Huawei HCIP-Security-CISN V3.0 H12-721 HCIP-Security-CISN Exam Questions
The classification of cyber-attacks includes traffic-based attacks, scanning and snooping attacks, malformed packet attacks, and special packet attacks.
Answer : A
Which of the following is a disadvantage of L2TP VPN?
Answer : D
The Haiwei Secoway VPN client initiates an L2TP connection. The source port of the L2TP packet is 1710 and the port 1710 of the destination port.
Answer : A
Note: Haiwei Secoway VPN is Huawei's VPN product, using the standard L2TP protocol, the destination port number uses UDP 1701; if using L2TP over IPSec technology, it uses UDP 500 and UDP4500 ports, if the port in the question If the number is not a mistake, the correct answer should be B, which is false.
The malformed packet attack technology uses some legitimate packets to perform reconnaissance or data detection on the network. These packets are legal application types, but only normal network packets are rarely used.
Answer : B
Note: Malformed message attack: By sending a defective message to the target system, the target system will make an error when processing such an IP packet, or cause a system crash, which affects the normal operation of the target system. The main attack methods are: SMURF attack; Second, LAND attack; Third, Fraggle attack; Fourth, IP Fragment attack; Fifth, IP Spoofing attack; Six, Ping of Death attack; Seven, TCP Flag attack; Eight, Tear Drop attack; Nine is the WinNuke attack.
In the L2TP over IPSec application scenario, the USG device encrypts the original data packet with IPSec and then encapsulates the packet with L2TP.
Answer : B
Note: In L2TP over IPSec, packets are encapsulated with L2TP and then encrypted with IPSec. Authentication--L2TP is completed, encryption--IPSec is completed, and there is no direct relationship between authentication and encryption.
By configuring the Bypass interface, you can avoid the network interruption caused by the device fault and improve the reliability of the network. The bypass function can be used to configure the Bypass function by configuring the Bypass parameters on any GE interface.
Answer : A
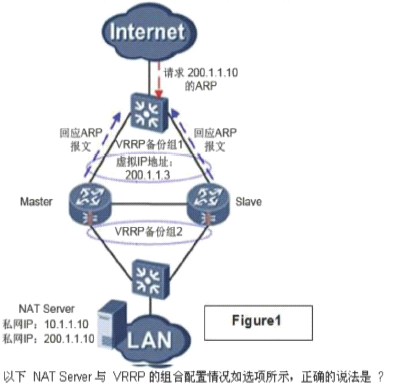
In a dual-system hot standby network, the NAT configurations of the two USGs are consistent. When the address in the NAT address pool is on the same network segment as the virtual IP address of the VRRP backup group, the next two graphs show the ARP response of the NAT server and VRRP combination application (lack of a picture).
Answer : C