Fortinet NSE 7 - Zero Trust Access 7.2 NSE7_ZTA-7.2 Exam Questions
Exhibit.
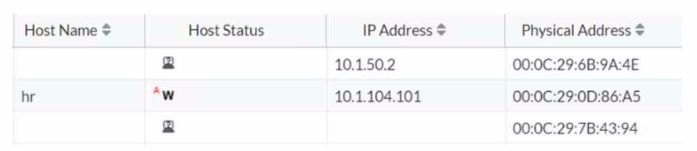
Which statement is true about the hr endpoint?
Answer : D
Based on the exhibit showing the status of the hr endpoint, the true statement about this endpoint is:
D) The endpoint has been marked at risk: The 'w' next to the host status for the 'hr' endpoint typically denotes a warning, indicating that the system has marked it as at risk due to some security policy violations or other concerns that need to be addressed.
The other options do not align with
the provided symbol 'w' in the context of FortiNAC:
A) The endpoint is a rogue device: If the endpoint were rogue, we might expect a different symbol, often indicating a critical status or alarm.
B) The endpoint is disabled: A disabled status is typically indicated by a different icon or status indicator.
C) The endpoint is unauthenticated: An unauthenticated status would also be represented by a different symbol or status indication, not a 'w'.
Which three core products are mandatory in the Fortinet ZTNA solution'' {Choose three.)
Answer : A, B, D
Fortinet ZTNA solution is a zero-trust network access approach that provides secure and granular access to applications hosted anywhere, for users working from anywhere. The three core products that are mandatory in the Fortinet ZTNA solution are:
FortiClient EMS: This is the central management console that orchestrates the ZTNA policies and provides visibility and control over the endpoints and devices. It also integrates with FortiAuthenticator for identity verification and FortiAnalyzer for reporting and analytics.
FortiClient: This is the endpoint agent that supports ZTNA, VPN, endpoint protection, and vulnerability scanning. It establishes encrypted tunnels with the ZTNA proxy on the FortiGate and provides device posture and single sign-on (SSO) capabilities.
FortiGate: This is the next-generation firewall that acts as the ZTNA proxy and enforces the ZTNA policies based on user identity, device posture, and application context. It also provides security inspection and threat prevention for the ZTNA traffic.
Which three statements are true about zero-trust telemetry compliance1? (Choose three.)
Answer : A, B, D
In the context of zero-trust telemetry compliance, the three true statements are:
A) FortiClient EMS creates dynamic policies using ZTNA tags: FortiClient EMS utilizes ZTNA (Zero Trust Network Access) tags to create dynamic policies based on the telemetry it receives from endpoints.
B) FortiClient checks the endpoint using the ZTNA tags provided by FortiClient EMS: FortiClient on the endpoint uses the ZTNA tags from FortiClient EMS to determine compliance with the specified security policies.
D) FortiOS provides network access to the endpoint based on the zero-trust tagging rules: FortiOS, the operating system running on FortiGate devices, uses the zero-trust tagging rules to make decisions on network access for endpoints.
The other options are not accurate in this context:
C) ZTNA tags are configured in FortiClient, based on criteria such as certificates and the logged-in domain: ZTNA tags are typically configured and managed in FortiClient EMS, not directly in FortiClient.
E) FortiClient EMS sends the endpoint information received through FortiClient Telemetry to FortiOS: While FortiClient EMS does process telemetry data, the direct sending of endpoint information to FortiOS is not typically described in this manner.
Zero Trust Telemetry in Fortinet Solutions.
FortiClient EMS and FortiOS Integration for ZTNA.
What are two functions of NGFW in a ZTA deployment? (Choose two.)
Answer : A, C
NGFW stands for Next-Generation Firewall, which is a network security device that provides advanced features beyond the traditional firewall, such as application awareness, identity awareness, threat prevention, and integration with other security tools. ZTA stands for Zero Trust Architecture, which is a security model that requires strict verification of the identity and context of every request before granting access to network resources. ZTA assumes that no device or user can be trusted by default, even if they are connected to a corporate network or have been previously verified.
In a ZTA deployment, NGFW can perform two functions:
Acts as segmentation gateway: NGFW can act as a segmentation gateway, which is a device that separates different segments of the network based on security policies and rules. Segmentation can help isolate and protect sensitive data and applications from unauthorized or malicious access, as well as reduce the attack surface and contain the impact of a breach. NGFW can enforce granular segmentation policies based on the identity and context of the devices and users, as well as the applications and services they are accessing. NGFW can also integrate with other segmentation tools, such as software-defined networking (SDN) and microsegmentation, to provide a consistent and dynamic segmentation across the network.
Device discovery and profiling: NGFW can also perform device discovery and profiling, which are processes that identify and classify the devices that are connected to the network, as well as their attributes and behaviors. Device discovery and profiling can help NGFW to apply the appropriate security policies and rules based on the device type, role, location, health, and activity. Device discovery and profiling can also help NGFW to detect and respond to anomalous or malicious devices that may pose a threat to the network.
