Fortinet NSE 4 - FortiOS 7.6 Administrator NSE4_FGT_AD-7.6 Exam Questions
Refer to the exhibits.
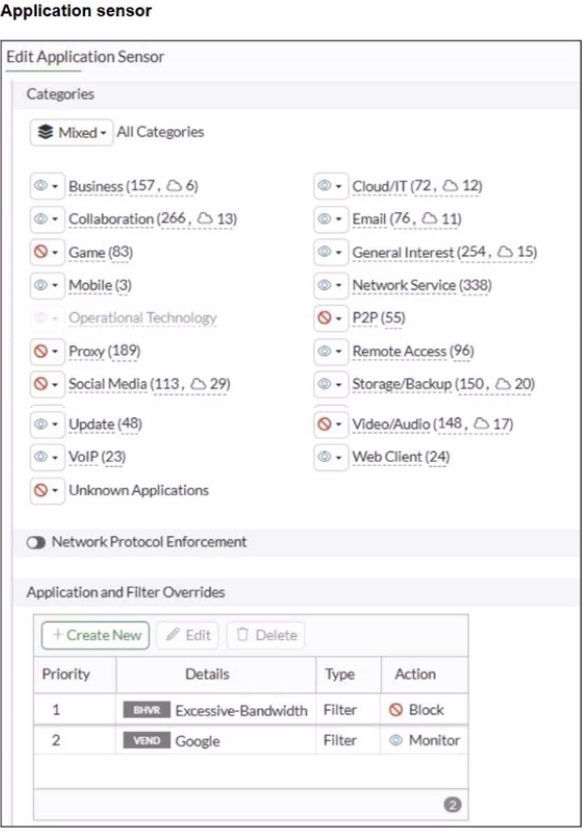
You have implemented the application sensor and the corresponding firewall policy as shown in the exhibits.
You cannot access any of the Google applications, but you are able to access www.fortinet.com.
Which two actions would you take to resolve the issue? (Choose two.)
Answer : B, E
From the exhibits:
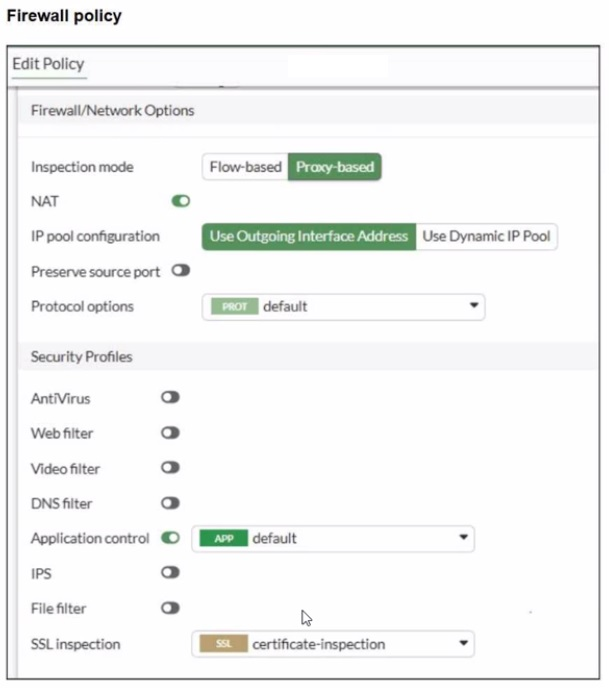
The firewall policy has Application Control enabled and uses certificate-inspection for SSL inspection.
The application sensor has Application and Filter Overrides with the following order (priority):
Excessive-Bandwidth with action Block
Google (vendor filter) with action Monitor
In FortiOS, Application and Filter Overrides are evaluated by priority (top-down). The first matching override is applied. If traffic matches an earlier override with Block, it will be blocked even if a later override would Monitor/Allow it.
Why Google apps fail while www.fortinet.com works:
Many Google applications can be detected as (or can trigger) the Excessive-Bandwidth behavior/signature depending on the specific service and traffic pattern.
Because Excessive-Bandwidth (Block) is above Google (Monitor), Google-related traffic may match the first rule and be blocked before the Google override is evaluated.
