HashiCorp Certified: Vault Associate (003) HCVA0-003 Exam Questions
Compared to service tokens, batch tokens are ideal for what type of action?
Answer : D
Comprehensive and Detailed in Depth
Batch tokens are designed for specific, transient use cases. The HashiCorp Vault documentation states: 'Batch tokens are lightweight and scalable and include just enough information to be used with Vault. They are generally used for ephemeral, high-performance workloads, such as encrypting data.' This makes them ideal for short-lived, high-volume, or 'ephemeral' tasks (D).
The docs contrast: 'Unlike service tokens, which are renewable and suited for long-lived processes, batch tokens have a fixed TTL and cannot be renewed.' Options like generating dynamic credentials (A) and daily batch jobs (C) align more with service tokens, while renewing tokens (B) isn't a batch token function. Thus, D is correct.
HashiCorp Vault Documentation - Batch Tokens
True or False? All dynamic secrets in Vault are required to have a lease.
Answer : A
Comprehensive and Detailed in Depth
A: All dynamic secrets (e.g., database creds) have leases for lifecycle management. Correct.
B: Incorrect; leases are mandatory for dynamic secrets.
Overall Explanation from Vault Docs:
''All dynamic secrets in Vault are required to have a lease... forcing consumers to check in routinely.''
Topic 2, Exam Pool B
Use this screenshot to answer the question below:
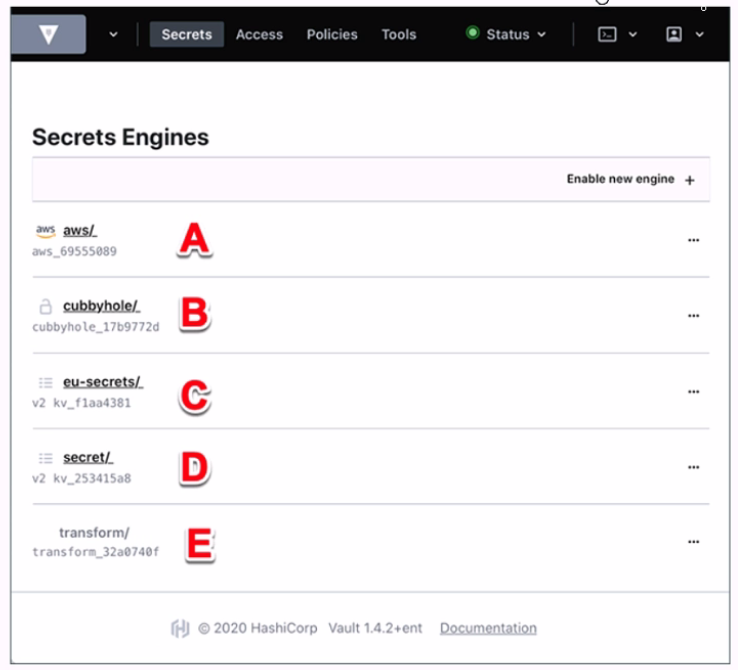
Where on this page would you click to view a secret located at secret/my-secret?
Answer : C
In the HashiCorp Vault UI, secrets are organized in a tree-like structure. To view a secret located at secret/my-secret, you would click on the ''secret/'' folder in the tree, then click on the ''my-secret'' file. In this screenshot, the ''secret/'' folder is located at option C. This folder contains the secrets that are stored in the key/value secrets engine, which is the default secrets engine in Vault. The key/value secrets engine allows you to store arbitrary secrets as key/value pairs. The key is the path of the secret, and the value is the data of the secret. For example, the secret located at secret/my-secret has a key of ''my-secret'' and a value of whatever data you stored there.
[KV - Secrets Engines | Vault | HashiCorp Developer]
From the options below, select the benefits of using a batch token over a service token (select four).
Answer : A, C, E, F
Comprehensive and Detailed in Depth
Batch tokens are lightweight alternatives to service tokens, with trade-offs. Let's analyze:
A: Designed for short-lived, high-performance tasks. Correct.
B: Cannot be root tokens; root status is service-token-specific. Incorrect.
C: Orphan batch tokens work in replication. Correct.
D: No accessors; unique to service tokens. Incorrect.
E: Minimal overhead makes them scalable. Correct.
F: No disk storage reduces cost. Correct.
Overall Explanation from Vault Docs:
''Batch tokens are encrypted blobs... lightweight, scalable, no storage cost, ideal for ephemeral workloads.''
True or False? Although AppRole is designed for machines, humans can use it to authenticate to Vault if you wish.
Answer : A
Comprehensive and Detailed In-Depth
AppRole's flexibility allows human use:
A . True: 'Although AppRole is primarily designed for machine-to-machine authentication, it can also be used by humans to authenticate to Vault if needed.' It uses a role_id and secret_id, which, while less convenient for humans, are technically usable. 'Yeah, absolutely. Although it's not super friendly for us humans to remember the values, you could use it if you wanted to.'
Incorrect Option:
B . False: Incorrect; it's not restricted to machines only.
This adaptability broadens AppRole's applicability.
Which statement best explains how Vault handles data encryption?
Answer : A
Comprehensive and Detailed in Depth
Vault's encryption mechanism is a core security feature. The HashiCorp Vault documentation states: 'When a Vault server is started, it starts in a sealed state. In this state, Vault is configured to know where and how to access the physical storage, but doesn't know how to decrypt any of it. Unsealing is the process of obtaining the plaintext root key necessary to read the decryption key to decrypt the data, allowing access to the Vault.' It further explains: 'Vault uses encryption to secure data at rest and in transit, using an encryption key protected by the root key.'
The documentation details: 'The data stored by Vault is encrypted using an encryption key in the keyring. This keyring is itself encrypted by the root key, which is protected by the unseal process (e.g., Shamir's Secret Sharing or auto-unseal). Vault ensures data is encrypted both at rest in the storage backend and in transit over the network using TLS.' Option B is false---the root key is never stored in plaintext. Option C is incorrect---data is encrypted at rest, not just in transit. Option D is wrong---Vault performs encryption internally, not via third-party services. Thus, A is correct.
HashiCorp Vault Documentation - Seal Concepts
True or False? Once the lease for a dynamic secret has expired, Vault revokes the credentials on the backend platform for which they were created (i.e., database, AWS, Kubernetes).
Answer : A
Comprehensive and Detailed In-Depth
Dynamic secrets are managed actively:
A . True: 'Once the lease for a dynamic secret has expired, Vault automatically revokes the credentials on the backend platform for which they were created.' This cleanup reduces technical debt.
Incorrect Option:
B . False: Incorrect; revocation is automatic.
'When a lease expires, Vault does indeed revoke the credentials on the platform.'