Fortinet NSE 5 - FortiSASE and SD-WAN 7.6 Core Administrator NSE5_SSE_AD-7.6 Exam Questions
What is the purpose of the on/off-net rule setting in FortiSASE?
Answer : C
According to the FortiSASE 24.4 Administration Guide and the FortiSASE Core Administrator training materials, the On-net detection rule setting is a critical component for determining the 'trust status' of an endpoint's physical location.
Endpoint Location Verification: On-net rule sets are used to determine if FortiSASE considers an endpoint to be on-net (trusted) or off-net (untrusted). An endpoint is considered on-net when it is physically located within the corporate network, which is assumed to already have on-premises security measures (like a FortiGate NGFW).
Operational Impact: When an endpoint is detected as on-net, FortiSASE can be configured to exempt the endpoint from automatically establishing a VPN tunnel to the SASE cloud. This optimization prevents redundant security inspection and conserves SASE bandwidth since the user is already protected by the local corporate firewall.
Detection Methods: To classify an endpoint as on-net, administrators configure rule sets that look for specific environmental markers, such as:
Known Public (WAN) IP: If the endpoint's public IP matches the corporate headquarters' egress IP.
DHCP Server: If the endpoint receives an IP from a specific corporate DHCP server.
DNS Server/Subnet: Matching internal DNS infrastructure or specific internal IP ranges.
Dynamic Policy Application: By accurately determining if an endpoint is on or off-net, FortiSASE ensures that the FortiClient agent only initiates its secure internet access (SIA) tunnel when the user is in an untrusted location (e.g., a home network or public Wi-Fi).
Why other options are incorrect:
Option A: User authentication is a separate process and is not controlled by the on/off-net detection rules, which focus on the network environment rather than user credentials.
Option B: While on-net status affects how traffic is routed (VPN vs. local), these rules specifically determine the status itself rather than defining the routing tables for private vs. cloud resources.
Option D: Geographical location (Geo-location) is a different filtering criterion often used in firewall policies; on-net detection is specifically about the proximity to the trusted corporate perimeter.
What is a key use case for FortiSASE Secure Internet Access (SIA) in an agentless deployment? (Choose one answer)
Answer : B
According to the FortiSASE 7.6 Administration Guide and the FCP - FortiSASE 24/25 Administrator curriculum, the Agentless deployment mode---commonly referred to as Secure Web Gateway (SWG) mode---is a vital component of the Secure Internet Access (SIA) framework.
Deployment Mechanism: In an agentless deployment, FortiSASE functions as an explicit web proxy. This is achieved by distributing a PAC (Proxy Auto-Configuration) file to the user's browser, which instructs the device to send its web traffic to the nearest FortiSASE Point of Presence (PoP).
Target Use Case: This mode is specifically designed for unmanaged endpoints, such as those used by contractors, partners, or temporary workers, where the organization does not have the authority or capability to install the FortiClient agent.
Security Capabilities: Even without an agent, FortiSASE applies a full security stack to the redirected traffic. This includes Web Filtering, Anti-Malware, SSL Inspection, and Inline-CASB to secure HTTP and HTTPS sessions.
Protocol Limitations: Because it relies on proxy settings, this mode is limited to web protocols (HTTP/HTTPS) and does not inherently secure non-web traffic like ICMP, DNS, or custom TCP/UDP applications unless they are specifically proxied.
Why other options are incorrect:
Option A: While it provides secure browsing, session isolation (RBI) is a specific feature that can be used in either mode; the defining characteristic of the agentless use case is the proxy-based redirection for unmanaged devices.
Option C: A PAC file can only secure web traffic (protocols that support proxying), not non-web traffic protocols.
Option D: Agentless mode is the opposite of requiring FortiClient; ZTNA tags generally require the FortiClient agent to provide the necessary telemetry for tag evaluation.
Refer to the exhibit.
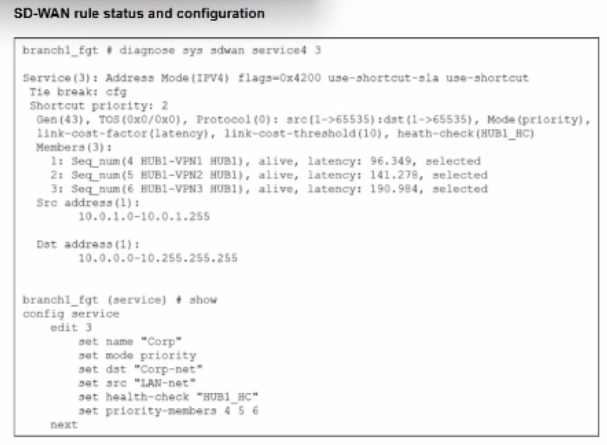
The SD-WAN rule status and configuration is shown. Based on the exhibit, which change in the measured latency will first make HUB1-VPN3 the new preferred member?
Answer : A
According to the SD-WAN 7.6 Core Administrator study guide and the FortiOS 7.6 Administration Guide, the selection of a preferred member in a Best Quality (priority) rule is determined by the measured quality metric (latency, in this case) and the link-cost-threshold.
Rule Logic (Best Quality): In the exhibit, the SD-WAN rule is configured with set mode priority, which corresponds to the Best Quality strategy. This strategy ranks members based on the link-cost-factor, which is set to latency.
The Link-Cost-Threshold: The exhibit shows link-cost-threshold(10), which is the default 10% value. This threshold is designed to prevent 'link flapping'. To replace the current preferred member, a new member must not only have a better latency but must be better by more than 10%.
The Calculation:
The current preferred member is HUB1-VPN1 with a real latency of 96.349 ms.
