HP Aruba Certified Network Security Associate HPE6-A78 Exam Questions
Which is a correct description of a Public Key Infrastructure (PKI)?
Answer : D
Public Key Infrastructure (PKI) relies on a trusted root Certification Authority (CA) to issue certificates. Devices and users must trust the root CA for the PKI to be effective. If a root CA certificate is not pre-installed or manually chosen to be trusted on a device, any certificates issued by that CA will not be inherently trusted by the device.
Refer to the exhibit.
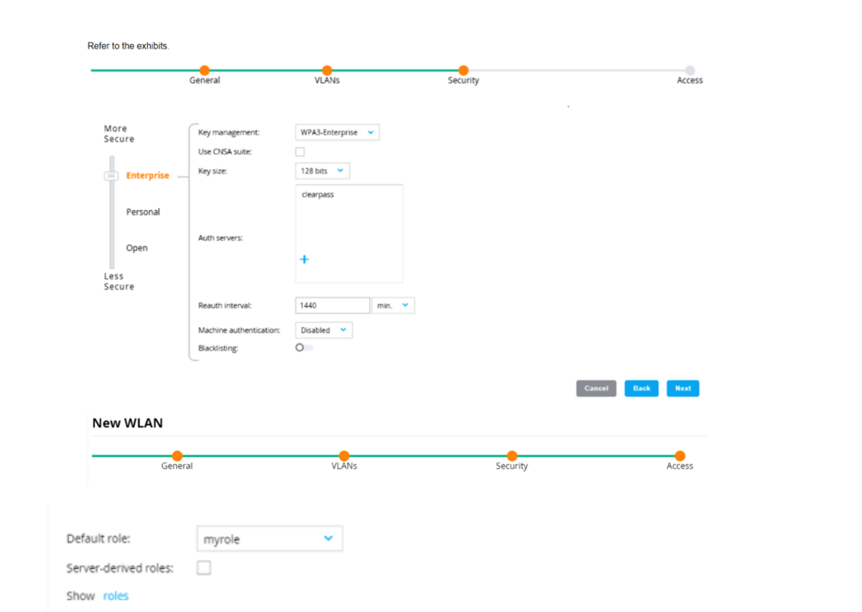
An admin has created a WLAN that uses the settings shown in the exhibits (and has not otherwise adjusted the settings in the AAA profile) A client connects to the WLAN Under which circumstances will a client receive the default role assignment?
Answer : D
In the context of an Aruba Mobility Controller (MC) configuration, a client will receive the default role assignment if they have passed 802.1X authentication and the authentication server did not send an Aruba-User-Role Vendor Specific Attribute (VSA). The default role is assigned by the MC when a client successfully authenticates but the authentication server provides no specific role instruction. This behavior ensures that a client is not left without any role assignment, which could potentially lead to a lack of network access or access control. This default role assignment mechanism is part of Aruba's role-based access control, as documented in the ArubaOS user guide and best practices.
You are checking the Security Dashboard in the Web UI for your AOS solution and see that Wireless Intrusion Prevention (WIP) has discovered a rogue radio operating in ad hoc mode with open security. What correctly describes a threat that the radio could pose?
Answer : B
The AOS Security Dashboard in an AOS-8 solution (Mobility Controllers or Mobility Master) provides visibility into wireless threats detected by the Wireless Intrusion Prevention (WIP) system. The scenario describes a rogue radio operating in ad hoc mode with open security. Ad hoc mode in 802.11 allows devices to communicate directly with each other without an access point (AP), forming a peer-to-peer network. Open security means no encryption or authentication is required to connect.
Ad Hoc Mode Threat: An ad hoc network created by a rogue device can pose significant risks, especially if a corporate client connects to it. Since ad hoc mode allows direct device-to-device communication, a client that joins the ad hoc network might inadvertently bridge the corporate LAN to the rogue network, especially if the client is also connected to the corporate network (e.g., via a wired connection or another wireless interface).
Option B, 'It could open a backdoor into the corporate LAN for unauthorized users,' is correct. If a corporate client connects to the rogue ad hoc network (e.g., due to a misconfiguration or auto-connect setting), the client might bridge the ad hoc network to the corporate LAN, allowing unauthorized users on the ad hoc network to access corporate resources. This is a common threat with ad hoc networks, as they bypass the security controls of the corporate AP infrastructure.
Option A, 'It could be attempting to conceal itself from detection by changing its BSSID and SSID frequently,' is incorrect. While changing BSSID and SSID can be a tactic to evade detection, this is not a typical characteristic of ad hoc networks and is not implied by the scenario. Ad hoc networks are generally visible to WIP unless explicitly hidden.
