GAQM Certified Professional Ethical Hacker (CPEH) CPEH-001 Exam Questions
You are the CIO for Avantes Finance International, a global finance company based in Geneva. You are responsible for network functions and logical security throughout the entire corporation. Your company has over 250 servers running Windows Server, 5000 workstations running Windows Vista, and 200 mobile users working from laptops on Windows 7. Last week, 10 of your company's laptops were stolen from salesmen while at a conference in Amsterdam. These laptops contained proprietary company information. While doing damage assessment on the possible public relations nightmare this may become, a news story leaks about the stolen laptops and also that sensitive information from those computers was posted to a blog online. What built-in Windows feature could you have implemented to protect the sensitive information on these laptops?
Answer : D
Peter extracts the SIDs list from Windows 2000 Server machine using the hacking tool ''SIDExtractor''. Here is the output of the SIDs:
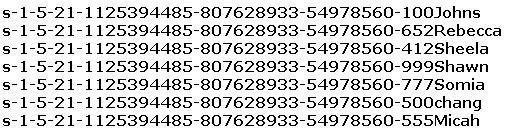
From the above list identify the user account with System Administrator privileges.
Answer : F
The SID of the built-in administrator will always follow this example: S-1-5-domain-500
Which tool/utility can help you extract the application layer data from each TCP connection from a log file into separate files?
Answer : C
Tcpflow is a program that captures data transmitted as part of TCP connections (flows), and stores the data in a way that is convenient for protocol analysis or debugging. A program like 'tcpdump' shows a summary of packets seen on the wire, but usually doesn't store the data that's actually being transmitted. In contrast, tcpflow reconstructs the actual data streams and stores each flow in a separate file for later analysis.
Which of the statements concerning proxy firewalls is correct?
Answer : D
What does a type 3 code 13 represent?(Choose two.
Answer : B, D
Type 3 code 13 is destination unreachable administratively prohibited. This type of message is typically returned from a device blocking a port.
Whichtypes of detection methods are employed by Network Intrusion Detection Systems (NIDS)? (Choose two.)
Answer : A, B
Which of the following represent weak password? (Select 2 answers)
Answer : E, H