Fortinet NSE 5 - FortiSwitch 7.6 Administrator NSE5_FSW_AD-7.6 Exam Questions
You are deploying a multitier FortiSwitch topology with redundant links between access and aggregation switches. The team is considering Multiple Spanning Tree Protocol (MSTP) to manage spanning tree across multiple VLANs. Which two Rapid STP (RSTP) features would be useful in this deployment to ensure fast convergence and predictable port roles? (Choose two answers)
Answer : A, D
According to theFortiSwitchOS 7.6 Administration Guideand theFortiSwitch 7.6 Study Guide, Multiple Spanning Tree Protocol (MSTP) is built directly upon the foundations ofRapid Spanning Tree Protocol (RSTP), inheriting its mechanisms for fast convergence and fault recovery.12
In a multitier deployment (Access, Aggregation, and Core)3, theprocess for selecting the root bridge (Option A)is a fundamental RSTP feature that MSTP utilizes to create a stable and predictable logical topolog4y. By configuring the Bridge ID (priority and MAC address), administrators can manually ensure that the aggregation or core switches act as the Root Bridge for specific MST instances. This placement is critical for ensuring that traffic follows the most efficient physical paths and that high-bandwidth aggregation links are utilized effectively rather than blocked by suboptimal root selection.
Furthermore, therules for determining port roles (Option D)are essential for achieving the 'Rapid' part of the protocol. RSTP/MSTP defines specific port roles such asRoot,Designated,Alternate, andBackup. Unlike legacy STP, which relies on slow listening and learning timers, RSTP uses the Alternate and Backup roles to identify secondary paths that are already in a 'blocking' state but ready to transition to 'forwarding' immediately through a proposal/agreement handshake if a primary link fails. This mechanism allows for sub-second convergence times in redundant multitier environments. While Option B (recalculating paths) occurs, it is the role-based synchronization process that characterizes the modern protocol's speed, making A and D the most relevant 'useful features' for predictability and speed in this context.
Refer to the exhibit.
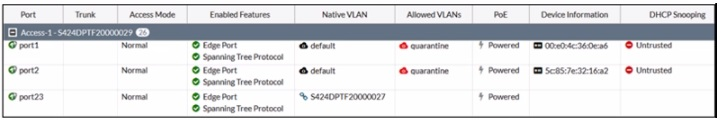
The exhibit shows the current status of the ports on the managed FortiSwitch. Access-1.
Why would FortiGate display a serial number in the Native VLAN column associated with the port23 entry?
Answer : D
The information in the 'Native VLAN' column for port23 on the FortiSwitch indicates that a standalone switch is connected to it. This is because the column displays '$424MPTF20000027,' which matches the format of a Fortinet device serial number.
Here's a breakdown of the evidence in the image:
Native VLAN:The 'Native VLAN' column typically displays the VLAN ID for untagged traffic on a trunk port. However, in this case, it shows a serial number format ('$424MPTF20000027').
No Trunk Information:The 'Trunk' column is blank for port23, indicating it's not configured as a trunk member.
Other Ports:Port1 and port2 show 'default' in the 'Native VLAN' column, which is the expected behavior for access ports.
Fortinet FortiSwitch devices typically don't display the serial number of adjacent FortiSwitch devices in the 'Native VLAN' column. This column is reserved for VLAN information on trunk ports.
Refer to the exhibits.
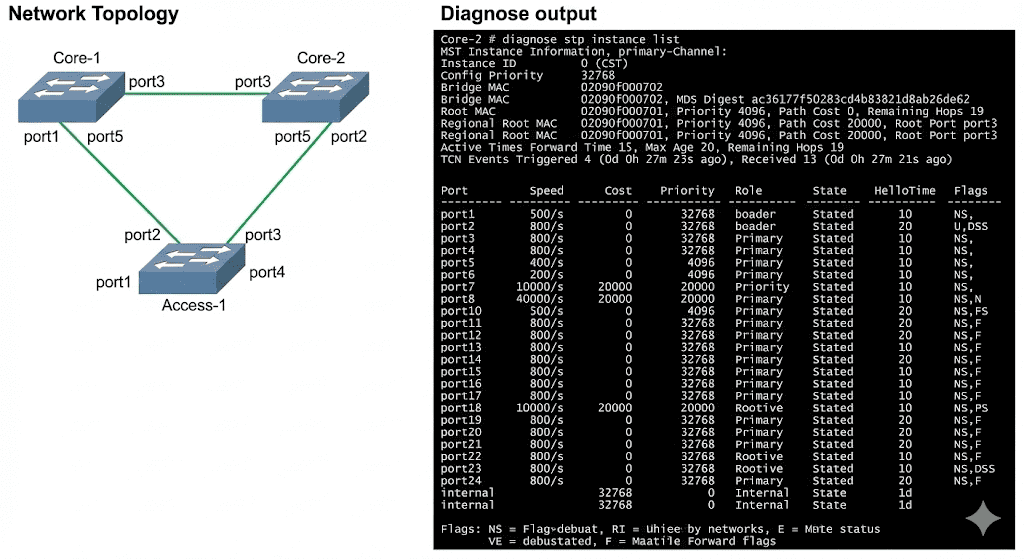
Three FortiSwitch devices in standalone mode are interconnected. The CLI command diagnose stp instance list is executed on Core-2. Based on the output shown in the exhibit, what can you conclude about Core-2? (Choose one answer)
Answer : A
According to theFortiSwitchOS 7.6 Administration Guideand theFortiSwitch 7.6 Study Guide, the output of the diagnose stp instance list command provides critical information about the Spanning Tree Protocol (STP) state of a switch within a given instance. In the provided exhibit, the output forInstance ID 0 (CST)onCore-2shows several key indicators of its role and connectivity within the STP topology.
