HP Aruba Certified Campus Access Mobility Expert Written HPE7-A07 Exam Questions
A customer is evaluating device profiles on a CX 6300 switch. The test device has the following attributes:
* MAC address = 81:cd:93:13:ab:31
* LLDP sys-desc = iotcontroller
The test device is being assigned to the ''lot-dev'' role However, the customer requires the "lot-prod'' role be applied.
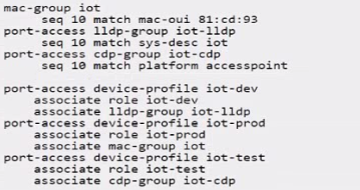
Given the configuration, what is causing the "iot-dev" role to be applied to the device'?
Answer : D
In device profile configuration, the device role is often determined by matching attributes such as MAC address, LLDP system description, and CDP information against defined conditions. The test device is being assigned the 'iot-dev' role because its LLDP system description matches the 'iot-lldp' group configuration that is associated with the 'iot-dev' role.
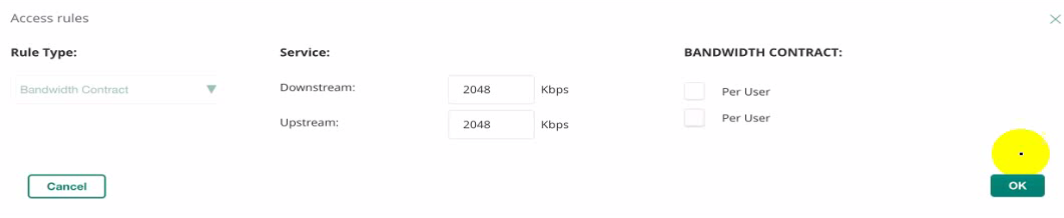
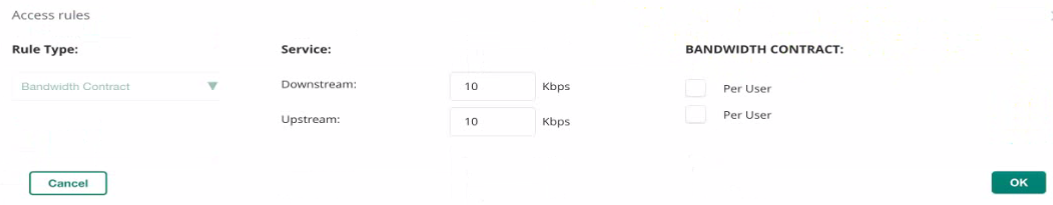
Which option shows the correct Banawidth Control for 1024 kbps down and 2048 Kops up for the SSID?
A)
B)
C)
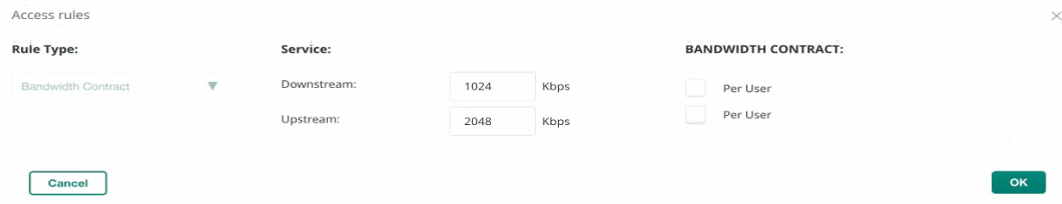
D)

Answer : D
The correct Bandwidth Control settings for 1024 Kbps down and 2048 Kbps up for the SSID are shown in Option D. In Option D, the downstream is set at 1024 Kbps and the upstream at 2048 Kbps, both configured per user, which matches the requested configuration. This setup ensures that each user has a guaranteed bandwidth allocation of the specified rates when connected to the SSID, providing a controlled and predictable user experience.
You configured" a bridged mode SSID with WPA3-Enterprise and EAP-TLS security. When you connect an Active Directory joined client that has valid client certificates. ClearPass shows the following error.
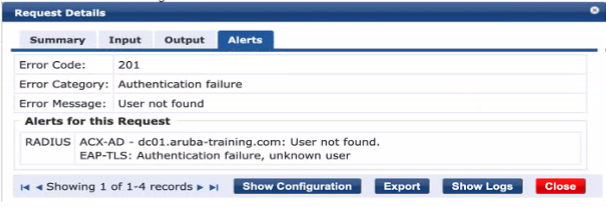
What is needed to resolve this issue?
Answer : C
The error message 'User not found' indicates that the authentication source, in this case, Active Directory (AD), is not able to locate the user account based on the current search parameters. This often occurs when the User Principal Name (UPN) that the client is using to authenticate is not included in the search parameters of the AD authentication source within ClearPass. By modifying the AD authentication source to include the UPN in the search, ClearPass will be able to correctly locate the user account and proceed with the authentication using the valid client certificates.
A customer is evaluating device profiles on a CX 6300 switch. The test device has the following attribute:
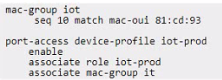
* MAC address=81:cd:93:13:ab:31
The test device needs to be assigned the "lot-prod'' role, in addition the "lot-default" role must be applied for any other device connected lo interface 1/1/1. This is a lab environment with no configuration of any external authentication server for the test.
Given the configuration example, what is required to meet this testing requirement?
