Fortinet NSE 7 - FortiSASE 25 Enterprise Administrator NSE7_SSE_AD-25 Exam Questions
Refer to the exhibits.
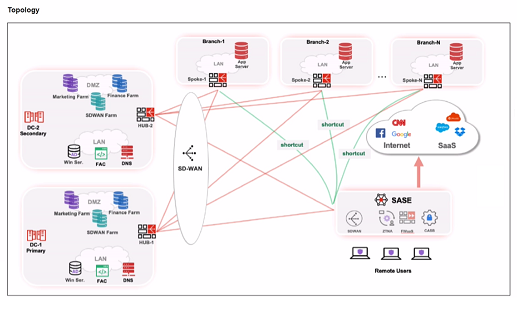

When remote users connected to FortiSASE require access to internal resources on Branch-2. how will traffic be routed?
Answer : C
When remote users connected to FortiSASE require access to internal resources on Branch-2, the following process occurs:
SD-WAN Capability:
FortiSASE leverages SD-WAN to optimize traffic routing based on performance metrics and priorities.
In the priority settings, HUB-1 is configured with the highest priority (P1), whereas HUB-2 has a lower priority (P2).
Traffic Routing Decision:
FortiSASE evaluates the available hubs (HUB-1 and HUB-2) and selects HUB-1 due to its highest priority setting.
Once the traffic reaches HUB-1, it is then routed to the appropriate branch based on internal routing policies.
Branch-2 Access:
Since HUB-1 has the highest priority, FortiSASE directs the traffic to HUB-1.
HUB-1 then routes the traffic to Branch-2, providing the remote users access to the internal resources.
FortiOS 7.6 Administration Guide: Details on SD-WAN configurations and priority settings.
FortiSASE 23.2 Documentation: Explains how FortiSASE integrates with SD-WAN to route traffic based on defined priorities and performance metrics.
A Fortinet customer is considering integrating FortiManager with FortiSASE. What are two prerequisites they should consider? (Choose two answers)
Answer : B, D
Integrating FortiManager with FortiSASE allows for central management of configuration objects like addresses and5 security 6profiles. For this integration to function correctly, the following key prerequisites must be met:
Same FortiCloud Account: A fundamental requirement for the integration is that both 10the FortiSASE instance and the FortiManager (whether physical, VM, or Cloud) must be registered under the same FortiCloud (FortiCare) account. This common identity allows the platforms to securely discover and authorize each other for synchronization.
Supported Firmware Version: The FortiManager must run a firmware version that is compatible with the FortiSASE release. According to the FortiSASE 25 Enterprise Administrator Study Guide, FortiManager version 7.4.4 or later is generally required to support the specific API connectors and object synchronization logic used by current FortiSASE environments. Using an unsupported version may result in synchronization failures or missing configuration features.
Management Logic: Once these prerequisites are met, the administrator can enable 'Central Management' in the FortiSASE portal. This creates a one-way synchronization where FortiManager acts as the source of truth for objects like Security Profile Groups, ensuring consistent security posture across both the SASE cloud and on-premises FortiGates.
Which statement about FortiSASE and SAML is true? (Choose one answer)
Answer : A
FortiSASE utilizes Security Assertion Markup Language (SAML) to provide a seamless Single Sign-On (SSO) experience for remote users connecting to the cloud infrastructure.
Role Identification: In a SAML exchange, FortiSASE functions as the Service Provider (SP). It relies on an external Identity Provider (IdP)---such as Microsoft Entra ID (formerly Azure AD), Okta, or FortiAuthenticator---to authenticate the user's identity and provide security assertions.2
SAML Group Matching: One of the core features of the FortiSASE SAML implementation is the ability to perform group matching. During the authentication process, the IdP sends a SAML assertion that typically includes an 'Attribute Statement' containing the user's group memberships.3 FortiSASE captures this attribute and matches it against locally defined SAML user groups.
Policy Enforcement: This group matching capability is critical because it allows administrators to apply different Security Internet Access (SIA) or Secure Private Access (SPA) policies based on the user's role (e.g., 'Marketing' vs. 'Finance') rather than managing individual users manually.
Analysis of Incorrect Options: * Options C and D are incorrect because FortiSASE does not natively act as a SAML IdP; it is designed to consume assertions from professional identity management platforms.
Option B is incorrect because FortiSASE fully supports and relies upon group matching for enterprise-scale policy management.
What are two advantages of using zero-trust tags? (Choose two.)
Answer : A, B
Zero-trust tags are critical in implementing zero-trust network access (ZTNA) policies. Here are the two key advantages of using zero-trust tags:
Access Control (Allow or Deny):
Zero-trust tags can be used to define policies that either allow or deny access to specific network resources based on the tag associated with the user or device.