First, the output explicitly identifies aRootbridge with MAC address 02090f000701 and a priority of 4096. Core-2 itself has a MAC address of 02090f000702 and a priority of 32768. Because Core-2 knows the MAC address and priority of the Root bridge, it must have received this information viaBridge Protocol Data Units (BPDUs). Furthermore, the port table shows thatport3on Core-2 has been assigned the role ofROOTand is in theFORWARDINGstate. In STP/RSTP, a Root Port is the port on a non-root switch that has the lowest path cost to the root bridge. To elect a Root Port and maintain its state, the switch must continuously receive BPDUs from the root bridge (or a bridge closer to the root) on that port.
Option B is incorrect because Core-2 has aRoot Port, which is only present on non-root bridges. Option C is incorrect because ports 1, 2, 4, 5, and the internal port are all in theFORWARDINGstate. Option D is incorrect as the output does not show any ports in anALTERNATErole; all active ports are either ROOT or DESIGNATED. Therefore, the most accurate conclusion is that Core-2 has successfully received BPDUs to identify the root and determine its own port roles.
How does FortiSwitch perform actions on ingress and egress traffic using the access control list (ACL)?
Answer : D
In FortiSwitch, Access Control Lists (ACLs) are used to enforce security rules on both ingress and egress traffic:
ACL Evaluation Order (D):
Operational Function:FortiSwitch processes ACL entries from top to bottom, similar to how firewall rules are processed. The first match in the ACL determines the action taken on the packet, whether to allow or deny it, making the order of rules critical.
Configuration Advice:Careful planning of the order of ACL rules is necessary to ensure that more specific rules precede more general ones to avoid unintentional access or blocks.
Which interfaces on FortiSwitch send out FortiLink discovery frames by default in order to detect a FortiGate with an enabled FortiLink interface?
Answer : A
Fortinet FortiLink Protocol:The FortiLink protocol is Fortinet's proprietary mechanism for managing FortiSwitch units from a FortiGate firewall. It simplifies configuration and security policy enforcement across the connected network devices.
Auto-Discovery:FortiLink's auto-discovery feature means that by default, all ports on a FortiSwitch will actively send out discovery frames. This allows them to locate a FortiGate device that has a FortiLink interface enabled, streamlining the device management process.
No Configuration Needed:You don't have to manually configure individual ports for FortiLink discovery on FortiSwitch devices.
Reference
FortiSwitchOS FortiLink Guide (FortiSwitch Devices Managed by FortiOS 7.6):Refer to pages 13 and 14 for details on zero-touch management and FortiLink configuration. [https://fortinetweb.s3.amazonaws.com/docs.fortinet.com/v2/attachments/27f63c72-b083-11ec-9fd1-fa163e15d75b/FortiSwitchOS-7.6.0-FortiLink_Guide%E2%80%94FortiSwitch_Devices_Managed_by_FortiOS_7.6.pdf]
Which statement about the configuration of VLANs on a managed FortiSwitch port is true?
Answer : C
The native VLAN is implicitly part of the allowed VLAN on the port (C): On a managed FortiSwitch port, the native VLAN, which is the VLAN assigned to untagged traffic, is implicitly included in the list of allowed VLANs. This means it does not need to be explicitly specified when configuring VLAN settings on the port. This configuration simplifies VLAN management and ensures that untagged traffic is handled correctly without additional configuration steps.
Refer to the exhibit.
What two conclusions can be made regarding DHCP snooping configuration? (Choose two.)
Answer : B, D
Based on the DHCP snooping configuration details provided in the exhibit:
B . FortiSwitch is configured to trust DHCP replies coming on FortiLink interface.The configuration segment shows 'trusted ports : port2 FlInK1 MLAG0,' indicating that the FortiSwitch is configured to trust DHCP replies coming from the specified ports, including the FortiLink interface labeled FlInK1. This setup is critical in environments where the FortiLink interface connects directly to a trusted device, such as a FortiGate appliance, ensuring that DHCP traffic on these ports is considered legitimate.
D . Global configuration for DHCP snooping is set to forward DHCP client requests on all ports in the VLAN.The 'DHCP Broadcast Mode' set to 'All' under the DHCP Global Configuration indicates that DHCP client requests are allowed to broadcast across all ports within the VLAN. This setting is essential for environments needing broad DHCP client servicing across multiple access ports without restriction, facilitating network connectivity and management.