Fortinet NSE 7 - Public Cloud Security 7.2 NSE7_PBC-7.2 Exam Questions
You need a solution to safeguard public cloud-hosted web applications from the OWASP Top 10 vulnerabilities. The solution must support the same region in which your applications reside, with minimum traffic cost
Which solution meets the requirements?
Answer : C
The correct answer is C. Use FortiWebCloud.
The other options are incorrect because:
Refer to the exhibit
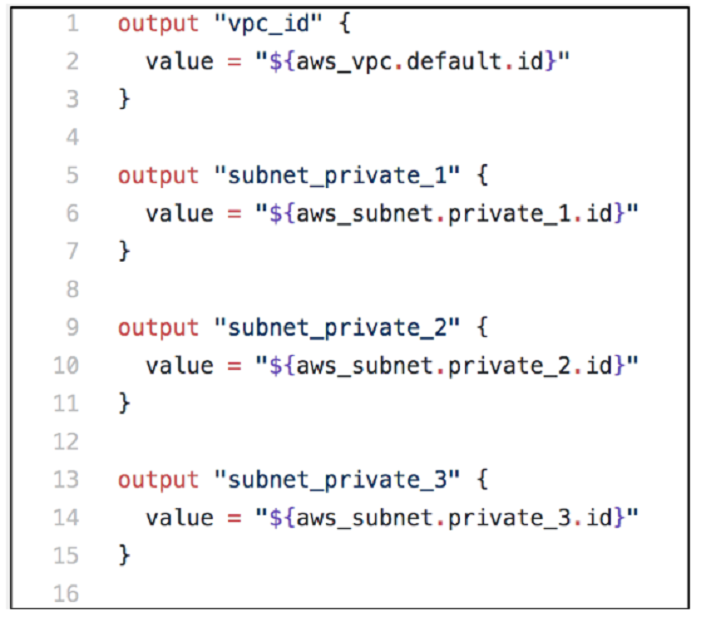
You are tasked with deploying a webserver and FortiGate VMS in AWS_ You are using Terraform to automate the process
Which two important details should you know about the Terraform files? (Choose two.)
Answer : A, B
The other options are incorrect because:
After the deployment, Terraform output values are not visible only through AWS CloudShell. You can access them from any shell or terminal where you have Terraform installed and configured with your AWS credentials.
Output Values - Configuration Language | Terraform - HashiCorp Developer
Command: output - Terraform by HashiCorp
Input Variables - Configuration Language | Terraform - HashiCorp Developer
Configuration Language | Terraform - HashiCorp Developer
You are tasked with deploying a FortiGate HA solution in Amazon Web Services (AWS) using Terraform What are two steps you must take to complete this deployment? (Choose two.)
Answer : B, C
To deploy a FortiGate HA solution in AWS using Terraform, you need to create an AWS IAM user with permissions to access the AWS resources and services required by the FortiGate-VM. You also need to use CloudShell to install Terraform, which is a tool for building, changing, and versioning infrastructure as code.
Deploying FortiGate-VM using Terraform | AWS Administration Guide
Setting up IAM roles | AWS Administration Guide
Launching the instance using roles and user data | AWS Administration Guide
Terraform by HashiCorp
Which two Amazon Web Services (AWS) features support east-west traffic inspection within the AWS cloud by the FortiGate VM? (Choose two.)
Answer : B, D
The correct answer is B and D. A transit gateway with an attachment and a transit VPC support east-west traffic inspection within the AWS cloud by the FortiGate VM.
The other options are incorrect because:
You are adding more spoke VPCs to an existing hub and spoke topology Your goal is to finish this task in the minimum amount of time without making errors.
Which Amazon AWS services must you subscribe to accomplish your goal?
Answer : D
The correct answer is D. CloudWatch and S3.
CloudWatch: A monitoring and observability service that collects and processes events from various AWS resources, including Transit Gateway attachments and route tables.
S3: A scalable object storage service that can store the configuration files and logs generated by the Lambda function.
The other AWS services mentioned in the options are not required for this task. GuardDuty is a threat detection service that monitors for malicious and unauthorized behavior to help protect AWS accounts and workloads. WAF is a web application firewall that helps protect web applications from common web exploits. Inspector is a security assessment service that helps improve the security and compliance of applications deployed on AWS. DynamoDB is a fast and flexible NoSQL database service that can store various types of data.
1: GitHub - fortinet/aws-lambda-tgw
An administrator is looking for a solution that can provide insight into users and data stored in major SaaS applications in the multicloud environment Which product should the administrator deploy to have secure access to SaaS applications?
Answer : C
For administrators seeking to gain insights into user activities and data within major SaaS applications across multicloud environments, deploying FortiCASB (Cloud Access Security Broker) is the most effective solution (Option C).
Role of FortiCASB: FortiCASB is specifically designed to provide security visibility, compliance, data security, and threat protection for cloud-based services. It acts as a mediator between users and cloud service providers, offering deep visibility into the operations and data handled by SaaS applications.
Capabilities of FortiCASB: This product enables administrators to monitor and control the access and usage of SaaS applications. It helps in assessing security configurations, tracking user activities, and evaluating data movement across the cloud services. By doing so, it assists organizations in enforcing security policies, detecting anomalous behaviors, and ensuring compliance with regulatory standards.
