HP Aruba Certified Campus Access Associate HPE6-A85 Exam Questions
Describe the purpose of the administrative distance
Answer : B
The administrative distance is used as a trust rating for route entries (B). It is a metric used by routers to select the best path when there are two or more different routes to the same destination from two different routing protocols. The lower the administrative distance value, the more trustworthy the source of the route. For example, a directly connected network has an administrative distance of 0 because it is the most trusted source of routing information. In contrast, routes learned from different routing protocols have higher administrative distances, reflecting their relative trustworthiness.
Two independent ArubaOS-CX 6300 switches with Spanning Tree (STP) settings are interconnected with two cables between ports 1/1/1 and 1/1/2 All four ports have "no shutdown" and "no routing" commands
How will STP forward or discard traffic on these ports?
Answer : D
The way that STP Spanning Tree Protocol. STP is a network protocol that ensures a loop-free topology for any bridged Ethernet local area network by preventing redundant paths between switches or bridges from creating loops that cause broadcast storms, multiple frame transmission, and MAC table instability.STP creates a logical tree structure that spans all of the switches in an extended network and blocks any redundant links that are not part of the tree from forwarding data packets3. will forward or discard traffic on these ports is as follows:
STP will elect a root bridge among the two switches based on their bridge IDs, which are composed of a priority value and a MAC address. The switch with the lower bridge ID will become the root bridge and will forward traffic on all its ports.
STP will assign a role and a state to each port on both switches based on their port IDs, which are composed of a priority value and a port number. The port with the lower port ID will become the designated port and will forward traffic, while the port with the higher port ID will become the alternate port and will discard traffic.
In this scenario, since both switches have two cables connected between ports 1/1/1 and 1/1/2, there will be two possible paths between them, creating a loop. To prevent this loop, STP will block one of these paths by discarding traffic on one of the ports on each switch.
Assuming that both switches have the same priority value (default is 32768), the switch with the lower MAC address will have the lower bridge ID and will become the root bridge. The root bridge will forward traffic on both ports 1/1/1 and 1/1/2.
Assuming that both ports have the same priority value (default is 128), port 1/1/1 will have a lower port ID than port 1/1/2 on both switches because it has a lower port number. Port 1/1/1 will become the designated port and will forward traffic, while port 1/1/2 will become the alternate port and will discard traffic.
Therefore, the switch with the lower MAC address will discard traffic on one port (port 1/1/2), while the switch with the higher MAC address will also discard traffic on one port (port 1/1/2).
You need to drop excessive broadcast traffic on ingress to an ArubaOS-CX switch What is the best technology to use for this task?
Answer : A
The best technology to use for dropping excessive broadcast traffic on ingress to an ArubaOS-CX switch is rate limiting. Rate limiting is a feature that allows network administrators to control the amount of traffic that enters or leaves a port or a VLAN on a switch by setting bandwidth thresholds or limits. Rate limiting can be used to prevent network congestion, improve network performance, enforce service level agreements (SLAs), or mitigate denial-of-service (DoS) attacks. Rate limiting can be applied to broadcast traffic on ingress to an ArubaOS-CX switch by using the storm-control command in interface configuration mode. This command allows network administrators to specify the percentage of bandwidth or packets per second that can be used by broadcast traffic on an ingress port. If the broadcast traffic exceeds the specified threshold, the switch will drop the excess packets.
The other options are not technologies for dropping excessive broadcast traffic on ingress because:
DWRR queuing: DWRR stands for Deficit Weighted Round Robin, which is a queuing algorithm that assigns different weights or priorities to different traffic classes or queues on an egress port. DWRR ensures that each queue gets its fair share of bandwidth based on its weight while avoiding starvation of lower priority queues. DWRR does not drop excessive broadcast traffic on ingress, but rather schedules outgoing traffic on egress.
QoS shaping: QoS stands for Quality of Service, which is a set of techniques that manage network resources and provide different levels of service to different types of traffic based on their requirements. QoS shaping is a technique that delays or buffers outgoing traffic on an egress port to match the available bandwidth or rate limit. QoS shaping does not drop excessive broadcast traffic on ingress, but rather smooths outgoing traffic on egress.
Strict queuing: Strict queuing is another queuing algorithm that assigns different priorities to different traffic classes or queues on an egress port. Strict queuing ensures that higher priority queues are always served before lower priority queues regardless of their bandwidth requirements or weights. Strict queuing does not drop excessive broadcast traffic on ingress, but rather schedules outgoing traffic on egress.
You need to troubleshoot an Aruba CX 6200 4-node VSF stack switch that fails to boot correctly Select the option that allows you to access the switch and see the boot options available for OS images and ServiceOS.
Answer : A
To troubleshoot an Aruba CX 6200 switch that is failing to boot correctly, accessing the switch via the RJ-45 console port on any of its member switches provides direct access to the switch's console for troubleshooting. This method allows a network technician to interact with the boot process, view boot messages, and access boot options, including the selection of different OS images or ServiceOS for recovery purposes.
What is used by network devices to send error and operational information related to IP communications?
Answer : D
ICMP (Internet Control Message Protocol) is used by network devices to send error and operational information related to IP communications. It is used to send messages like 'destination unreachable' or 'time exceeded' when there are issues in IP communication
Refer to the exhibit.
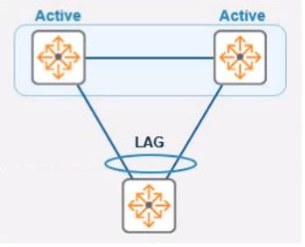
In the given topology, a pair of Aruba CX 8325 switches are in a VSX stack using the active gateway What is the nature and behavior of the Virtual IP for the VSX pair if clients are connected to the access switch using VSX as the default gateway?
Answer : B
In a Virtual Switching Extension (VSX) stack, the Virtual IP (VIP) provides a single default gateway IP address for clients connected to the access switch. This VIP is a floating IP that is active on the primary VSX switch. In the event of a failure of the primary switch, the VIP will failover to the secondary switch, ensuring that client traffic can continue to be routed without disruption.
When performing live firmware upgrades on Aruba APs. which technology partitions all the APs based on RF neighborhood data minimizing the impact on clients?
Answer : C
Aruba AirMatch is a feature that optimizes RF Radio Frequency. RF is any frequency within the electromagnetic spectrum associated with radio wave propagation. When an RF current is supplied to an antenna, an electromagnetic field is created that then is able to propagate through space. performance and user experience by using machine learning algorithms and historical data to dynamically adjust AP power levels, channel assignments, and channel width. AirMatch performs live firmware upgrades on Aruba APs by partitioning all the APs based on RF neighborhood data and minimizing the impact on clients. AirMatch uses a rolling upgrade process that upgrades one partition at a time while ensuring that adjacent partitions are not upgraded simultaneously. Reference: https://www.arubanetworks.com/assets/ds/DS_AirMatch.pdf https://www.arubanetworks.com/techdocs/ArubaOS_86_Web_Help/Content/arubaos-solutions/arm/AirMatch.htm