Fortinet NSE 7 - Advanced Analytics 6.3 NSE7_ADA-6.3 Exam Questions
In the event of a WAN link failure between the collector and the supervisor, by default, what is the maximum number of event files stored on the collector?
On which disk are the SQLite databases that are used for the baselining stored?
Answer : D
The SQLite databases that are used for the baselining are stored on Disk3 of the FortiSIEM server. Disk3 is also used for storing raw event data and CMDB data.
Which three statements about collector communication with the FortiSIEM cluster are true? (Choose three.)
Answer : B, C, E
The statements about collector communication with the FortiSIEM cluster that are true are:
Collectors communicate periodically with the supervisor node. Collectors send heartbeat messages to the supervisor every 30 seconds to report their status and configuration.
The supervisor periodically checks the health of the collector. The supervisor monitors the heartbeat messages from collectors and alerts if there is any issue with their connectivity or performance.
Collectors upload event data to any node in the worker upload list, but report their health directly to the supervisor node. Collectors use a round-robin algorithm to distribute event data among worker nodes in the worker upload list, which is provided by the supervisor during registration. However, collectors only report their health and status to the supervisor node.
What is Tactic in the MITRE ATT&CK framework?
Answer : B
Tactic is what an attacker hopes to achieve in the MITRE ATT&CK framework. Tactic is a high-level category of adversary behavior that describes their objective or goal. For example, some tactics are Initial Access, Persistence, Lateral Movement, Exfiltration, etc. Each tactic consists of one or more techniques that describe how an attacker can accomplish that tactic.
Refer to the exhibit.
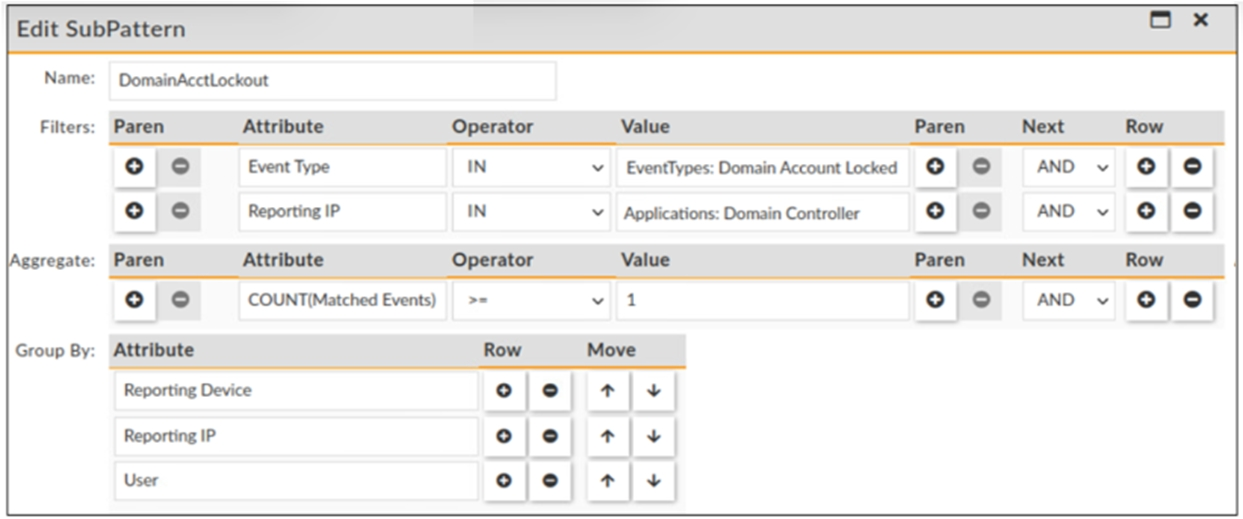
Which statement about the rule filters events shown in the exhibit is true?
Answer : B
The rule filters events with an event type that belong to the Domain Account Locked CMDB group and a reporting IP that belong to the Domain Controller applications group. This means that only events that have both criteria met will be processed by this rule. The event type and reporting IP are joined by an AND operator, which requires both conditions to be true.
Refer to the exhibit.