Access to www.fortinet.com works because that traffic is not matching the Excessive-Bandwidth override.
Therefore, to resolve:
B . Move up Google in the Application and Filter Overrides section to set its priority higher
This ensures Google matches the Google override before any broader blocking override is applied.
E . Set the action for Google in the Application and Filter Overrides section to Allow
This explicitly permits Google applications once the higher-priority match occurs (stronger than Monitor for troubleshooting and ensuring access).
Why the other options are not the best fit here:
A (deep-content inspection) can help identify more HTTPS applications, but the exhibit already shows a specific Google override configured; the immediate issue is the override evaluation order and action.
C relates to Web Filter URL categories, but the problem is occurring under Application Control behavior/vendor overrides.
D (flow-based) is not required to fix an override priority/action conflict.
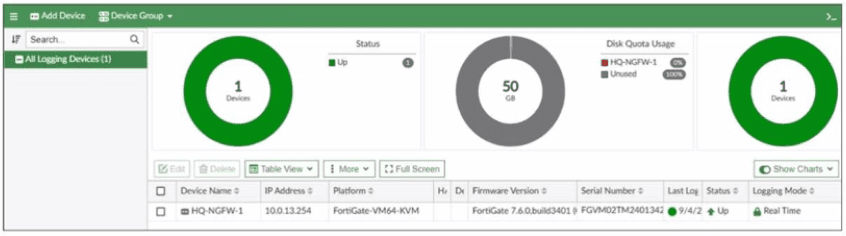
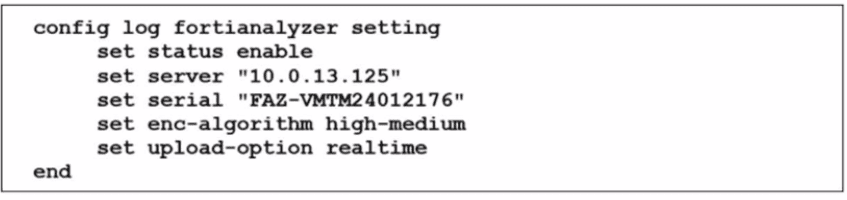
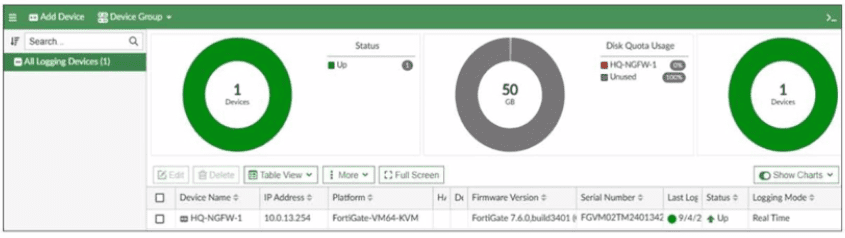
The FortiGate device HQ-NGFW-1 with the IP address 10.0.13.254 sends logs to the FortiAnalyzer device with the IP address 10.0.13.125. The administrator wants to verify that reliable logging is enabled on HQ-NGFW-1.
Which exhibit helps with the verification?
A)
B)
C)
D)
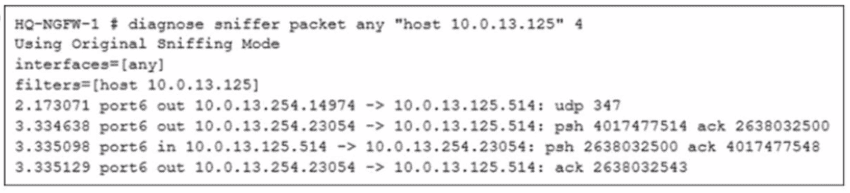
Answer : B
Refer to the exhibit.