Option C, 'It is running in a non-standard 802.11 mode and could effectively jam the wireless signal,' is incorrect. Ad hoc mode is a standard 802.11 mode, not a non-standard one. While a rogue device could potentially jam the wireless signal, this is not a direct threat posed by ad hoc mode with open security.
Option D, 'It is flooding the air with many wireless frames in a likely attempt at a DoS attack,' is incorrect. There is no indication in the scenario that the rogue radio is flooding the air with frames. While ad hoc networks can be used in DoS attacks, the primary threat in this context is the potential for unauthorized access to the corporate LAN.
The HPE Aruba Networking AOS-8 8.11 User Guide states:
'A rogue radio operating in ad hoc mode with open security poses a significant threat, as it can open a backdoor into the corporate LAN. If a corporate client connects to the ad hoc network, it may bridge the ad hoc network to the corporate LAN, allowing unauthorized users to access corporate resources. This is particularly dangerous if the client is also connected to the corporate network via another interface.' (Page 422, Wireless Threats Section)
Additionally, the HPE Aruba Networking Security Guide notes:
'Ad hoc networks detected by WIP are a concern because they can act as a backdoor into the corporate LAN. A client that joins an ad hoc network with open security may inadvertently allow unauthorized users to access the corporate network, bypassing the security controls of authorized APs.' (Page 73, Ad Hoc Network Threats Section)
:
HPE Aruba Networking AOS-8 8.11 User Guide, Wireless Threats Section, Page 422.
HPE Aruba Networking Security Guide, Ad Hoc Network Threats Section, Page 73.
===========
How does the AOS firewall determine which rules to apply to a specific client's traffic?
Answer : A
In an AOS-8 architecture, the Mobility Controller (MC) includes a stateful firewall that enforces policies on client traffic. The firewall uses user roles to apply policies, allowing granular control over traffic based on the client's identity and context.
User Roles: In AOS-8, each client is assigned a user role after authentication (e.g., via 802.1X, MAC authentication, or captive portal). The user role contains firewall policies (rules) that define what traffic is allowed or denied for clients in that role. For example, a 'guest' role might allow only HTTP/HTTPS traffic, while an 'employee' role might allow broader access.
Option A, 'The firewall applies the rules in policies associated with the client's user role,' is correct. The AOS firewall evaluates traffic based on the user role assigned to the client. Each role has a set of policies (rules) that are applied in order, and the first matching rule determines the action (permit or deny). For example, if a client is in the 'employee' role, the firewall applies the rules defined in the 'employee' role's policy.
Option B, 'The firewall applies every rule that includes the client's IP address as the source,' is incorrect. The firewall does not apply rules based solely on the client's IP address; it uses the user role. Rules within a role may include IP addresses, but the role determines which rules are evaluated.
Option C, 'The firewall applies the rules in policies associated with the client's WLAN,' is incorrect. While the WLAN configuration defines the initial role for clients (e.g., the default 802.1X role), the firewall applies rules based on the client's current user role, which may change after authentication (e.g., via a RADIUS VSA like Aruba-User-Role).
Option D, 'The firewall applies every rule that includes the client's IP address as the source or destination,' is incorrect for the same reason as Option B. The firewall uses the user role to determine which rules to apply, not just the client's IP address.
The HPE Aruba Networking AOS-8 8.11 User Guide states:
'The AOS firewall on the Mobility Controller applies rules based on the user role assigned to a client. Each user role contains a set of firewall policies that define the allowed or denied traffic for clients in that role. For example, a policy in the 'employee' role might include a rule like ipv4 user any http permit to allow HTTP traffic. The firewall evaluates the rules in the client's role in order, and the first matching rule determines the action for the traffic.' (Page 325, Firewall Policies Section)
Additionally, the HPE Aruba Networking Security Guide notes:
'User roles in AOS-8 provide a powerful mechanism for firewall policy enforcement. The firewall determines which rules to apply to a client's traffic by looking at the policies associated with the client's user role, which is assigned during authentication or via a RADIUS VSA like Aruba-User-Role.' (Page 50, Role-Based Access Control Section)
:
HPE Aruba Networking AOS-8 8.11 User Guide, Firewall Policies Section, Page 325.
HPE Aruba Networking Security Guide, Role-Based Access Control Section, Page 50.
Refer to the exhibit, which shows the current network topology.

You are deploying a new wireless solution with an Aruba Mobility Master (MM). Aruba Mobility Controllers (MCs). and campus APs (CAPs). The solution will Include a WLAN that uses Tunnel for the forwarding mode and Implements WPA3-Enterprise security
What is a guideline for setting up the vlan for wireless devices connected to the WLAN?