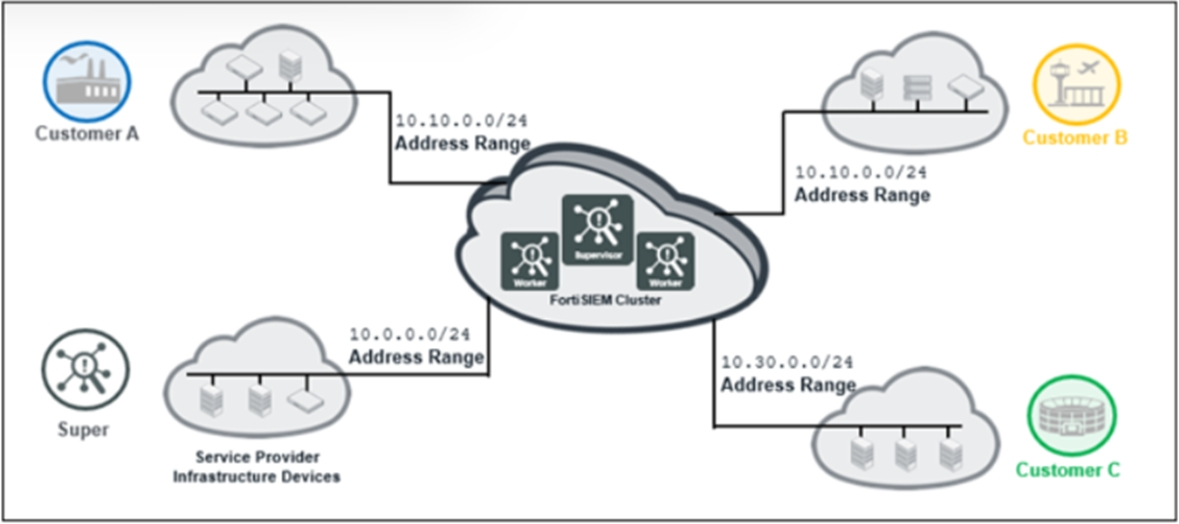
The service provider deployed FortiSIEM without a collector and added three customers on the supervisor.
What mistake did the administrator make?
Answer : A
The mistake that the administrator made is that customer A and customer B have overlapping IP addresses. This will cause confusion and errors in event collection and correlation, as well as CMDB discovery and classification. To avoid this problem, each customer should have a unique IP address range or use NAT to translate their IP addresses.
Refer to the exhibit. Click on the calculator button.
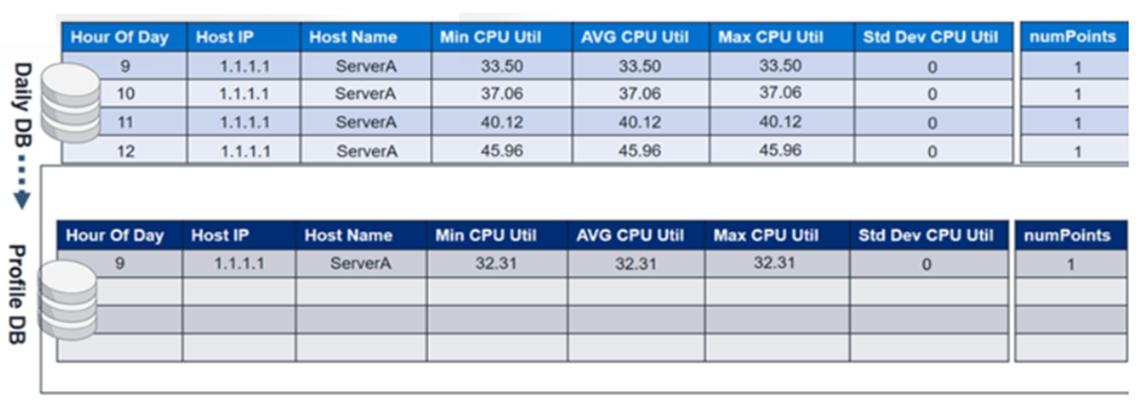
The profile database contains CPU utilization values from day one. At midnight on the second day, the CPU utilization values from the daily database will be merged with the profile database.
In the profile database, in the Hour of Day column where 9 is the value, what will be the updated minimum, maximum, and average CPU utilization values?
Answer : B
The profile database contains CPU utilization values from day one. At midnight on the second day, the CPU utilization values from the daily database will be merged with the profile database using a weighted average formula:
New value = (Old value x Old weight) + (New value x New weight) / (Old weight + New weight)
The weight is determined by the number of days in each database. In this case, the profile database has one day of data and the daily database has one day of data, so the weight is equal for both databases. Therefore, the formula simplifies to:
New value = (Old value + New value) / 2
In the profile database, in the Hour of Day column where 9 is the value, the updated minimum, maximum, and average CPU utilization values are:
Min CPU Util = (32.31 + 32.31) / 2 = 32.31 Max CPU Util = (33.50 + 33.50) / 2 = 33.50 AVG CPU Util = (32.67 + 32.67) / 2 = 32.67