Integration and Functionality: FortiCASB integrates seamlessly with major SaaS platforms, providing a centralized management interface that allows for comprehensive analysis and real-time protection measures. This integration ensures that organizations can maintain control over their data across various cloud services, enhancing the overall security posture in a multicloud environment.
Refer to the exhibit
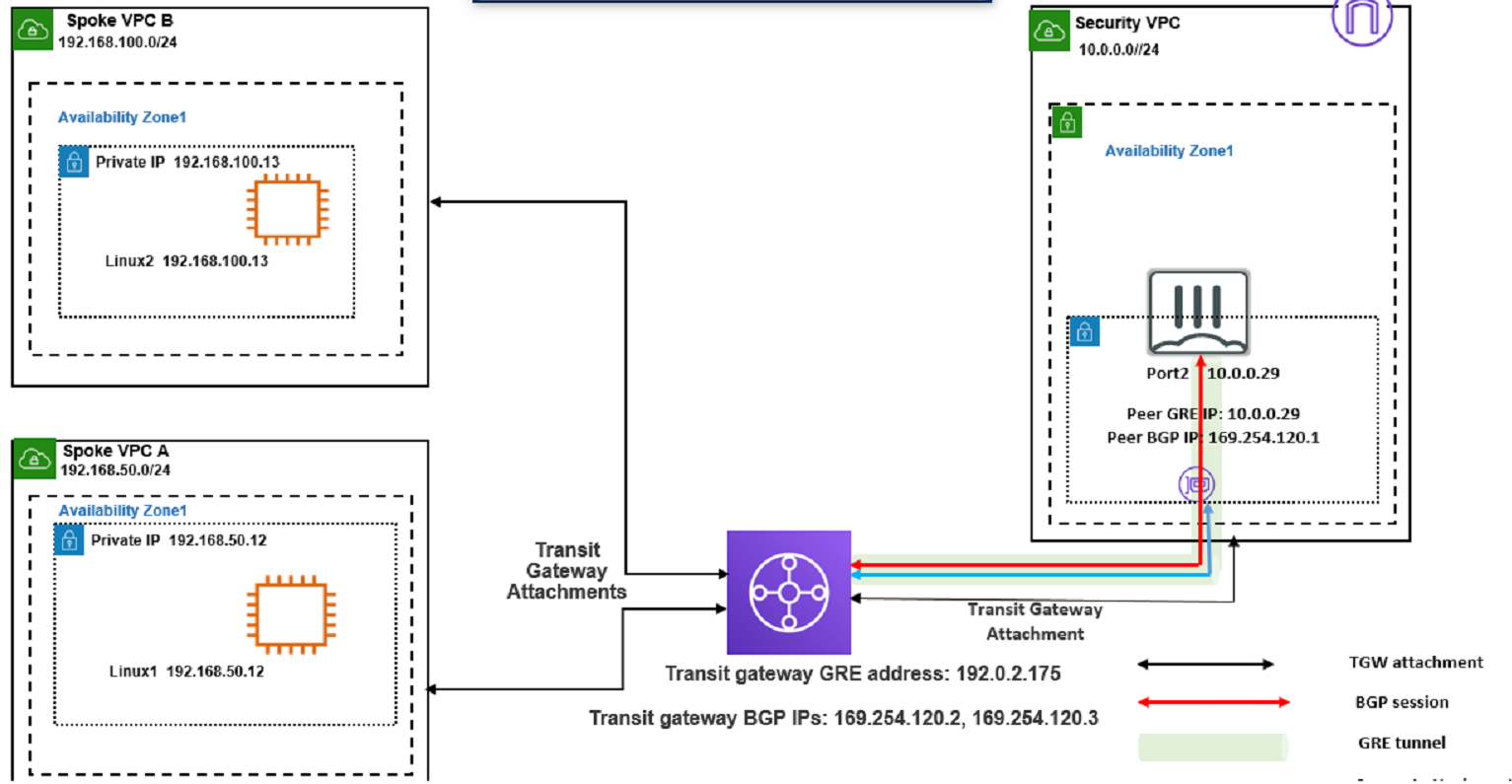
You attempted to access the Linux1 EC2 instance directly from the internet using its public IP address in AWS.
However, your connection is not successful.
Given the network topology, what can be the issue?
Answer : D
This is because the Linux1 EC2 instance is not accessible directly from the internet using its public IP address in AWS.
An internet gateway is a horizontally scaled, redundant, and highly available VPC component that allows communication between instances in your VPC and the internet. Without an internet gateway, the Linux1 EC2 instance cannot receive or send traffic to or from the internet, even if it has a public IP address assigned to it.
To fix this issue, you need to attach an internet gateway to the Spoke VPC A and configure a route table that directs internet-bound traffic to the internet gateway. You also need to ensure that the Linux1 EC2 instance has a security group that allows inbound and outbound traffic on the desired ports.
: [Internet Gateways - Amazon Virtual Private Cloud] : [Attach an Internet Gateway to Your VPC - Amazon Virtual Private Cloud] : [Security Groups for Your VPC - Amazon Virtual Private Cloud]