This granular control ensures that only authorized users or devices with the appropriate tags can access sensitive resources, thereby enhancing security.
Determining Security Posture:
Zero-trust tags can be utilized to assess and determine the security posture of an endpoint.
Based on the assigned tags, FortiSASE can evaluate the device's compliance with security policies, such as antivirus status, patch levels, and configuration settings.
Devices that do not meet the required security posture can be restricted from accessing the network or given limited access.
FortiOS 7.6 Administration Guide: Provides detailed information on configuring and using zero-trust tags for access control and security posture assessment.
FortiSASE 23.2 Documentation: Explains how zero-trust tags are implemented and used within the FortiSASE environment for enhancing security and compliance.
What is the maximum number of Secure Private Access (SPA) service connections (SPA hubs) supported in the SPA use case? (Choose one answer)
Answer : B
In recent versions of FortiSASE (starting from version 24.4 and later), the platform has increased its scalability to support larger enterprise environments.
Maximum Hub Support: According to the FortiSASE Mature Administration Guide and the FortiSASE 25.3.148 Feature Release Notes, administrators can now configure a maximum of 12 SPA Service Connections (SPA hubs). Previously, this limit was restricted to 4 hubs.
Scalability for Large Enterprises: This enhancement allows organizations with complex, geographically dispersed networks---such as those with multiple regional datacenters or cloud hubs---to integrate up to 12 distinct FortiGate SD-WAN hubs into their SASE infrastructure.
Service Connection Licensing: Each SPA hub requires a dedicated FortiGate SPA Service Connection license. In MSSP environments using FortiCloud Organizations, a single FortiSASE instance can inherit these licenses from a root OU, supporting up to the same cumulative maximum of 12 service connections.
Routing and Performance: These 12 hubs form the 'Private Access' backbone, where FortiSASE security PoPs act as spokes. The use of BGP (either per-overlay or on loopback) ensures that traffic is dynamically routed to the optimal hub based on the destination network and defined SLA priorities.
What are the key differences between the FortiSASE BGP per overlay and BGP on loopback routing design methods? (Choose one answer)
Answer : A
FortiSASE supports two main routing design methods for Secure Private Access (SPA) when connecting to a FortiGate SD-WAN hub:
BGP per Overlay (Traditional/Default Method): In this configuration, a separate iBGP session is established over every individual IPsec overlay (tunnel) between the FortiSASE PoP and the hub. These sessions terminate on the tunnel interface IP addresses. To facilitate this, the hubs typically use the IPsec VPN mode-cfg feature to dynamically assign tunnel IP addresses to the SASE PoPs. For every LAN prefix, the system generates multiple BGP routes---one for each overlay---which increases the total number of routes advertised across the network.
BGP on Loopback (Modern Alternative): This newer design establishes only a single iBGP session between the spoke and the hub, regardless of how many physical or logical overlays (tunnels) connect them. The session is terminated on a loopback interface on both sides.
Key Advantages of BGP on Loopback:
Reduced Complexity: It significantly simplifies the BGP configuration because there are fewer neighbors to manage.2
Improved Scalability: It greatly reduces the volume of routes advertised, as only a single BGP route is generated for each LAN prefix, making it the preferred choice for large-scale deployments.
Resiliency: The BGP session remains active as long as the loopback is reachable via any of the available overlays, meaning no BGP convergence is required if a single overlay fails.
Refer to the exhibits.
WiMO-Pro and Win7-Pro are endpoints from the same remote location. WiMO-Pro can access the internet though FortiSASE, while Wm7-Pro can no longer access the internet
Given the exhibits, which reason explains the outage on Wm7-Pro?
Answer : D
Based on the provided exhibits, the reason why the Win7-Pro endpoint can no longer access the internet through FortiSASE is due to exceeding the total vulnerability detected threshold. This threshold is used to determine if a device is compliant with the security requirements to access the network.
Endpoint Compliance:
FortiSASE monitors endpoint compliance by assessing various security parameters, including the number of vulnerabilities detected on the device.
The compliance status is indicated by the ZTNA tags and the vulnerabilities detected.
Vulnerability Threshold:
The exhibit shows that Win7-Pro has 176 vulnerabilities detected, whereas Win10-Pro has 140 vulnerabilities.
If the endpoint exceeds a predefined vulnerability threshold, it may be restricted from accessing the network to ensure overall network security.
Impact on Network Access:
Since Win7-Pro has exceeded the vulnerability threshold, it is marked as non-compliant and subsequently loses internet access through FortiSASE.
The FortiSASE endpoint profile enforces this compliance check to prevent potentially vulnerable devices from accessing the internet.
FortiOS 7.6 Administration Guide: Provides information on endpoint compliance and vulnerability management.
FortiSASE 23.2 Documentation: Explains how vulnerability thresholds are used to determine endpoint compliance and access control.