HP Aruba Certified Network Security Expert Written HPE6-A84 Exam Questions
A customer has an AOS 10 architecture, which includes Aruba APs. Admins have recently enabled WIDS at the high level. They also enabled alerts and email notifications for several events, as shown in the exhibit.

Admins are complaining that they are getting so many emails that they have to ignore them, so they are going to turn off all notifications.
What is one step you could recommend trying first?
Answer : C
According to the AOS 10 documentation1, WIDS is a feature that monitors the radio spectrum for the presence of unauthorized, rogue access points and the use of wireless attack tools. WIDS can be configured at different levels, such as low, medium, high, or custom. The higher the level, the more checks are enabled and the more alerts are generated. However, not all checks are equally relevant or indicative of real threats. Some checks may generate false positives or unnecessary alerts that can overwhelm the administrators and reduce the effectiveness of WIDS.
Therefore, one step that could be recommended to reduce the number of email notifications is to change the WIDS level to custom, and enable only the checks most likely to indicate real threats. This way, the administrators can fine-tune the WIDS settings to suit their network environment and security needs, and avoid getting flooded with irrelevant or redundant alerts. Option C is the correct answer.
Option A is incorrect because sending the email notifications directly to a specific folder and only checking the folder once a week is not a good practice for security management. This could lead to missing or ignoring important alerts that require immediate attention or action. Moreover, this does not solve the problem of getting too many emails in the first place.
Option B is incorrect because disabling email notifications for Rogue AP, but leaving the Infrastructure Attack Detected and Client Attack Detected notifications on, is not a sufficient solution. Rogue APs are unauthorized access points that can pose a serious security risk to the network, as they can be used to intercept or steal sensitive data, launch attacks, or compromise network performance. Therefore, disabling email notifications for Rogue APs could result in missing critical alerts that need to be addressed.
Option D is incorrect because disabling just the Rogue AP and Client Attack Detected alerts, as they overlap with the Infrastructure Attack Detected alert, is not a valid assumption. The Infrastructure Attack Detected alert covers a broad range of attacks that target the network infrastructure, such as deauthentication attacks, spoofing attacks, denial-of-service attacks, etc. The Rogue AP and Client Attack Detected alerts are more specific and focus on detecting and classifying rogue devices and clients that may be involved in such attacks. Therefore, disabling these alerts could result in losing valuable information about the source and nature of the attacks.
Refer to the scenario.
# Introduction to the customer
You are helping a company add Aruba ClearPass to their network, which uses Aruba network infrastructure devices.
The company currently has a Windows domain and Windows C
Answer : A, A
Refer to the exhibit.

Aruba ClearPass Policy Manager (CPPM) is using the settings shown in the exhibit. You reference the tag shown in the exhibit in enforcement policies related to NASes of several types, including Aruba APs, Aruba gateways, and AOS-CX switches.
What should you do to ensure that clients are reclassified and receive the correct treatment based on the tag?
Answer : C
According to the ClearPass Policy Manager User Guide1, the tag shown in the exhibit is a Device Insight tag, which is used to classify and identify devices based on their behavior and characteristics. Device Insight tags can be used as conditions in enforcement policies to apply different actions or roles to devices based on their tags. However, in order to ensure that devices are reclassified and receive the correct treatment based on their tags, profiling must be enabled in each service that uses one of these enforcement profiles. Profiling is a feature that allows ClearPass to dynamically discover and profile devices on the network, and update their attributes and tags accordingly. Profiling also allows ClearPass to send RADIUS Change of Authorization (CoA) messages to the network access servers (NASes) that control the access of the devices, and instruct them to reauthenticate or terminate the sessions of the devices that have changed their tags. The profiling action must be set to the correct one for the NASes using that service, as different NASes may support different types of CoA messages. Therefore, option C is the correct answer.
You are working with a developer to design a custom NAE script for a customer. You are helping the developer find the correct REST API resource to monitor.
Refer to the exhibit below.

What should you do before proceeding?
