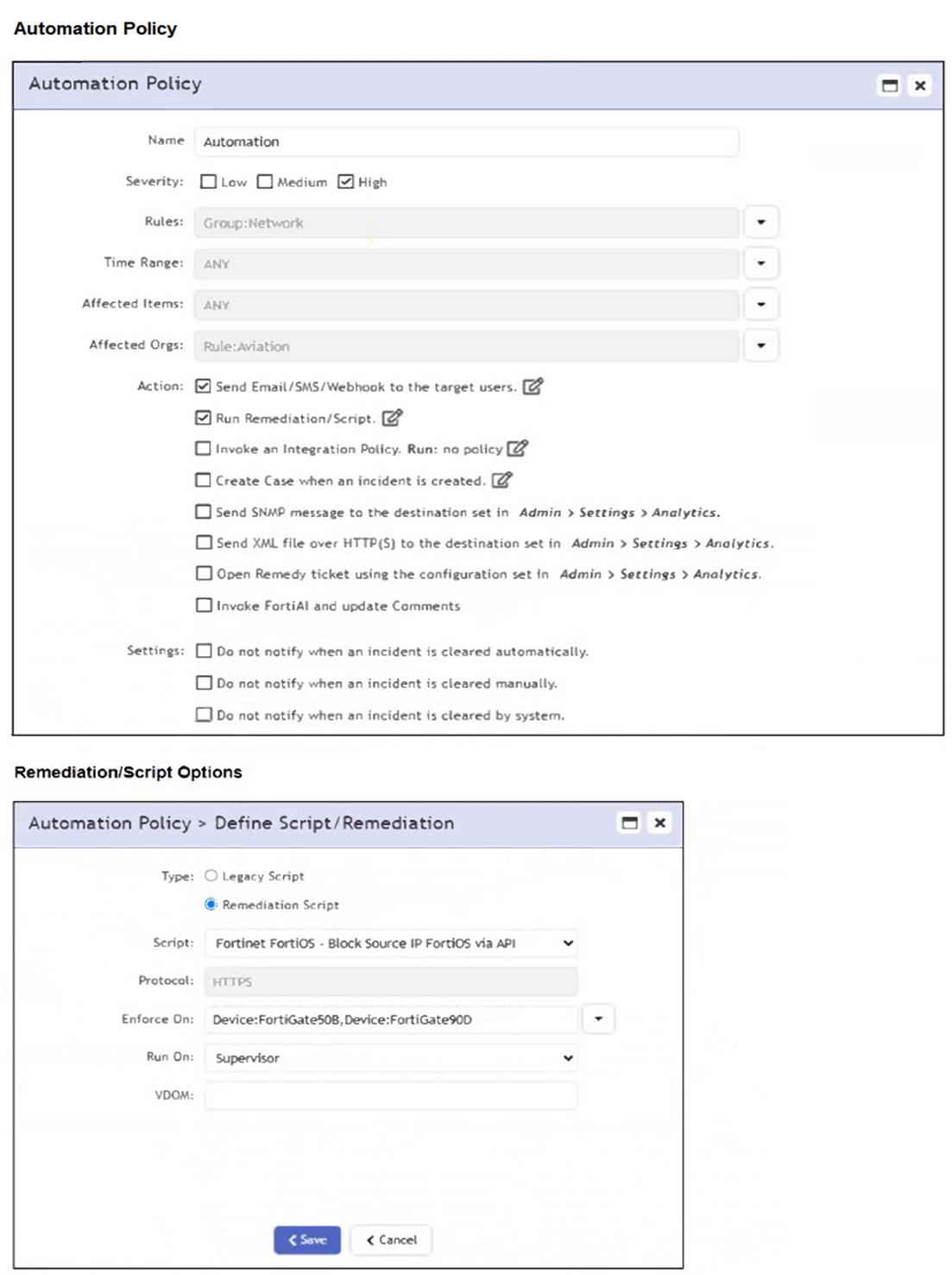
If a rule containing the automation policy shown in the exhibit triggers, what will happen?
Answer : D
The automation policy is configured to run a remediation script named 'Fortinet FortiOS - Block Source IP FortiOS via API'. It specifies enforcement on two FortiGate devices: FortiGate508 and FortiGate90D. Therefore, associated source IP addresses will be blocked on those two FortiGate firewalls only.
Refer to the exhibit.
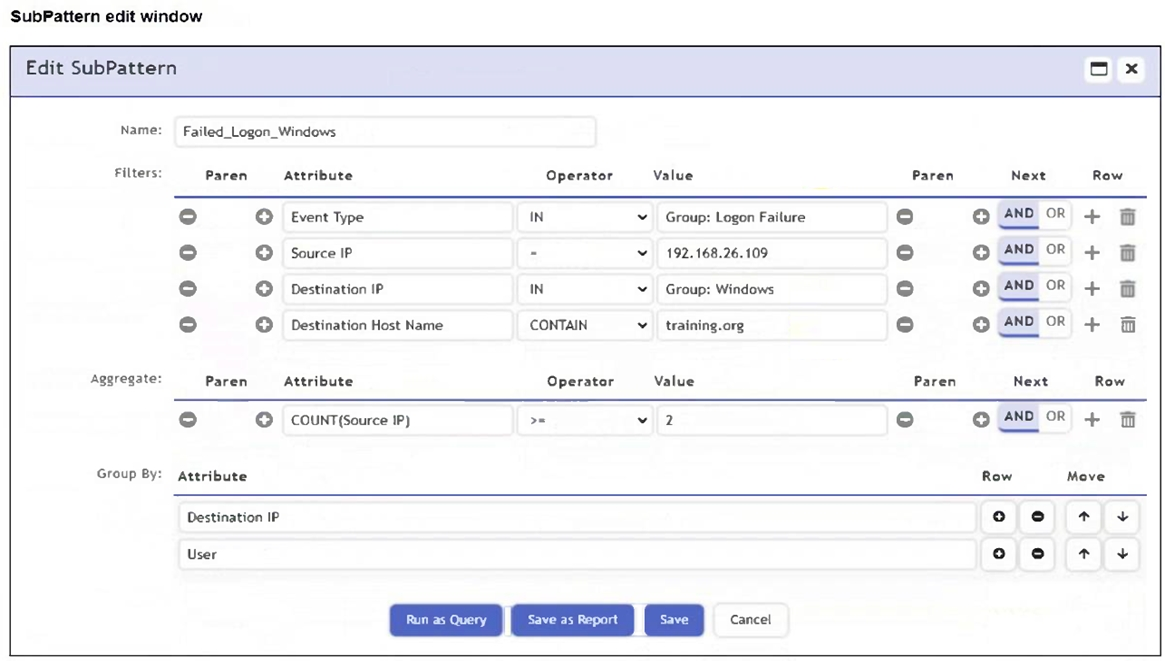
An analyst is troubleshooting the rule shown in the exhibit. It is not generating any incidents, but the filter parameters are generating events on the Analytics tab.
What is wrong with the rule conditions?
Answer : C
The Group By attributes - Destination IP and User - cause the aggregation (COUNT(Source IP) >= 2) to apply within each unique combination of those groupings. This restricts the count calculation and can prevent the rule from triggering incidents, even if matching events exist in the Analytics tab.