Fortinet FCSS - SD-WAN 7.6 Architect FCSS_SDW_AR-7.6 Exam Questions
(When you deploy SD-WAN, you can choose from several common designs. Each design best applies to specific contexts.
Which two statements correctly associate a common SD-WAN design with its main indication or constraint? Choose two answers.)
Answer : A, C
The FCSS SD-WAN 7.6 curriculum describes multiple standard SD-WAN deployment designs, each mapped to a specific operational goal or constraint.
A cloud on-ramp topology is designed to optimize connectivity to cloud services such as SaaS and IaaS. This design provides the most efficient and reliable path to cloud applications by establishing direct tunnels to cloud gateways or cloud workloads and by avoiding backhauling traffic through a central data center. As a result, its primary indication is improving the performance of cloud applications, which makes option A correct.
A remote breakout (centralized breakout) design forwards all internet-bound traffic from branch sites to a central hub for security inspection. This allows security policies, inspection, and logging to be centralized on a high-capacity FortiGate at the hub. Because branch devices do not need advanced local security configurations, this design also limits local management requirements, which makes option C correct.
Option B is incorrect because a standalone SD-WAN design is not selected simply because a site has only one WAN link. SD-WAN provides its main benefits when multiple WAN paths exist, and single-link sites do not gain meaningful traffic-steering advantages.
Option D is incorrect because a direct internet access (DIA) design performs local internet breakout at the branch and therefore requires strong local security capabilities. DIA does not inherently increase traffic security and is not intended for devices with limited capabilities.
Therefore, the two correct associations are A and C.
Which three factors about SLA targets and SD-WAN rules should you consider when configuring SD-WAN rules? (Choose three.)
Answer : B, C, E
The use of SLA targets is specific to certain SD-WAN strategies. The 'Lowest Cost (SLA)' and 'Maximize Bandwidth (SLA)' strategies are explicitly designed to use the configured SLA targets to make routing decisions. The 'Best Quality' strategy uses performance metrics but does not necessarily require or reference SLA targets in the same way, while 'Manual' does not use metrics at all for path selection.
This is a core function of SD-WAN rules with SLA targets. The purpose of configuring an SLA target with specific thresholds for latency, jitter, and packet loss is to define what is considered 'acceptable' performance for an application. SD-WAN rules then use these targets to check if the members (interfaces) meet these requirements before a flow is steered over them, ensuring that a preferred path still offers a good user experience.
FortiGate allows for a single SD-WAN rule to reference multiple, different performance SLAs. This is crucial for complex deployments where a single SD-WAN rule needs to handle traffic for multiple applications that have distinct performance requirements. For example, a single rule might direct VoIP traffic based on one performance SLA with strict latency/jitter targets, while simultaneously handling general web traffic using another performance SLA with more lenient requirements.
Refer to the exhibits.
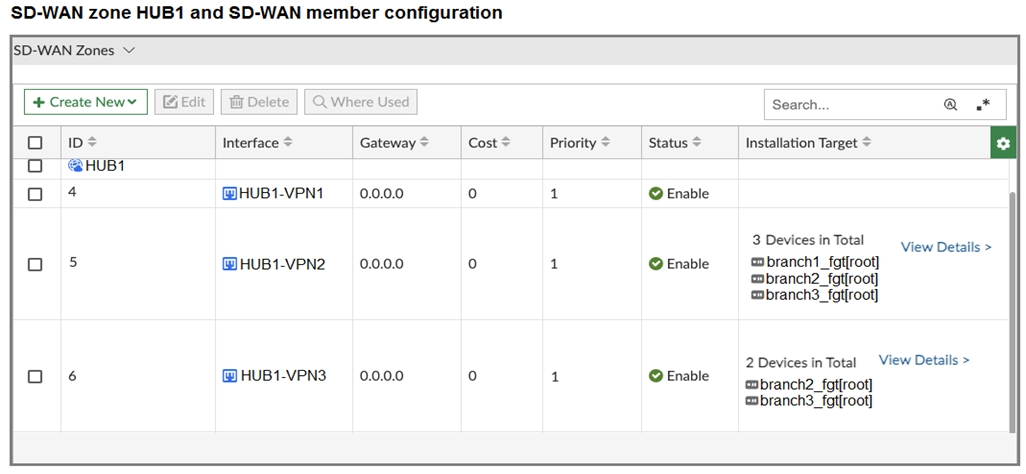
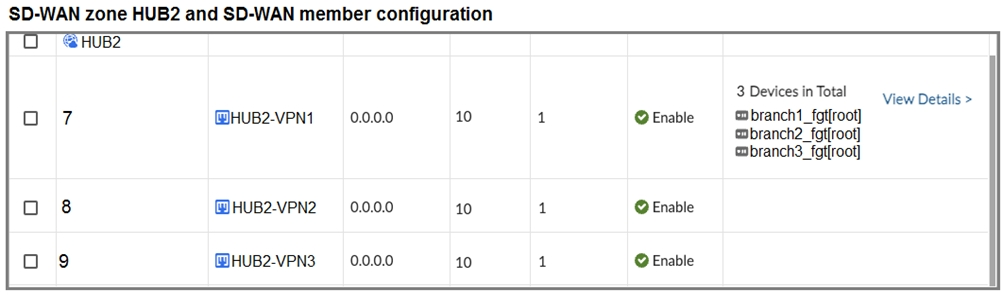
The first exhibit shows the SD-WAN zone HUB1 and SD-WAN member configuration from an SD-WAN template, and the second exhibit shows the output of command diagnose sys sdwan member collected on a FortiGate device.
