Fortinet NSE 6 - FortiMail 7.2 NSE6_FML-7.2 Exam Questions
Refer to the exhibit which shows the Authentication Reputation list on a gateway mode FortiMail device.

Why was the IP address blocked?
Answer : C
Refer to the exhibits, which display a topology diagram (Topology) and two FortiMail device configurations (FML1 Configuration and FML2 Configuration).
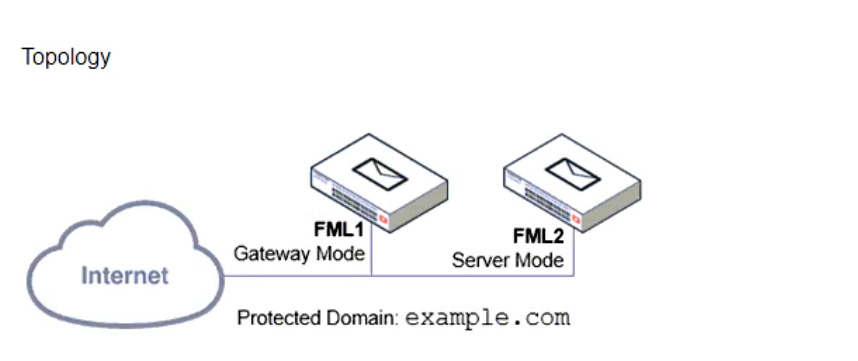
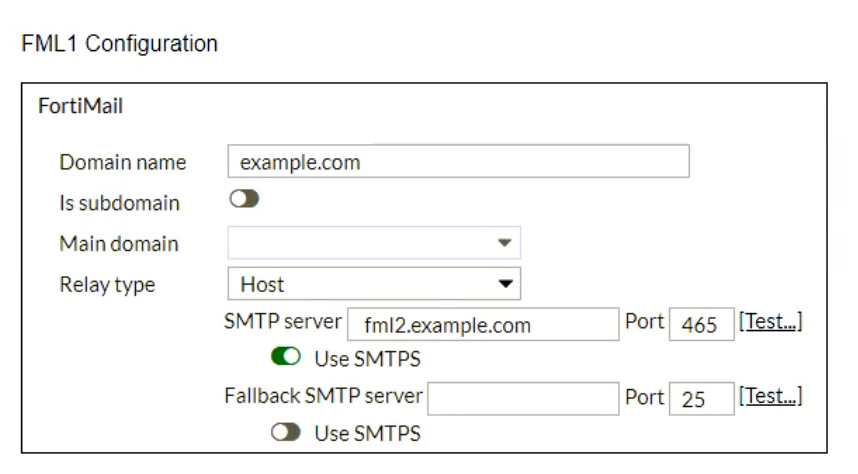
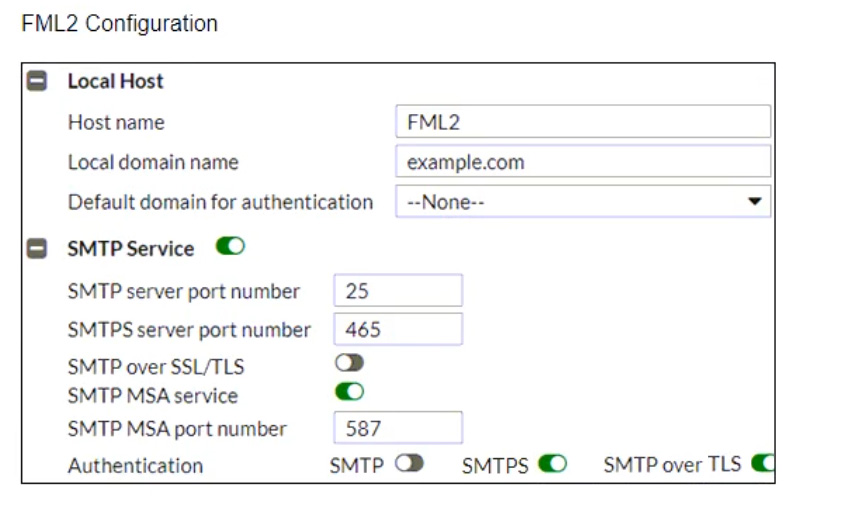
What is the expected outcome of SMTP sessions sourced from FML1 and destined for FML2?
Answer : D
A FortiMail is configured with the protected domain example.com.
On this FortiMail, which two envelope addresses are considered incoming? (Choose two.)
Answer : A, C
Refer to the exhibit, which shows an inbound recipient policy.
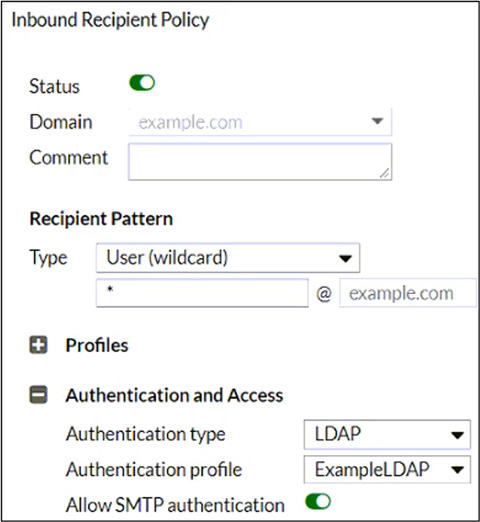
After creating the policy shown in the exhibit, an administrator discovers that clients can send unauthenticated emails using SMTP.
