Fortinet NSE 6 - OT Security 7.6 Architect NSE6_OTS_AR-7.6 Exam Questions
For the installation of your first FortiGate device, you want to minimize the impact in your OT network. Therefore, you deploy it initially as an offline IDS. Which two statements about this deployment are correct? (Choose two answers)
Answer : A, B
Deploying a FortiGate in offline IDS (also known as one-arm sniffer mode) is a common strategy in OT environments for several reasons found in the study guide:
Priority of Availability: In OT, availability and safety are critically important and prioritized higher than in IT. An offline IDS minimizes impact because it does not sit in the direct path of production traffic.
Network Sensor Role: In this mode, the FortiGate is connected to a mirror/SPAN port on a switch. It acts as a network sensor, receiving a copy of the traffic rather than having the traffic flow through it. This confirms Statement A is correct and Statement D is incorrect.
Passive vs. Active: The guide explicitly states that in OT environments, passive methods are preferred over active methods to avoid negatively impacting performance or causing process interruptions.
Depth of Visibility: Even though the device is offline, you apply security profiles (such as IPS, Application Control, and Antivirus) to the sniffer interface. This allows the FortiGate to analyze the copied traffic and provide deep visibility into the OT assets and their behaviors. This confirms Statement B is correct.
Detection vs. Prevention: An IDS (Intrusion Detection System) is passive; it can detect threats but cannot reset connections or drop packets to block attacks. Therefore, it cannot block zero-day attacks, making Statement C incorrect.
According to the IEC 62443 standard, your security level is 4. What is your OT environment defending against? (Choose one answer)
Answer : C
According to the OT Security 7.6 Architect study guide regarding IEC 62443 Security Levels:
Security Level 4 (SL 4) Definition: This level provides 'Protection against intentional violation using sophisticated means with extended resources, specific skills, and high motivation'.
Real-World Application: The study guide specifically notes: 'If you are facing a syndicate of cyber extortionists with extensive resources and capabilities, then you should strive for security level 4'.
Comparison to other levels:
SL 1: Protection against 'casual or unintentional system violation'.
SL 2: Protection against 'intentional violation using simple means with low resources'.
SL 3: Protection against 'intentional violation using sophisticated means with moderate resources'.
Refer to the exhibit. A partial OT network is shown. You must improve the security of this OT network and implement internal segmentation between network 1 and network 2. How can you achieve the segmentation? (Choose one answer)
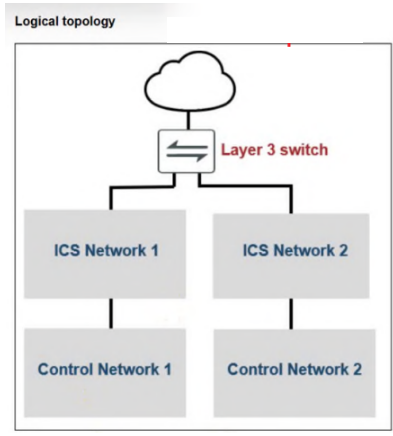
Answer : D
The correct answer is D. You can configure forward domain IDs for each network. The study guide explains that in FortiGate transparent mode, ''all interfaces belong to the same broadcast domain, even interfaces with different VLAN IDs'' and then states that you should ''use this command to subdivide into multiple broadcast domains'' with set forward-domain <domain_ID>. It further explains that ''interfaces with the same domain ID belong to the same broadcast domain'' and ''traffic arriving on one interface is broadcast only to interfaces in the same forward domain ID.'' This is exactly the mechanism used to separate one internal network from another and improve segmentation.
The other options do not match this requirement. Universal ZTNA is described as controlling user access to applications, not segmenting two internal OT networks. An explicit software switch is for controlling intra-switch or intra-VLAN traffic inside the same software switch broadcast domain, which is more aligned with microsegmentation than separating two routed internal networks. One traffic VDOM does not create segmentation by itself; segmentation with VDOMs requires multiple VDOMs, not one. Therefore, the best choice for segmenting network 1 and network 2 in this scenario is to assign separate forward domain IDs.
Refer to the exhibit.
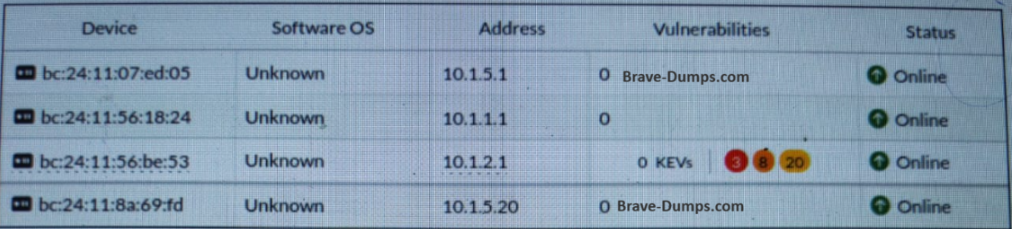
Which statement about this partial Asset Identity List page is correct? (Choose one answer)
Answer : B
Based on the OT Security 7.6 Architect study guide regarding the Asset Identity Center and Asset Management:
Vulnerability Visibility: The Asset Identity List tab displays key metadata for IT and OT devices, including detected addresses, users, and a specific column for Vulnerabilities.