Answer : B
The exhibit shows the ArubaOS-CX REST API documentation interface, which allows you to explore the available resources and try out the API calls using the ''Try it out'' button. However, before you can use this feature, you need to authenticate yourself with your Aruba passport account and collect a token that will be used for subsequent requests. This token will expire after a certain time, so you need to refresh it periodically.You can find more details about how to use the documentation interface and collect a token in theArubaOS-CX REST API Guide1.
A company has an Aruba ClearPass server at 10.47.47.8, FQDN radius.acnsxtest.local. This exhibit shows ClearPass Policy Manager's (CPPM's) settings for an Aruba Mobility Controller (MC).
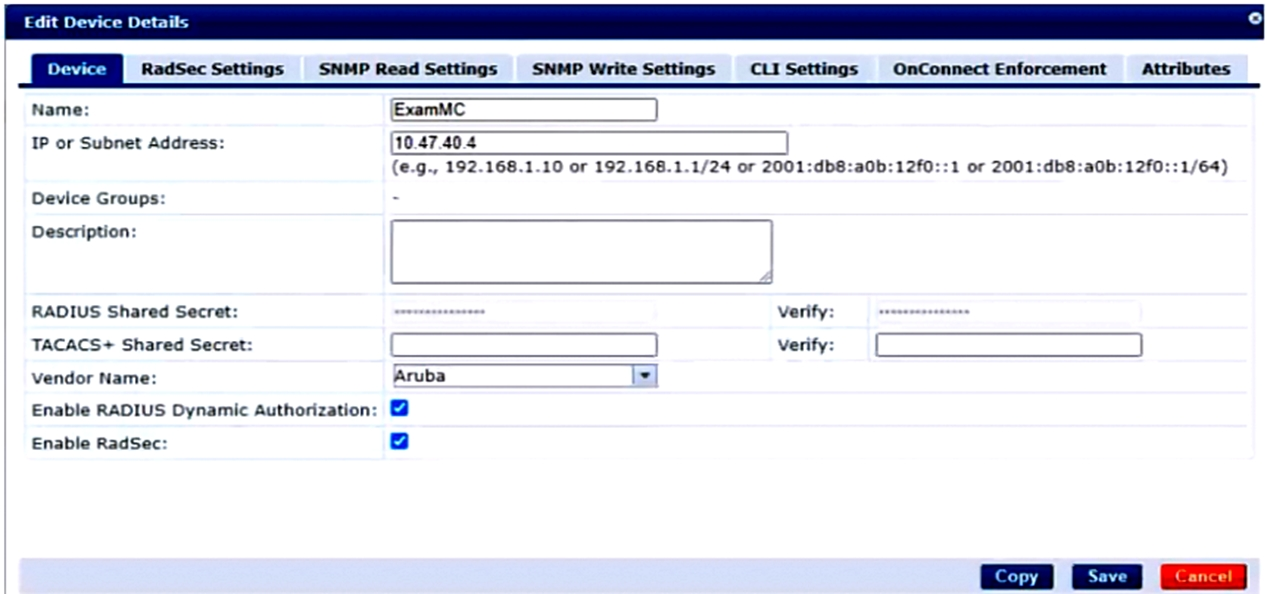
The MC is already configured with RADIUS authentication settings for CPPM, and RADIUS requests between the MC and CPPM are working. A network admin enters and commits this command to enable dynamic authorization on the MC:
aaa rfc-3576-server 10.47.47.8
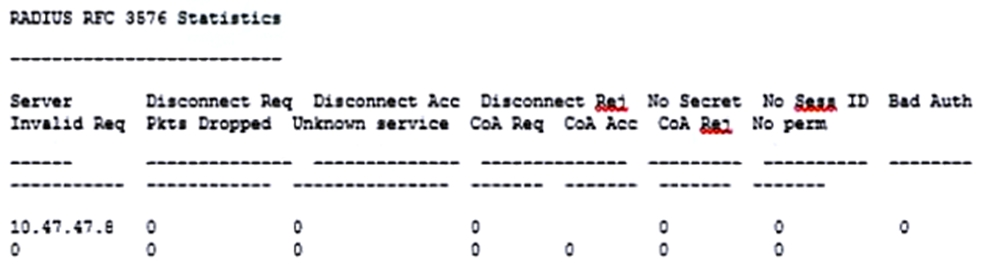
But when CPPM sends CoA requests to the MC, they are not working. This exhibit shows the RFC 3576 server statistics on the MC:
How could you fix this issue?