Answer : B
The fallback role is used as a default role in the absence of a specified role or when an authentication server is not available. Given the scenario, where the test device with MAC address 81:cd:93:13:ab:31 needs to be assigned to 'iot-prod' and other devices to 'iot-default', and considering there is no external authentication server configured for the test, the appropriate action would be to set a global fallback role that applies to all devices connecting to the network. This ensures that any device that does not match the specific device profile will inherit the 'iot-default' role. Since the configuration for a specific MAC address (81:cd:93:xx:xx:xx) to associate with the 'iot-prod' role is already in place, setting the fallback role globally accommodates the requirement for other devices.
You configured a WPA3-SAE with the following MAC Authentication Role Mapping in Cloud Authentication and Policy:
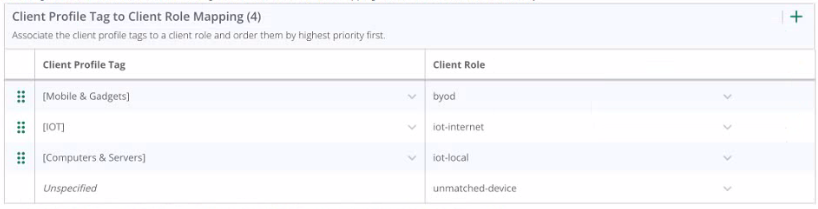
With further default settings assume a new Android phone is connected to the network. Which role will the client be assigned after connecting for the first time?
Answer : D
The configuration shown in the third exhibit details a client role mapping that associates different client profile tags with specific client roles. When a new device, such as an Android phone, connects to the network, it will be profiled and assigned a role based on the mappings defined. If the device does not match any predefined profiles, it would be assigned the 'unmatched-device' role. This is under the assumption that default settings are in place and the client does not match the criteria for any of the specific roles like 'byod', 'iot-internet', or 'iot-local'. Therefore, an Android phone connecting for the first time and not matching any specific profile tag would be assigned to the 'unmatched-device' role.
Your customer asked for help to apply an ACL for wireless guest users with the following criteria:
* Wi-Fi guests are on VLAN 555
* allow internet access
* only allow access to public DNS servers
* deny access to all internal networks except for any DHCP server
These session ACLs are already present in the CLI of the mobility gateway group:
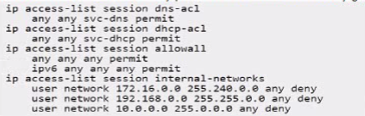
You have access to the CLl. Which user role meets all the criteria?
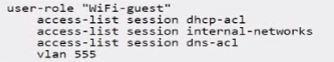
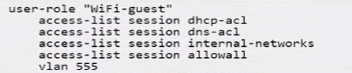
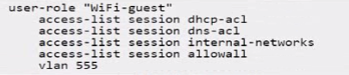
A)
B)
C)
D)
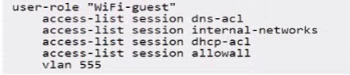
Answer : A
Based on the criteria provided for wireless guest users, the correct user role configuration must allow internet access, only allow access to public DNS servers, deny access to all internal networks except for any DHCP server, and place the Wi-Fi guests on VLAN 555. The ACLs must permit services necessary for basic internet access (such as DNS and DHCP) and block access to internal networks.
Option A satisfies these criteria with the following configurations:
user-role 'WiFi-guest': This defines the role for Wi-Fi guests.
access-list session dhcp-acl: This applies the access list that likely permits DHCP, which is necessary for guests to obtain an IP address.
access-list session dns-acl: This applies the DNS access list, which likely restricts guests to using public DNS servers.
access-list session internal-networks: This applies the internal networks access list, which denies access to internal networks.
vlan 555: This sets the VLAN for Wi-Fi guests to 555.
Options B, C, and D are incorrect because they include access-list session allowall which would permit all traffic, contradicting the requirement to deny access to all internal networks.
Exhibit.
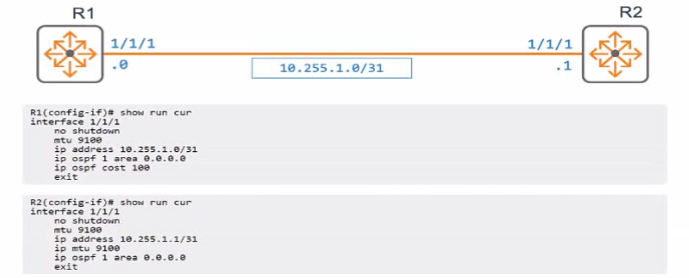
An engineer has applied the above configuration to R1 and R2 However the routers OSPF adjacency never progresses past the "EXSTART-DR" slate as shown below.
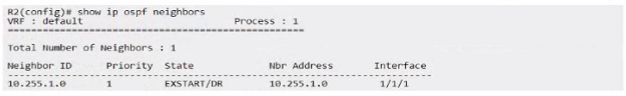
Which configuration action on either router will allow R1 and R2 to progress past the "EXSTART/DR" state?
Answer : A
In OSPF, the 'EXSTART/DR' state indicates that the routers are trying to establish an adjacency but are unable to progress. This can happen if the OSPF network type is incorrectly configured for the type of connection between the routers. Given that R1 and R2 are connected via a point-to-point link (as suggested by the /31 subnet), setting the network type to point-to-point on both routers will remove the need for DR/BDR election, which is unnecessary on a point-to-point link, and allow OSPF to progress past the 'EXSTART' state and form a full adjacency.