Fortinet NSE 7 - Enterprise Firewall 7.2 NSE7_EFW-7.2 Exam Questions
Which two statements about IKE version 2 fragmentation are true? (Choose two.)
Answer : A, D
In IKE version 2, not all packets are fragmentable. Only certain messages within the IKE negotiation process can be fragmented. Additionally, there is a limit to the number of fragments that IKE version 2 can handle, which is 128. This is specified in the Fortinet documentation and ensures that the IKE negotiation process can proceed even in networks that have issues with large packets. The reassembly timeout and the layer at which fragmentation occurs are not specified in this context within Fortinet documentation.
Which statement is true regarding the Bidirectional Forwarding Detection protocol in BGP?
Answer : C
Which two statements about metadata variables are true? (Choose two.)
Answer : C, D
Metadata variables in FortiGate are created to store metadata associated with different FortiGate features. These variables can be used in various configurations and scripts to dynamically replace the variable with its actual value during processing. A: You create metadata variables on FortiGate. They are used to store metadata for FortiGate features and can be called upon in different configurations. D: They can be used as variables in scripts. Metadata variables are utilized within the scripts to dynamically insert values as per the context when the script runs.
Fortinet FortiOS Handbook: CLI Reference
Which FortiGate in a Security I auric sends togs to FortiAnalyzer?
Answer : B
Option B is correct because each FortiGate in the Security Fabric can send logs to FortiAnalyzer for centralized logging and analysis12. This allows you to monitor and manage the entire Security Fabric from a single console and view aggregated reports and dashboards.
Option A is incorrect because the root FortiGate is not the only device that can send logs to FortiAnalyzer.The root FortiGate is the device that initiates the Security Fabric and acts as the central point of contact for other FortiGate devices3. However, it does not have to be the only log source for FortiAnalyzer.
Option C is incorrect because the FortiGate devices performing NAT or UTM are not the only devices that can send logs to FortiAnalyzer.These devices can perform additional security functions on the traffic that passes through them, such as firewall, antivirus, web filtering, etc4. However, they are not the only devices that generate logs in the Security Fabric.
Option D is incorrect because the last FortiGate that handled a session in the Security Fabric is not the only device that can send logs to FortiAnalyzer.The last FortiGate is the device that terminates the session and applies the final security policy5. However, it does not have to be the only device that reports the session information to FortiAnalyzer.Reference: =
1: Security Fabric - Fortinet Documentation1
2: FortiAnalyzer Demo6
3: Security Fabric topology
4: Security Fabric UTM features
5: Security Fabric session handling
Exhibit.
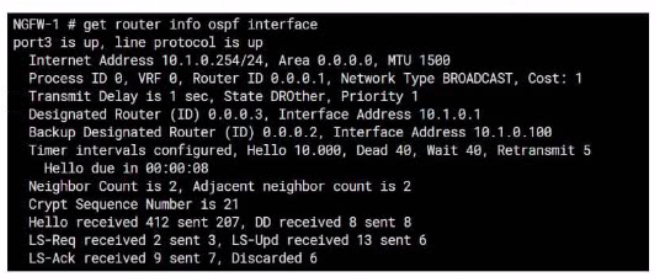
Refer to the exhibit, which shows information about an OSPF interlace
What two conclusions can you draw from this command output? (Choose two.)
Answer : A, C
From the OSPF interface command output, we can conclude that the port3 network has more than one OSPF router because the Neighbor Count is 2, indicating the presence of another OSPF router besides NGFW-1. Additionally, we can deduce that the interfaces of the OSPF routers match the MTU value configured as 1500, which is necessary for OSPF neighbors to form adjacencies. The MTU mismatch would prevent OSPF from forming a neighbor relationship.
Fortinet FortiOS Handbook: OSPF Configuration
An administrator configured the following command on FortiGate
config router ospf
sec reszart-mode graceful-restart
Which two statements correctly describe the result of the above command? (Choose two.)
Answer : B, C
Exhibit.
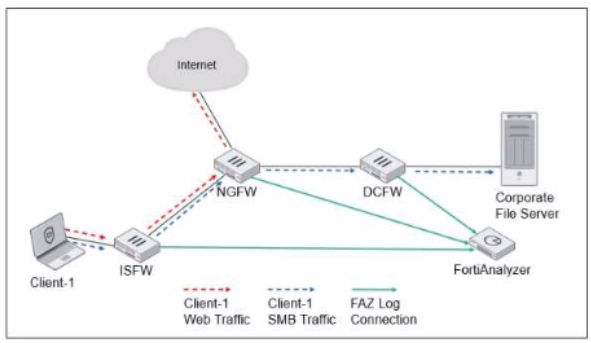
ISFW is installed in the access layer NGFW is performing SNAT and web tittering DCFW is running IPS Which two statements are true regarding the Security Fabric logging? (Choose two.)
Answer : A, B