Answer : B
When setting up VLANs for a wireless solution with an Aruba Mobility Master (MM), Aruba Mobility Controllers (MCs), and campus APs (CAPs), it is recommended to use wireless user roles to assign devices to different VLANs. This allows for greater flexibility and control over network resources and policies applied to different user groups. Wireless user roles can dynamically assign devices to the appropriate VLAN based on a variety of criteria such as user identity, device type, location, and the resources they need to access. This approach aligns with the ArubaOS features that leverage user roles for network access control, as detailed in Aruba's configuration and administration guides.
A client has accessed an HTTPS server at myhost1.example.com using Chrome. The server sends a certificate that includes these properties:
Subject name: myhost.example.com
SAN: DNS: myhost.example.com; DNS: myhost1.example.com
Extended Key Usage (EKU): Server authentication
Issuer: MyCA_Signing
The server also sends an intermediate CA certificate for MyCA_Signing, which is signed by MyC
Answer : A, A
When a client (e.g., a Chrome browser) accesses an HTTPS server, the server presents a certificate to establish a secure connection. The client must validate the certificate to trust the server. The certificate in this scenario has the following properties:
Subject name: myhost.example.com
SAN (Subject Alternative Name): DNS: myhost.example.com; DNS: myhost1.example.com
Extended Key Usage (EKU): Server authentication
Issuer: MyCA_Signing (an intermediate CA)
The server also sends an intermediate CA certificate for MyCA_Signing, signed by MyCA (the root CA).
The client's Trusted CA Certificate list does not include MyCA or MyCA_Signing.
Certificate Validation Process:
Name Validation: The client checks if the server's hostname (myhost1.example.com) matches the Subject name or a SAN in the certificate. Here, the SAN includes 'myhost1.example.com,' so the name validation passes.
EKU Validation: The client verifies that the certificate's EKU includes 'Server authentication,' which is required for HTTPS. The EKU is correctly set to 'Server authentication,' so this validation passes.
Chain of Trust Validation: The client builds a certificate chain from the server's certificate to a trusted root CA in its Trusted CA Certificate list. The chain is:
Server certificate (issued by MyCA_Signing)
Intermediate CA certificate (MyCA_Signing, issued by MyCA)
Root CA certificate (MyCA, which should be in the client's trust store) The client's Trusted CA Certificate list does not include MyCA or MyCA_Signing, meaning the client cannot build a chain to a trusted root CA. This causes the validation to fail.
Option A, 'The client does not have the correct trusted CA certificates,' is correct. The client's trust store must include the root CA (MyCA) to trust the certificate chain. Since MyCA is not in the client's Trusted CA Certificate list, the client cannot validate the chain, and the certificate is not trusted.
Option B, 'The certificate lacks a valid SAN,' is incorrect. The SAN includes 'myhost1.example.com,' which matches the server's hostname, so the SAN is valid.
Option C, 'The certificate lacks the correct EKU,' is incorrect. The EKU is set to 'Server authentication,' which is appropriate for HTTPS.
Option D, 'The certificate lacks a valid SAN, and the client does not have the correct trusted CA certificates,' is incorrect because the SAN is valid, as explained above. The only issue is the missing trusted CA certificates.
The HPE Aruba Networking AOS-CX 10.12 Security Guide states:
'For a client to trust a server's certificate during HTTPS communication, the client must validate the certificate chain to a trusted root CA in its trust store. If the root CA (e.g., MyCA) or intermediate CA (e.g., MyCA_Signing) is not in the client's Trusted CA Certificate list, the chain of trust cannot be established, and the client will reject the certificate. The Subject Alternative Name (SAN) must include the server's hostname, and the Extended Key Usage (EKU) must include 'Server authentication' for HTTPS.' (Page 205, Certificate Validation Section)
Additionally, the HPE Aruba Networking Security Fundamentals Guide notes:
'A common reason for certificate validation failure is the absence of the root CA certificate in the client's trust store. For example, if a server's certificate is issued by an intermediate CA (e.g., MyCA_Signing) that chains to a root CA (e.g., MyCA), the client must have the root CA certificate in its Trusted CA Certificate list to trust the chain.' (Page 45, Certificate Trust Issues Section)
:
HPE Aruba Networking AOS-CX 10.12 Security Guide, Certificate Validation Section, Page 205.
HPE Aruba Networking Security Fundamentals Guide, Certificate Trust Issues Section, Page 45.
===========
You are checking the Security Dashboard in the Web Ul for your ArubaOS solution and see that Wireless Intrusion Prevention (WIP) has discovered a rogue radio operating in ad hoc mode with open security. What correctly describes a threat that the radio could pose?
Answer : A
A rogue radio operating in ad hoc mode with open security can pose several threats to a network. Ad hoc networks allow direct device-to-device communication without centralized control. If such a radio is present within or near a corporate environment, it can potentially be used to create a peer-to-peer network that bypasses corporate security controls, effectively acting as a backdoor into the corporate network for unauthorized users or devices. This can lead to a breach of data security and unauthorized access to network resources.