Fortinet NSE 7 - OT Security 7.2 NSE7_OTS-7.2 Exam Questions
Which two statements are true when you deploy FortiGate as an offline IDS? (Choose two.)
Answer : B, C
Refer to the exhibit.
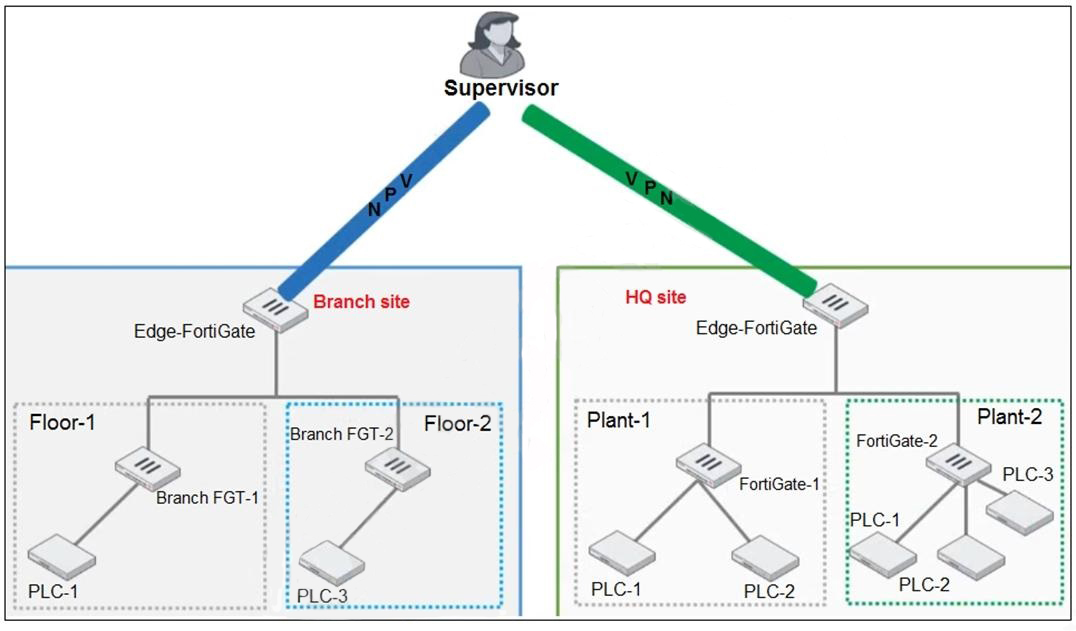
You need to configure VPN user access for supervisors at the breach and HQ sites using the same soft FortiToken. Each site has a FortiGate VPN gateway.
What must you do to achieve this objective?
Answer : A
Which two frameworks are common to secure ICS industrial processes, including SCADA and DCS? (Choose two.)
Answer : B, C
B . NIST Cybersecurity Framework (CSF)
Role: Provides a risk-based approach to manage cybersecurity for critical infrastructure (including ICS/SCADA/DCS).
Fortinet Reference:
Fortinet OT Security Solution Guide (v7.2): 'The NIST Cybersecurity Framework is widely adopted in OT environments to align security practices with business objectives, manage risks, and ensure resilience.' Page 12: 'Framework adoption (e.g., NIST CSF) helps organizations prioritize OT asset protection.'
C . IEC 62443
Role: International standardspecifically designedfor ICS/OT security, covering technical controls, processes, and risk management.
Fortinet Reference:
*Fortinet NSE 7 - OT Security 7.2 Study Guide*: 'IEC 62443 is the foundational standard for securing industrial automation and control systems (IACS), including SCADA and DCS. It defines security zones, conduits, and security levels (SLT).' *Module 4: 'IEC 62443 provides OT-specific security requirements not covered by IT frameworks.'*
Why Other Options Are Incorrect
A . Modbus: Acommunication protocol(not a framework) used in OT environments. It lacks security features and governance.
FortiGate OT Security Guide: 'Modbus is an unauthenticated, cleartext protocol vulnerable to eavesdropping. It is not a security framework.'
You are investigating a series of incidents that occurred in the OT network over past 24 hours in FortiSIEM.
Which three FortiSIEM options can you use to investigate these incidents? (Choose three.)
Answer : C, D, E
What is the primary objective of implementing SD-WAN in operational technology (OT) networks'?
Answer : C
In a wireless network integration, how does FortiNAC obtain connecting MAC address information?
Answer : A
FortiNAC can integrate with RADIUS servers to obtain MAC address information for wireless clients that authenticate through the RADIUS server.
Fortinet NSE 7 - OT Security 6.4 Study Guide, Chapter 4: OT Security Devices, page 4-28.
An OT supervisor has configured LDAP and FSSO for the authentication. The goal is that all the users be authenticated against passive authentication first and, if passive authentication is not successful, then users should be challenged with active authentication.
What should the OT supervisor do to achieve this on FortiGate?
Answer : C
The OT supervisor should configure a firewall policy with FSSO users and place it on the top of list of firewall policies in order to achieve the goal of authenticating users against passive authentication first and, if passive authentication is not successful, then challenging them with active authentication.