: What is a Next-Generation Firewall (NGFW)? | Fortinet : What is Zero Trust Network Access (ZTNA)? | Fortinet :Zero Trust Architecture Explained: A Step-by-Step Approach:The Most Common NGFW Deployment Scenarios:Sample Configuration for Post vWAN Deployment
Which two statements are true regarding certificate-based authentication for ZTNA deployment? (Choose two.)
Answer : B, D
Certificate-based authentication is a method of verifying the identity of a device or user by using a digital certificate issued by a trusted authority. For ZTNA deployment, certificate-based authentication is used to ensure that only authorized devices and users can access the protected applications or resources.
B) The default action for empty certificates is block. This is true because ZTNA requires both device and user verification before granting access. If a device does not have a valid certificate issued by the ZTNA CA, it will be blocked by the ZTNA gateway. This prevents unauthorized or compromised devices from accessing the network.
D) Client certificate configuration is a mandatory component for ZTNA. This is true because ZTNA relies on client certificates to identify and authenticate devices. Client certificates are generated by the ZTNA CA and contain the device ID, ZTNA tags, and other information. Client certificates are distributed to devices by the ZTNA management server (such as EMS) and are used to establish a secure connection with the ZTNA gateway.
A) FortiGate signs the client certificate submitted by FortiClient. This is false because FortiGate does not sign the client certificates. The client certificates are signed by the ZTNA CA, which is a separate entity from FortiGate. FortiGate only verifies the client certificates and performs certificate actions based on the ZTNA tags.
C) Certificate actions can be configured only on the FortiGate CLI. This is false because certificate actions can be configured on both the FortiGate GUI and CLI. Certificate actions are the actions that FortiGate takes based on the ZTNA tags in the client certificates. For example, FortiGate can allow, block, or redirect traffic based on the ZTNA tags.
1: Technical Tip: ZTNA for Corporate hosts with SAML authentication and FortiAuthenticator as IDP
2: Zero Trust Network Access - Fortinet
Which statement is true regarding a FortiClient quarantine using FortiAnalyzer playbooks?
Answer : C
FortiAnalyzer playbooks are automated workflows that can perform actions based on triggers, conditions, and outputs. One of the actions that a playbook can perform is to quarantine a device by sending an API call to FortiClient EMS, which then instructs the FortiClient agent on the device to disconnect from the network. This can help isolate and contain a compromised or non-compliant device from spreading malware or violating policies.Reference:=
Quarantine a device from FortiAnalyzer playbooks
Playbooks
exhibit.
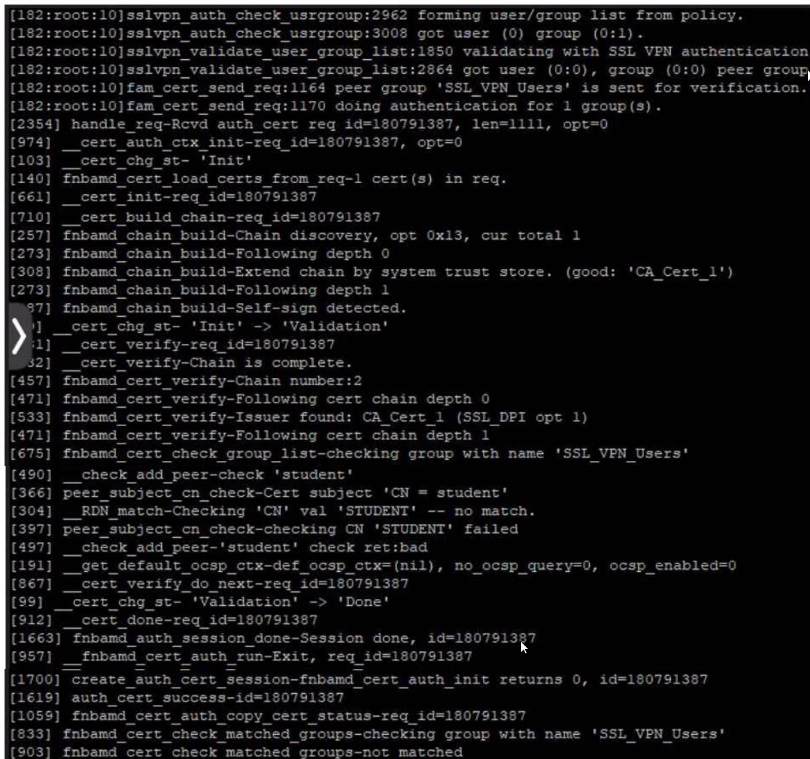
User student is not able to log in to SSL VPN
Given the output showing a real-time debug: which statement describes the login failure?
Answer : C
Given the output showing a real-time debug, the statement that describes the login failure is:
C) student is not part of the usergroup SSL_VPN_Users: The debug log contains a line that says 'fnbam_cert_check_group_list-checking group with name 'SSL_VPN_Users'' followed by 'peer_check_add_peer_check_student' and later 'RDN_match-Checking 'CN' val 'STUDENT' -- no match.' This suggests that the certificate presented has a common name (CN) of 'student', which does not match or is not authorized under the 'SSL_VPN_Users' group expected for successful authentication.