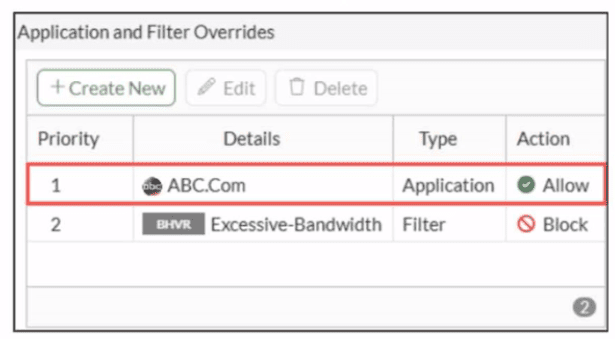
An administrator has configured an Application Overrides for the ABC.Com application signature and set the Action to Allow This application control profile is then applied to a firewall policy that is scanning all outbound traffic. Logging is enabled in the firewall policy. To test the configuration, the administrator accessed the ABC.Com web site several times.
Why are there no logs generated under security logs for ABC.Com?
Answer : D
In FortiOS 7.6 Application Control, security logs are generated primarily for actions such as Block or Monitor, not for Allow actions.
What is happening in the exhibit
An Application Override is configured for ABC.Com
Type: Application
Action: Allow
The application control profile is applied to a firewall policy
Logging is enabled on the firewall policy
Traffic to ABC.Com is successfully allowed
However, no security logs appear for ABC.Com.
Why no logs are generated
In FortiOS 7.6:
Application Control logs are written to Security Logs when:
An application is Blocked
An application is Monitored
When an application action is set to Allow:
The traffic is permitted silently
No application control security log is generated
Even if policy logging is enabled
This is expected and documented behavior.
To generate logs for allowed applications, the action must be set to Monitor, not Allow.
Why the other options are incorrect
A . ABC.Com is hitting the category Excessive-BandwidthIncorrect. ABC.Com has a higher-priority explicit override (priority 1), so it is not evaluated against the Excessive-Bandwidth filter.
B . The ABC.Com Type is set as Application instead of FilterIncorrect. Application-type overrides are valid and commonly used; this does not suppress logging.
C . The ABC.Com must be configured as a web filter profileIncorrect. This traffic is being evaluated by Application Control, not Web Filter.
Which three strategies are valid SD-WAN rule strategies for member selection? (Choose three answers)
Answer : A, B, D
According to the FortiOS 7.6 Administrator Study Guide and official documentation, SD-WAN rules (services) determine the path selection for traffic matching specific criteria. Version 7.6 provides specific flexibility regarding how these strategies handle multiple member interfaces.
First, Manual with load balancing (Statement B) is a valid configuration. In the Manual strategy, the administrator orders interfaces by preference, but by enabling the Load balancing toggle, the FortiGate can distribute traffic across all members that are up.
Second, the Lowest Cost (SLA) strategy has been enhanced to support two modes. When the load balancing option is disabled, it acts as Lowest Cost (SLA) without load balancing (Statement A), selecting the single lowest-cost link that meets the SLA. Alternatively, by enabling the toggle, it functions as Lowest Cost (SLA) with load balancing (Statement D), where the FortiGate distributes traffic across all interfaces that satisfy the SLA target, regardless of their individual costs.
Statements C and E are incorrect because 'Lowest Quality' is not a recognized SD-WAN strategy, and the Best Quality strategy is specifically a priority-based selection for a single 'best' link, meaning the load balancing toggle is not available in the GUI when this mode is selected.
Which statement correctly describes NetAPI polling mode for the FSSO collector agent?
Answer : B
NetAPI: Polls temporary sessions created on the DC when a user logs on or logs off and calls the NetSessionEnum function on Windows. It's faster than the WinSec and WMI methods; however, it can miss some logon events if a DC is under heavy system load. This is because sessions can be quickly created and purged form RAM, before the agent has a chance to poll and notify FG.
Which two components are part of the secure internet access (SIA) agent-based mode on FortiSASE? (Choose two.)
Answer : A, C
In FortiSASE Secure Internet Access (SIA) agent-based mode, traffic steering and security enforcement rely on components integrated with the FortiClient agent.
Components used in SIA agent-based mode
A . FortiSASE Firewall-as-a-Service (FWaaS)
Correct.
FWaaS is a core security component of FortiSASE.
It enforces firewall policies, security inspection, and access control for agent-based users.
All user traffic tunneled by the agent is inspected by FWaaS.
C . VPN policies
Correct.
In agent-based mode, the FortiClient establishes a secure tunnel to FortiSASE.
VPN policies define:
Authentication
Access control
Traffic steering
These policies are fundamental to agent-based connectivity.