Which statement best describes what the diagnose output shows?
Answer : D
The diagnose output lists SD-WAN members 4(HUB1-VPN1), 5(HUB1-VPN2), 7(HUB2-VPN1), 8(HUB2-VPN2), and 9(HUB2-VPN3). It does not include member 6 (HUB1-VPN3). From the template, HUB1-VPN3 is installed only on branch2_fgt and branch3_fgt - not on branch1_fgt. Therefore, the output must be from branch1_fgt.
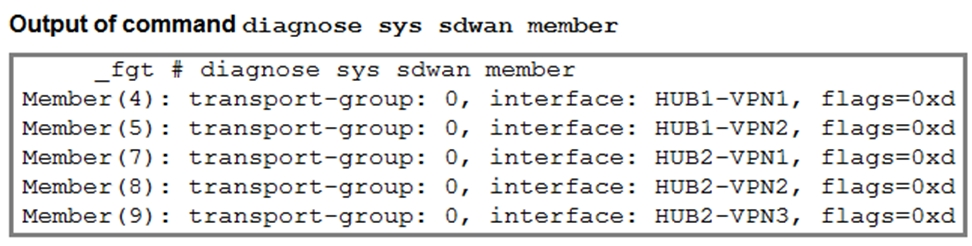
Refer to the exhibit.
The exhibit shows the health-check configuration on a FortiGate device used as a spoke. You notice that the hub FortiGate doesn't prioritize the traffic as expected.
Which two configuration elements should you check on the hub? (Choose two.)
Answer : C, D
The hub must use a performance SLA with the same criteria as the spoke's health check. The spoke's health check is using ping (protocol ping) and measuring latency (link-cost-factor latency). For the hub to use the data sent by the spoke, its performance SLA must be configured to measure the same metrics. If the hub is looking for jitter or packet loss, it will not use the latency data sent by the spoke.
When a spoke sends embedded health data, the hub FortiGate must be configured to receive and use it. This is done by setting set embedded-measure accept within the performance SLA configuration on the hub. This setting explicitly tells the hub to trust and use the performance metrics received from the remote FortiGate (the spoke). Without this setting, the hub will likely ignore the embedded health data and rely on its own health checks, which could lead to incorrect traffic prioritization.
Which statement describes FortiGate behavior when you reference a zone in a static route?
Answer : D
When referencing a zone in a static route, FortiGate's behavior is described as: 'Referencing a zone in a static route causes FortiGate to install a static route for each member interface of the zone. This enables ECMP (Equal-Cost Multi-Path) and load balancing where supported and ensures that traffic can be steered over any valid zone member according to SD-WAN rules or standard routing.' This mechanism is fundamental to Fortinet's implementation of SD-WAN and simplifies large, multi-interface deployments. Reference:
[FCSS_SDW_AR-7.4 1-0.docx Q21]
FortiOS 7.4 Routing Guide, ''Zone-based Routing and ECMP Behavior''
Refer to the exhibit.
You want to configure SD-WAN on a network as shown in the exhibit.
The network contains many FortiGate devices. Some are used as NGFW, and some are installed with extensions such as FortiSwitch. FortiAP. or Forti Ex tender.
What should you consider when planning your deployment?
Answer : B
In Fortinet SD-WAN, hubs should not have extensions like FortiSwitch, FortiAP, or FortiExtender installed, as these can affect hub functionality and scalability. While all device types can be included in the topology, the hubs must be 'clean' FortiGate devices without such extensions to ensure proper ADVPN and overlay management. Reference:
[FCSS_SDW_AR-7.4 1-0.docx Q3]
Fortinet SD-WAN Reference Architecture Guide 7.4 -- Hub requirements
As an MSSP administrator, you are asked to configure ADVPN on an existing SD-WAN topology. FortiManager manages the customer devices in a dedicated ADOM. The previous administrator used the SD-WAN overlay topology.
Which two statements apply to this scenario? (Choose two.)
Answer : B, D
When you enable ADVPN (auto-discovery VPN) in the overlay template, FortiManager automatically updates both the IPsec and BGP templates on the hub so that shortcut tunnels can be established dynamically.
ADVPN can be activated in the SD-WAN overlay template for any supported topology, including dual-hub primary--primary, not just single hub.