Virtual Patching Feature: In the OT Security 7.6 architecture, the 'Vulnerabilities' column is populated through the OT Security Service license, which includes 'OT vulnerability correlation definitions & virtual patching signatures'.
Correlation Mechanism: FortiGate extracts metadata from OT traffic and uses these signatures to identify known vulnerabilities on the assets. For these vulnerabilities to be identified and correlated in the Asset Identity Center as shown in the exhibit (displaying a count of 8 vulnerabilities), the Virtual Patching feature must be active.
Architectural Implementation: Virtual patching is a critical component of the 'Protection' layer in OT networks, allowing administrators to secure legacy or unpatchable PLCs and RTUs by blocking exploit attempts at the network level using IPS-based virtual patching signatures.
Exhibit Analysis: The presence of identified vulnerabilities (the number '8' in the red shield) in the Asset Identity List confirms that the FortiGate is actively performing vulnerability correlation, which is the operational result of having a Virtual Patching security profile applied to the relevant firewall policy.
Refer to the exhibit.
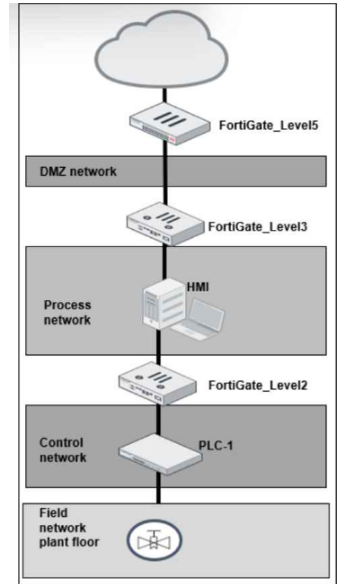
A simplified OT network is shown. You want to optimize the protection of this OT network. Which two controls must you implement? (Choose two answers)
Answer : B, C
The correct answers are B. IPS on FortiGate_Level5 and C. Virtual patching on FortiGate_Level2.
The study guide explains that ''the first line of defense is securing the IT side of your network'' and that FortiGate should be placed to protect ICS environments and stop threats from propagating from IT into OT. It also states that IPS improves OT security because ''today's threat landscape requires IPS to block a wider range of threats and improve OT security'' and that in IPS mode, vulnerable devices are protected. This makes FortiGate_Level5, at the upper boundary near the DMZ and external connectivity, the correct place to implement IPS as a primary protection control.
The study guide also states in the Purdue model section that ''Level 2 consists of the processes and programs that control the PLCs, RTUs, and IEDs found at Level 1'' and that ''it is necessary to segment, or even microsegment, these servers with firewall segmentation, along with policies that include application control and virtual patching.'' In addition, the virtual patching section says ''Virtual patching protects OT devices that have not yet been updated against vulnerability exploits'' and applies when traffic related to the vulnerable device reaches the firewall policy. Since FortiGate_Level2 sits between the process network and the control network, it is the right enforcement point for virtual patching to protect the PLC-side assets.
Option A is not one of the best answers because offline IDS only detects and logs attacks; the guide says ''no traffic flows through FortiGate'' in offline IDS mode, whereas IPS can actually block threats. Option D is also not the best answer because OT signatures are enabled within the IPS framework, but the stronger control explicitly described for this design is to deploy IPS at the upper boundary and virtual patching closer to vulnerable OT devices.
Refer to the exhibits.