Why the other options are incorrect
B . Proxy auto-configuration (PAC) filePAC files are used in agentless or proxy-based modes, not agent-based SIA.
D . FortiExtenderFortiExtender is a WAN extension device and is unrelated to FortiSASE SIA agent-based architecture.
Refer to the exhibits.
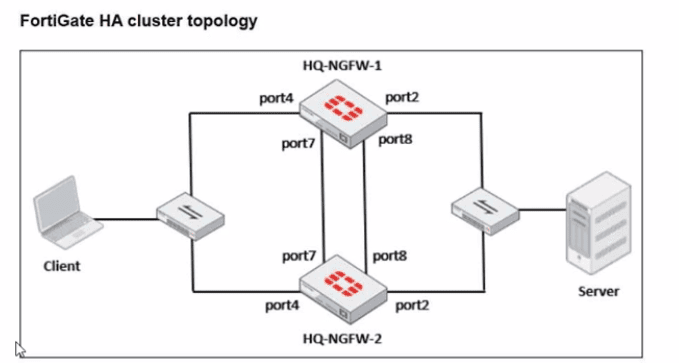
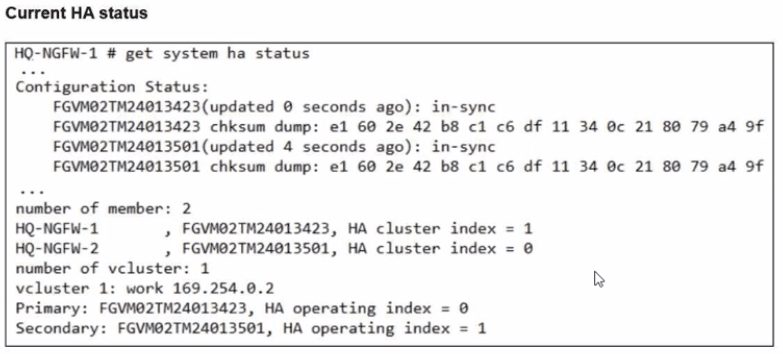
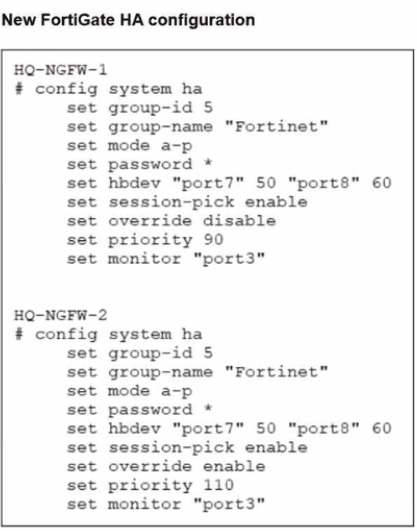
Based on the current HA status, an administrator updates the override and priority parameters on HQ-NGFW-1 and HQ-NGFW-2 as shown in the exhibits.
What would be the expected outcome in the HA cluster?
Answer : A
From the current HA status, HQ-NGFW-1 is the primary and HQ-NGFW-2 is the secondary.
The administrator then changes these HA parameters:
HQ-NGFW-1: set override disable, set priority 90
HQ-NGFW-2: set override enable, set priority 110
In FGCP (A-P mode), the override (preemption) feature controls whether a higher-priority unit is allowed to take over the primary role.
When override is enabled, the cluster will prefer (and can re-elect) the unit with the highest device priority to become primary (preempting a lower-priority primary when conditions trigger re-election behavior as defined by FGCP).
Here, HQ-NGFW-2 has:
override enabled
higher priority (110) than HQ-NGFW-1 (90)
Therefore, the expected result is that HQ-NGFW-2 becomes the primary.
Why the other options are incorrect:
B is incorrect because it claims HQ-NGFW-2 has lower priority (it is higher: 110 > 90).
C is incorrect because a mismatch in the override setting is not what causes the ''configuration out of sync'' condition shown in get system ha status (that is about synchronized configuration databases, not a requirement that override values must match to remain in-sync).
D is incorrect because HA settings like override/priority are not synchronized in the way regular configuration objects are; they are device-level HA parameters.