HashiCorp Certified: Vault Associate (002) Vault-Associate Exam Questions
Which of the following describes usage of an identity group?
Answer : D
An identity group is a collection of entities that share some common attributes. An identity group can have one or more policies attached to it, which are inherited by all the members of the group. An identity group can also have subgroups, which can further refine the policies and attributes for a subset of entities.
Which of the following is a machine-oriented Vault authentication backend?
You can build a high availability Vault cluster with any storage backend.
The vault lease renew command increments the lease time from:
You are using the Vault userpass auth method mounted at auth/userpass. How do you create a new user named "sally" with password "h0wN0wB4r0wnC0w"? This new user will need the power-users policy.
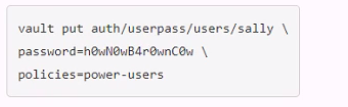
A.
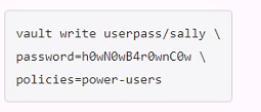
B.
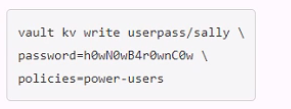
C.
D.
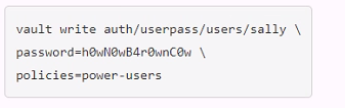
Answer : D
To create a new user named ''sally'' with password ''h0wN0wB4r0wnC0w'' and the power-users policy, you would use the Vault userpass auth method mounted at auth/userpass. You would use the following command: ''vault write auth/userpass/users/sally password=h0wN0wB4r0wnC0w policies=power-users''. This command would create a new user named ''sally'' with the specified password and policy.Reference:
[Userpass Auth Method | Vault | HashiCorp Developer]
[Create Vault policies | Vault | HashiCorp Developer]
A developer mistakenly committed code that contained AWS S3 credentials into a public repository. You have been tasked with revoking the AWS S3 credential that was in the code. This credential was created using Vault's AWS secrets engine and the developer received the following output when requesting a credential from Vault.
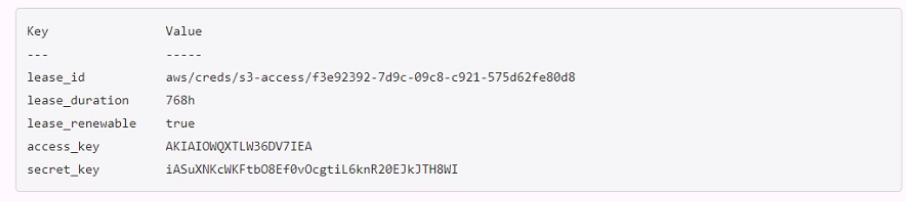
Which Vault command will revoke the lease and remove the credential from AWS?
Answer : A