Answer : A
Dynamic authorization is a feature that allows CPPM to send change of authorization (CoA) or disconnect messages to the MC to modify or terminate a user session based on certain conditions or events1.Dynamic authorization uses the RFC 3576 protocol, which is an extension of the RADIUS protocol2.
To enable dynamic authorization on the MC, you need to configure the IP address and UDP port of the CPPM server as the RFC 3576 server on the MC3. The default UDP port for RFC 3576 is 3799, but it can be changed on the CPPM server .The MC and CPPM must use the same UDP port for dynamic authorization to work properly3.
In this scenario, the MC is configured with the IP address of the CPPM server (10.47.47.8) as the RFC 3576 server, but it is using the default UDP port of 3799. However, according to the exhibit, the CPPM server is using a different UDP port of 1700 for dynamic authorization . This mismatch causes the CoA requests from CPPM to fail on the MC, as shown by the statistics .
To fix this issue, you need to change the UDP port in the MCs' RFC 3576 server config to match the UDP port used by CPPM, which is 1700 in this case. Alternatively, you can change the UDP port in CPPM to match the default UDP port of 3799 on the MC.Either way, you need to ensure that both devices use the same UDP port for dynamic authorization3.
How does Aruba Central handle security for site-to-site connections between AOS 10 gateways?
Answer : B
Aruba Central supports site-to-site VPNs between AOS 10 gateways, which are Aruba devices that provide routing, firewall, and VPN functions. Aruba Central can automatically provision and manage the site-to-site VPNs using the VPN Manager feature.The VPN Manager allows you to create VPN groups that consist of one or more hubs and branches, and define the VPN settings for each group1
Aruba Central uses IPsec as the protocol to secure the site-to-site connections between the AOS 10 gateways. IPsec is a standard protocol that provides encryption, authentication, and integrity for IP packets. Aruba Central automatically establishes IPsec tunnels for all site-to-site connections using keys that are securely distributed by Central. The keys are generated by Central and pushed to the gateways using a secure channel.The keys are rotated periodically to enhance security2
Refer to the scenario.
A customer is using an AOS 10 architecture with Aruba APs and Aruba gateways (two per site). Admins have implemented auto-site clustering for gateways with the default gateway mode disabled. WLANs use tunneled mode to the gateways.
The WLAN security is WPA3-Enterprise with authentication to an Aruba ClearPass Policy Manager (CPPM) cluster VIP. RADIUS communications use RADIUS, not RadSec.
For which devices does CPPM require network device entries?
Answer : A
ClearPass Policy Manager (CPPM) requires network device entries for the devices that communicate with it using RADIUS or TACACS+ protocols. In this scenario, the gateways are the devices that act as RADIUS clients and send authentication requests to CPPM for the WLAN users. Therefore, CPPM needs to have network device entries for the gateways' actual IP addresses and the shared secrets that match the ones configured on the gateways.
Additionally, CPPM also requires network device entries for the gateways' dynamic authorization VRRP addresses, which are used for sending CoA messages to the gateways. CoA messages are used to change the attributes or status of a user session on the gateways without requiring re-authentication. For example, CPPM can use CoA to apply policies, roles, or bandwidth limits based on various conditions. To enable VRRP IP addresses for dynamic authorization, you need to set up gateway clusters manually and assign a VRRP VLAN and a VRRP IP address to each cluster. This way, CPPM can use the VRRP IP address as the NAS IP address for RADIUS communications and CoA messages. The VRRP IP address will remain the same even if the active gateway in the cluster changes due to a failover event, ensuring seamless operations.