To calculate the 'target' latency a lower-priority member must achieve to take over, we use the formula: $Target = \frac{Current\_Latency}{(1 + \frac{Threshold}{100})}$.
$\frac{96.349}{1.1} = \mathbf{87.59\text{ ms}}$.
Evaluating Options:
Option A (80 ms): Since 80 ms is lower than the required 87.59 ms target, HUB1-VPN3 successfully overcomes the 10% advantage of HUB1-VPN1 and becomes the new preferred member.
Option D (90 ms): While 90 ms is lower than 96.349 ms, it is not lower than 87.59 ms. Therefore, the 10% threshold prevents a member switch, and HUB1-VPN1 remains preferred.
Option B: Incorrect because having a 'lower' latency is not enough due to the 10% threshold.
Option C: If HUB1-VPN1 moved to 200 ms, HUB1-VPN2 (at 141.278 ms) would likely become the new preferred member before HUB1-VPN3 (at 190.984 ms).
Which FortiSASE feature monitors SaaS application performance and connectivity to points of presence (POPs)?
Answer : D
According to the FortiSASE 7.6 Administration Guide and Digital Experience Monitoring (DEM) documentation, the feature specifically designed to monitor SaaS application performance and connectivity to PoPs is Digital Experience Monitoring (DEM).
SaaS and Path Visibility: DEM assists administrators in troubleshooting remote user connectivity issues by providing enhanced health check visibility for SaaS applications, endpoint devices, and the network path. It provides real-time insights into application performance and latency issues.
PoP Connectivity: It monitors the digital journey from the end-user device through the Security Points of Presence (POPs) to the final application, identifying hops where degraded service (packet loss, delay, or jitter) is detected.
Proactive Management: By establishing thresholds and simulating user activities through Synthetic Transaction Monitoring (STM), DEM allows IT teams to identify performance problems before they impact the business.
Why other options are incorrect:
Option A: Operations widgets provide general status overviews but do not offer the granular per-hop path analysis or specific SaaS transaction monitoring found in DEM.
Option B: FortiView dashboards provide traffic visibility and session data but are not dedicated performance monitoring tools for end-to-end digital experience.
Option C: Event logs record system occurrences and security events but do not provide real-time performance metrics or health check probes for SaaS applications.
Which configuration is a valid use case for FortiSASE features in supporting remote users?
Answer : C
According to the FortiSASE 7.6 Architecture Guide and FCP - FortiSASE 24/25 Administrator materials, the solution is built around three primary use cases that support a hybrid workforce:
Secure Internet Access (SIA): This enables secure web browsing by applying security profiles such as Web Filter, Anti-Malware, and SSL Inspection in the SASE cloud. It protects remote users from internet-based threats regardless of their location.
Secure Private Access (SPA): This provides granular, explicit access to private applications hosted in data centers or the cloud. It is achieved through ZTNA (Zero Trust Network Access) for session-based security or through SD-WAN integration where FortiSASE acts as a spoke to an existing corporate SD-WAN hub.
SaaS Security: FortiSASE utilizes Inline-CASB and Shadow IT visibility to monitor and control the use of cloud applications. Data Loss Prevention (DLP) is integrated into these workflows to prevent sensitive corporate data from being uploaded to unauthorized SaaS platforms.
Why other options are incorrect:
Option A: While it mentions SD-WAN and Shadow IT, it misses the core definition of SIA (secure web browsing) which is the primary driver for SASE deployments.
Option B: Remote Browser Isolation (RBI) is typically applied to risky or uncategorized websites, not 'all websites,' due to the high performance and resource overhead.
Option D: FortiSASE is designed to protect data in motion (via security profiles) as well as data stored in sanctioned cloud apps, not 'at rest only'.
Which three factors about SLA targets and SD-WAN rules should you consider when configuring SD-WAN rules? (Choose three answers)
Answer : B, D, E
According to the SD-WAN 7.6 Core Administrator study guide and the Fortinet Document Library, the interaction between SD-WAN rules and SLA targets is governed by specific selection and measurement logic:
Usage by Strategy (Option B): SLA targets are fundamentally used by the Lowest Cost (SLA) strategy to determine which links are currently healthy enough to be considered for traffic steering. While other strategies like Best Quality use a 'Measured SLA' to monitor metrics, they do not typically use the 'Required SLA Target' to disqualify links unless specifically configured in a hybrid mode. In most curriculum contexts, the 'Required SLA Target' field is specifically associated with the Lowest Cost and Maximize Bandwidth strategies.
SLA Compliance Checking (Option D): SD-WAN rules utilize SLA targets as a 'pass/fail' gatekeeper. The engine checks if the preferred members meet the defined SLA requirements (latency, jitter, or packet loss thresholds). If a preferred member fails the SLA, the rule will move to the next member in the priority list that does meet the SLA.
Single SLA Binding (Option E): When configuring an SD-WAN rule, the GUI and CLI allow you to select multiple SLA targets, but they must all belong to the same Performance SLA profile. You cannot mix and match targets from different health checks (e.g., Target 1 from 'Google_HC' and Target 2 from 'Amazon_HC') within a single SD-WAN rule.
Why other options are incorrect:
Option A: This is incorrect because a single SD-WAN rule can only be associated with one specific Performance SLA profile at a time; therefore, you cannot select targets from different SLAs.
Option C: This is incorrect because member metrics (latency, jitter, packet loss) are measured by the Performance SLA probes regardless of whether an SD-WAN rule is currently using that SLA target for steering decisions. Measurement is a function of the health-check, not the rule matching process.
Which three authentication sources support secure identity verification and access control for FortiSASE remote users? (Choose three.)
Answer : A, C, E