Fortinet FCP - FortiWeb 7.4 Administrator FCP_FWB_AD-7.4 Exam Questions
What are two results of enabling monitor mode on FortiWeb? (Choose two.)
Answer : A, D
It does not affect denial-of-service (DoS) protection profile actions to rate limit traffic: Monitor mode allows FortiWeb to monitor traffic without impacting the protection profile actions, including rate limiting in the DoS protection profiles. Traffic will still be subjected to DoS protection actions like rate limiting, but FortiWeb will not block traffic unless a violation occurs.
It overrides all usual profile actions. FortiWeb accepts all requests and generates alert email or log messages only for violations: In monitor mode, FortiWeb will allow all traffic through and generate logs or alerts for any violations, but it will not take active actions like blocking requests or redirecting traffic. This allows you to observe the traffic patterns and potential threats without disrupting normal operations.
An attacker attempts to send an SQL injection attack containing the known attack string 'root'; -- through an API call.
Which FortiWeb inspection feature will be able to detect this attack the quickest?
Answer : B
The quickest detection for an SQL injection attack like the one described ('root'; --) would be through known signatures. FortiWeb utilizes signature-based detection to match incoming traffic against predefined attack patterns. Since SQL injection attacks are commonly known and have specific patterns (such as 'root'; --), known signatures would immediately recognize and flag this type of attack.
A customer wants to be able to index your websites for search and advertisement purposes.
What is the easiest way to allow this on a FortiWeb?
Answer : A
The easiest way to allow a search engine indexer (such as Googlebot or Bingbot) to index your website on a FortiWeb is to add the indexer's IP address to the trusted IP list. This ensures that traffic from trusted indexers is allowed through without being blocked or interfered with by FortiWeb's security features like bot protection.
In which two operating modes can FortiWeb modify HTTP packets? (Choose two.)
Answer : B, D
Virtual proxy: In virtual proxy mode, FortiWeb acts as an intermediary between clients and the server, and it can modify HTTP packets. It performs various security checks, such as inspecting and filtering HTTP traffic before forwarding it to the web server.
Reverse proxy: In reverse proxy mode, FortiWeb sits between the client and the server, handling incoming requests from clients, modifying or inspecting HTTP packets as needed, and forwarding them to the backend servers.
Refer to the exhibit.
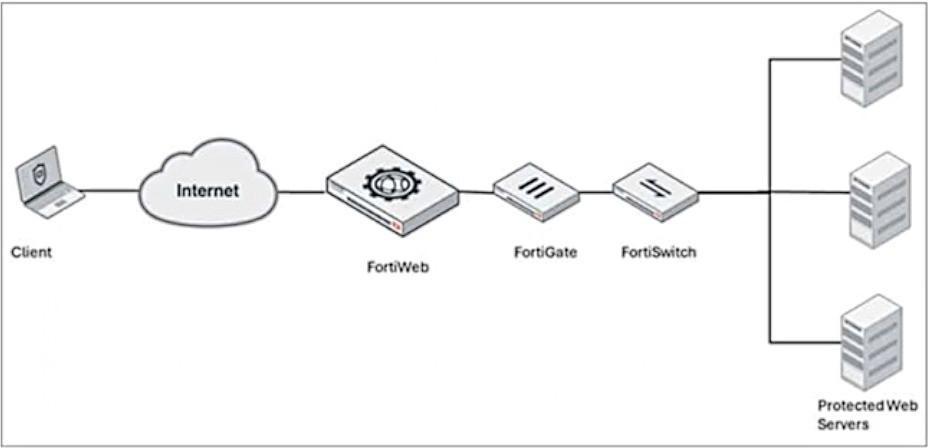
A FortiWeb device is deployed upstream of a device performing source network address translation (SNAT) or load balancing.
What configuration must you perform on FortiWeb to preserve the original IP address of the client?
Answer : A
When FortiWeb is deployed upstream of a device performing source network address translation (SNAT) or load balancing, the original client IP address may be lost. To preserve the original client IP address, you must enable and configure the Preserve Client IP setting on FortiWeb. This allows FortiWeb to retain and pass the client's original IP address to the backend servers for accurate logging and processing.
Which high availability mode is commonly used to integrate with a traffic distributer like FortiADC?
Answer : C
In Fortinet's high availability (HA) configurations, integrating FortiWeb with a traffic distributor like FortiADC is best achieved using the Active-Active HA mode. This mode allows multiple FortiWeb appliances to operate simultaneously, distributing traffic loads and enhancing both performance and redundancy.
FortiWeb supports several HA modes:
Active-Passive: One appliance actively handles all traffic, while the other remains on standby, ready to take over if the active unit fails.
Active-Active: Multiple appliances actively process traffic concurrently, sharing the load and providing redundancy.
High Volume Active-Active: An enhanced version of Active-Active, designed for environments with exceptionally high traffic volumes.
When integrating with a traffic distributor like FortiADC, the Active-Active mode is particularly advantageous. FortiADC can intelligently distribute incoming traffic across multiple active FortiWeb appliances, optimizing resource utilization and ensuring high availability. This setup not only balances the load but also provides fault tolerance; if one appliance becomes unavailable, FortiADC can redirect traffic to the remaining active units without service interruption.
This collaborative approach between FortiWeb and FortiADC ensures that web applications remain secure, performant, and resilient against failures.
Refer to the exhibits.

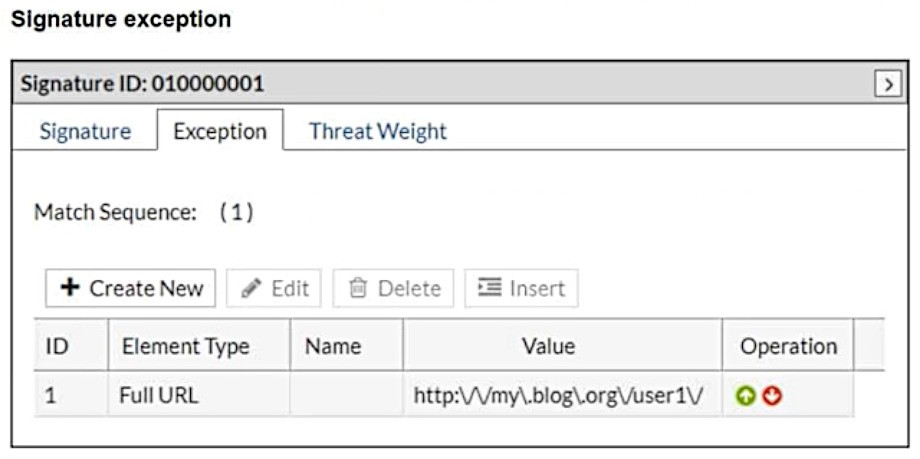
What will happen when a client attempts a mousedown cross-site scripting (XSS) attack against the site http://my.blog.org/userl1/blog.php and FortiWeb is enforcing the highlighted signature?
Answer : D
In the provided configuration, the signature exception has been set for the URL http://my.blog.org/user1V. This means that any request to this specific URL will bypass the signature ID 01000001, which is designed to block cross-site scripting (XSS) attacks using the mousedown event. As the request comes from the URL http://my.blog.org/userl1/blog.php, which does not match the exception rule for http://my.blog.org/user1V, the attack will be allowed through.
Therefore, the connection will be allowed because the exception rule bypasses protection for the specified URL.