Huawei HCIA-Datacom V2.0 H12-811_V2.0 Exam Questions
Which of the following statements are true about the Python code shown below? (Select all that apply)
import paramiko
import time
ssh = paramiko.SSHClient()
ssh.set_missing_host_key_policy(paramiko.AutoAddPolicy())
ssh.connect('192.168.1.254', username='python', password='Huawei@123')
channel = ssh.invoke_shell()
channel.send('screen-length 0 temporary\n')
time.sleep(1)
output = channel.recv(65535).decode('utf-8')
print(output)
ssh.close()
Answer : A, B, C, D
All four statements are correct. The code uses the Paramiko library to automate SSH login to a network device. import paramiko and import time load the Python modules required for SSH communication and delay control, so option C is correct. The statement ssh = paramiko.SSHClient() creates an SSH client object, and ssh.set_missing_host_key_policy(paramiko.AutoAddPolicy()) allows the client to accept an unknown host key automatically in this example scenario.
The command ssh.connect('192.168.1.254', username='python', password='Huawei@123') establishes an SSH connection to the target device, so option B is correct. Then channel = ssh.invoke_shell() opens an interactive shell channel, which is commonly used to send CLI commands and receive output just as an administrator would in a terminal session, making option D correct. The command channel.send('screen-length 0 temporary\n') disables page-by-page output for the current session, which is useful in network automation. Finally, ssh.close() closes the SSH session and releases the connection, so option A is correct. HCIA-Datacom automation knowledge often uses Paramiko examples to demonstrate basic Python-based device O&M.
On the OSPF network shown in the figure, all IP addresses can communicate with each other. Then the following configurations are added on R1:
Which IP address of S1 can successfully ping 10.2.23.3?
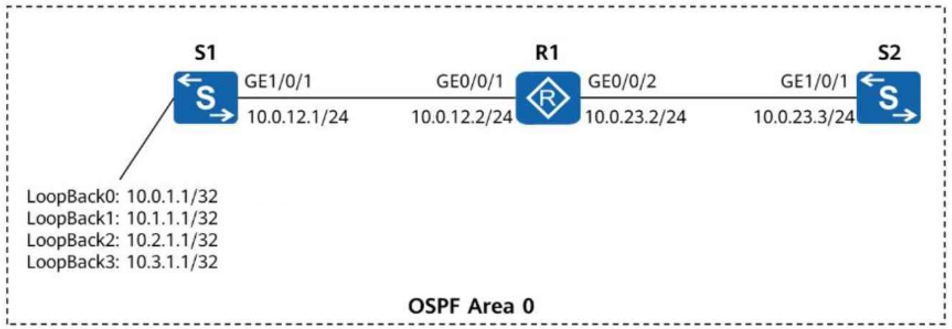
Answer : B
According to the topology and the original question scenario, the correct answer is 10.2.1.1, so option B is selected. In HCIA-Datacom troubleshooting questions of this type, the goal is usually to identify the correct management address, next-hop interface address, or testing destination based on the addressing design shown in the figure.
The answer depends on the role of the device and the direction of the connectivity verification. In such topologies, each interface belongs to a specific network segment, and the selected address must match the intended test target on that segment. If the test is being performed toward the neighboring device or a specific reachable interface, using the correct IP on the proper subnet is essential. An incorrect address may still look familiar from the topology but would not represent the right test endpoint. HCIA-Datacom places strong emphasis on reading topology labels carefully, matching interface addresses to subnet assignments, and choosing the correct destination when using tools such as ping, tracert, or service-specific connectivity tests. This question mainly checks address recognition accuracy in a troubleshooting context.
In the WAC + Fit AP networking, an AP fails to go online. The output of the display ap all command run on the WAC is shown below. According to the command output, which of the following is the possible cause of the AP's failure to go online?
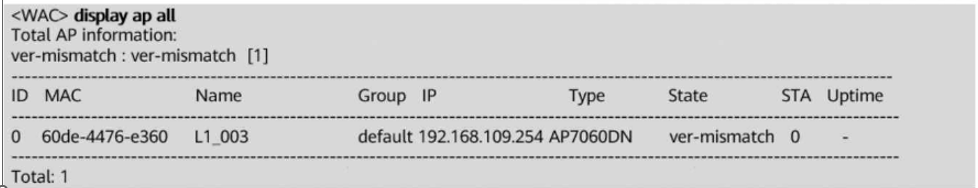
Answer : C
The correct answer is C. In the command output, the AP state is shown as ver-mismatch. This state directly indicates a version mismatch between the AP and the WAC. In Huawei WLAN deployment, a Fit AP must use a software version that is compatible with the WAC version. If the versions do not match, the AP may be discovered by the WAC and appear in the AP list, but it cannot successfully complete the online process.