What must the administrator do to enforce authentication?
Answer : D
Refer to the exhibits which show a topology diagram (Topology), and a configuration element (Access Control Rule).
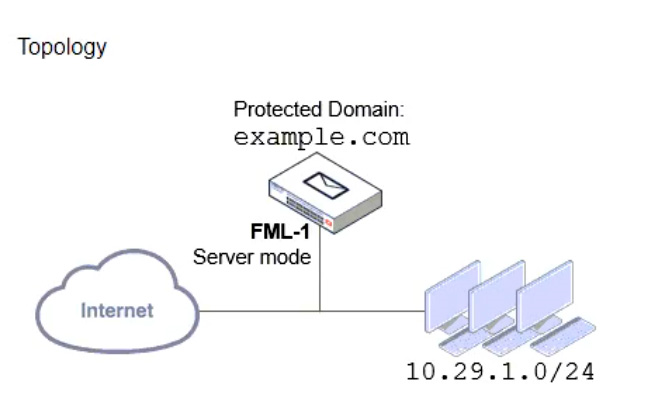
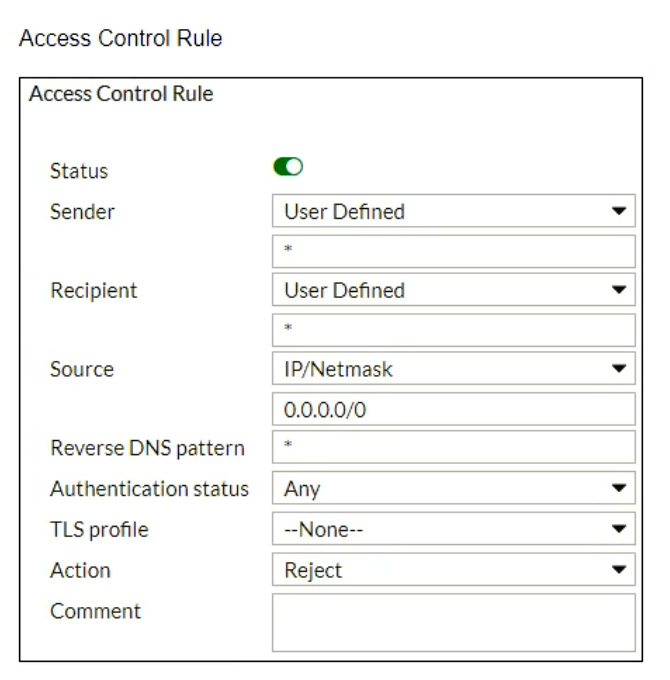
An administrator must enforce authentication on FML-1 for all outbound email from the example.com domain.
Which two settings should be used to configure the access receive rule? (Choose two.)
Answer : A, D
A FortiMail administrator is concerned about cyber criminals attempting to get sensitive information from employees using whaling phishing attacks. What option can the administrator configure to prevent these types of attacks?
Answer : A
Refer to the exhibit, which shows a few lines of FortiMail logs.
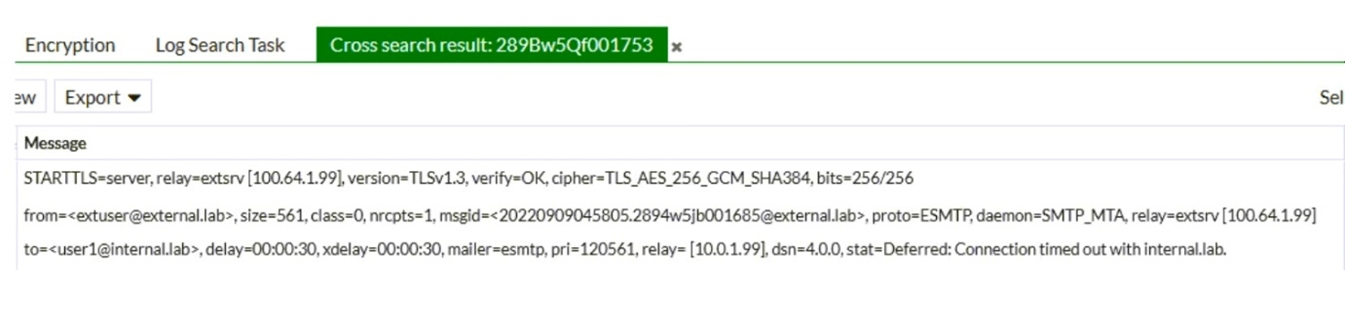
Based on these log entries, which two statements correctly describe the operational status of this FortiMail device? (Choose two.)
Answer : A, C