Fortinet NSE 5 - FortiSIEM 6.3 NSE5_FSM-6.3 Exam Questions
An administrator is investigating the slow performance of a FortiSlEM device.
Which command provides information about the CPU usage of FortiSlEM processes, disk usage, and EPS?
Answer : B
What are two tasks that you must do to make a secondary FortiSIEM device ready for disaster recovery? (Choose two.)
Answer : A, D
In me FortiSIEM CLI. which command must you use to determine whether or not syslog is being received from a network device?
Answer : A
Syslog Reception Verification: To verify whether syslog messages are being received from a network device, a network packet capture tool can be used.
tcpdump Command: tcpdump is a powerful command-line packet analyzer tool available in Unix-like operating systems. It allows administrators to capture and analyze network traffic.
Usage: By using tcpdump with the appropriate filters (e.g., port 514 for syslog), administrators can monitor the incoming syslog messages in real-time to verify if they are being received.
Example Command: tcpdump -i <interface> port 514 captures the syslog messages on the specified network interface.
Reference: FortiSIEM 6.3 User Guide, CLI Commands section, which details the usage of tcpdump for network traffic analysis and verification of syslog reception.
Refer to the exhibit.
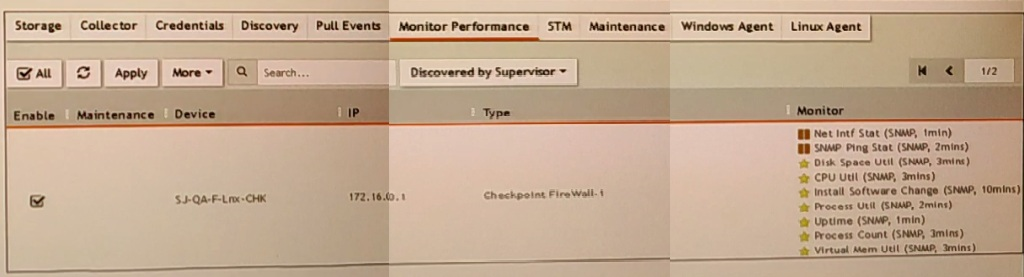
What do the yellow stars listed in the Monitor column indicate?
Answer : B
Monitor Column Indicators: In FortiSIEM, the Monitor column displays the status of various metrics applied during the discovery process.
Yellow Star Meaning: A yellow star next to a metric indicates that the metric was successfully applied during discovery and data has been collected for that metric.
Successful Data Collection: This visual indicator helps administrators quickly identify which metrics are active and have data available for analysis.
Reference: FortiSIEM 6.3 User Guide, Device Monitoring section, which explains the significance of different icons and indicators in the Monitor column.
When configuring collectors located in geographically separated sites, what ports must be open on a front end firewall?
Answer : B
FortiSIEM Architecture: In FortiSIEM, collectors gather data from various sources and send this data to supervisors and workers within the FortiSIEM architecture.
Communication Requirements: For collectors to effectively send data to the FortiSIEM system, specific communication channels must be open.
Port Usage: The primary port used for secure communication between the collectors and the FortiSIEM infrastructure is HTTPS (port 443).
Network Configuration: When configuring collectors in geographically separated sites, the HTTPS port must be open for the collectors to communicate with both the supervisor and the worker upload settings addresses. This ensures that the collected data can be securely transmitted to the appropriate processing and analysis components.
Reference: FortiSIEM 6.3 Administration Guide, Network Ports section details the necessary ports for communication within the FortiSIEM architecture.
Which protocol do collectors use to communicate with a FortiSIEM cluster?
Answer : C
Where must you configure rule notifications and automated remediation on FortiSIEM?
Answer : B