Fortinet NSE 6 - FortiNAC 9.1 NSE6_FNC-9.1 Exam Questions
Which three circumstances trigger Layer 2 polling of infrastructure devices? (Choose three.)
Answer : A, B, E
Which three of the following are components of a security rule? (Choose three.)
Answer : C, D, E
Where should you configure MAC notification traps on a supported switch?
Answer : D
Where do you look to determine when and why the FortiNAC made an automated network access change?
Answer : B
Study Guide p. 356: Any time FortiNAC changes network access for an endpoint, the change is documented on the Port Changes view. This provides an administrator with valuable information when validating control configurations and enforcement.
What would occur if both an unknown (rogue) device and a known (trusted) device simultaneously appeared on a port that is a member of the Forced Registration port group?
Answer : C
Refer to the exhibit, and then answer the question below.
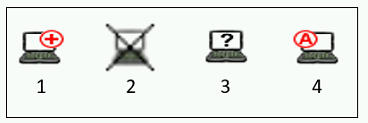
Which host is rogue?
Answer : B
Which two agents can validate endpoint compliance transparently to the end user? (Choose two.)
Answer : B, D