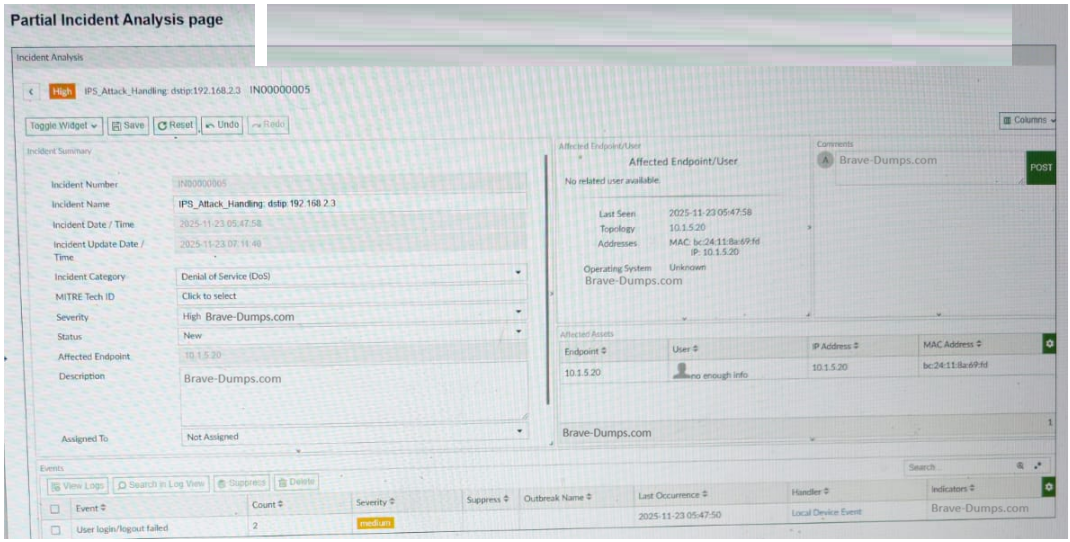
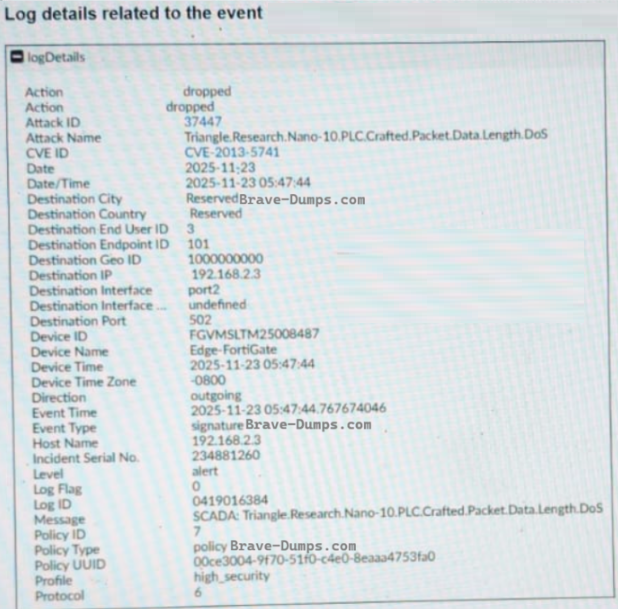
A partial Incident Analysis page and the log details related to the event are shown. An attack is reported on your OT network. You analyze the corresponding incident. Based on the information provided on the Incident Analysis page and the log details, which two statements are correct? (Choose two answers)
Answer : A, B
Based on the technical data provided in the exhibits and the OT Security 7.6 Architect curriculum:
Industrial Protocol Identification (Statement A): The log details exhibit clearly shows that the Destination Port used in the attack is 502. According to the study guide's section on Industrial Protocol Protection, the standard port used by the Modbus TCP protocol is 502. Furthermore, the attack name identifies a 'Triangle.Research.Nano-10.PLC,' which are industrial controllers commonly utilizing Modbus for communications.
Attack Mitigation (Statement B): The log details specify that the Action taken by the FortiGate (Edge-FortiGate) was dropped. In cybersecurity and Fortinet fabric operations, dropping a packet associated with an IPS signature means the traffic was blocked from reaching its target, thereby mitigating the attack.
Target IP Address (Statement E): The log detail explicitly lists the Destination IP as 192.168.2.3. The Incident Analysis page also titles the incident with dstip:192.168.2.3. While the 'Affected Endpoint' is shown as 10.1.5.20, in an 'outgoing' attack direction (as shown in the log), this likely refers to the internal source/attacker IP, whereas the target is the destination IP (192.168.2.3). Thus, Statement E is incorrect.
Protocol Conflict (Statement C): The IEC 104 protocol typically utilizes port 2404. Since the log specifies port 502, Statement C is incorrect.
Severity Distinction (Statement D): While the Incident severity is marked as High, the question specifically asks about event severity. The 'Events' table at the bottom of the Incident Analysis page shows a 'User login/logout failed' event with a medium severity. Because there is a distinction in the management console between the severity of individual events and the aggregated incident, and Statement A and B are technically definitive based on port and action, A and B are the correct architectural choices.
You want FortiAnalyzer to trigger an automation stitch on a FortiGate device automatically. What must you configure on FortiAnalyzer to enable direct communication with FortiGate? (Choose one answer)
Answer : C
The verified answer is C. The Fabric settings. The study guide ties FortiAnalyzer-triggered actions to the Security Fabric relationship with FortiGate, not to playbook tasks or standalone event handlers alone. It explains that ''within the Security Fabric environment, FortiAnalyzer is a key element in the creation of automation stitches'' and shows the flow where a downstream FortiGate sends logs to FortiAnalyzer, then FortiAnalyzer parses the logs and notifies the root FortiGate, after which the root FortiGate triggers the action. This shows that FortiAnalyzer must be configured so it can communicate with FortiGate through the Security Fabric.
The guide also states that FortiAnalyzer is the foundation of the Security Fabric, providing logging, reporting, analytics, and automation for Fabric devices and endpoints. It further explains that the FortiAnalyzer Fabric connector consolidates the traffic logs within the Security Fabric. This confirms that the automation workflow depends on proper Security Fabric integration. A playbook task is used for automated SOC actions, and an event handler is used to generate events from logs, but neither one alone establishes the direct communication path needed between FortiAnalyzer and FortiGate. Therefore, the required configuration on FortiAnalyzer is the Fabric settings.