Option A is incorrect because blacklist-related failures are displayed with blacklist-related status information, not ver-mismatch. Option B is also incorrect because authentication failures normally generate authentication-related fault indications. Option D is incorrect because configuration initialization failure would not be identified by the specific ver-mismatch state.
HCIA-Datacom troubleshooting knowledge emphasizes reading AP online states carefully. Common causes of AP online failure include IP address acquisition failure, CAPWAP tunnel establishment failure, insufficient licenses, authentication problems, and version mismatch. When the state explicitly shows ver-mismatch, the troubleshooting direction is clear: check AP and WAC software compatibility and upgrade or align the software version as needed.
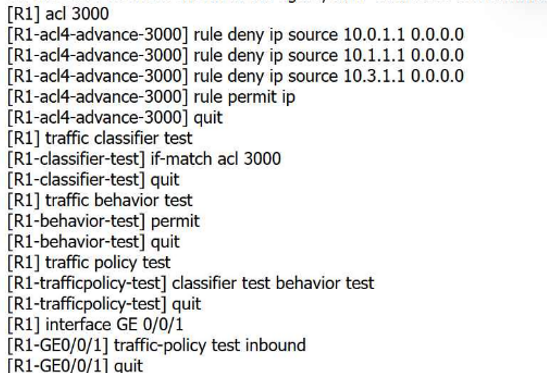
On the OSPF network shown in the figure, all IP addresses can communicate with each other. Then the following configurations are added on R1:
[R1] acl 3000
[R1-acl4-advance-3000] rule deny ip source 10.0.1.1 0.0.0.0
[R1-acl4-advance-3000] rule deny ip source 10.1.1.1 0.0.0.0
[R1-acl4-advance-3000] rule permit ip source 10.3.1.1 0.0.0.0
[R1-acl4-advance-3000] rule permit ip
[R1-acl4-advance-3000] quit
[R1] traffic classifier test
[R1-classifier-test] if-match acl 3000
[R1-classifier-test] quit
[R1] traffic behavior test
[R1-behavior-test] permit
[R1-behavior-test] quit
[R1] traffic policy test
[R1-trafficpolicy-test] classifier test behavior test
[R1-trafficpolicy-test] quit
[R1] interface GE 0/0/1
[R1-GE0/0/1] traffic-policy test outbound
[R1-GE0/0/1] quit
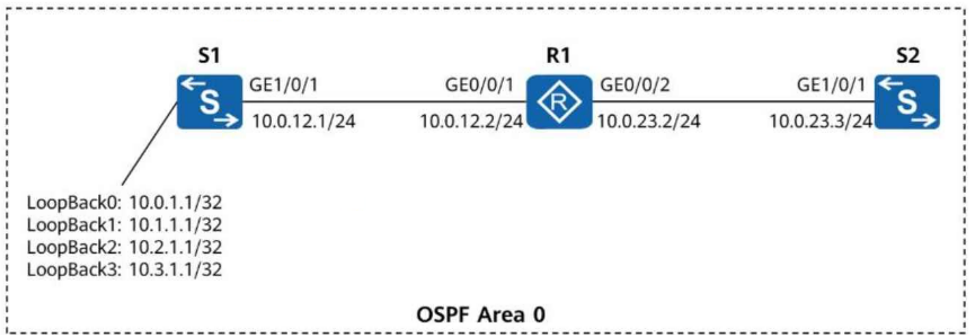
Which IP addresses of S1 can successfully ping 10.0.23.3? (Select all that apply)
Answer : A, B, C, D
All four addresses can successfully ping 10.0.23.3, so the correct answer is A, B, C, D.
The key point is that the traffic policy is applied outbound on GE0/0/1 of R1, which is the interface facing S1. When S1 pings 10.0.23.3, the echo request travels from S1 to R1 and then to S2. The return echo reply from 10.0.23.3 comes back to R1 and is then sent outbound on GE0/0/1 toward S1. Therefore, the traffic policy examines the reply packets, not the original ping request packets.
In those reply packets, the source IP address is 10.0.23.3, and the destination is one of S1's loopback addresses. The ACL rules denying 10.0.1.1 and 10.1.1.1 as source addresses do not match these reply packets, because those addresses appear as destination addresses, not source addresses. In addition, the ACL contains rule permit ip, which permits all remaining IP traffic. As a result, replies to all four S1 addresses are forwarded successfully, so every listed address can ping 10.0.23.3.
The following command output is displayed on R1:
[R1] display aaa configuration
Domain Name Delimiter : @
Domainname parse direction : Left to right
Domainname location : After-delimiter
Administrator user default domain : default_admin
Normal user default domain : default
Domain : total: 256 used: 3
Authentication-scheme : total: 32 used: 2
Accounting-scheme : total: 32 used: 1
Authorization-scheme : total: 32 used: 2
Service-scheme : total: 256 used: 0
Recording-scheme : total: 32 used: 0
Local-user : total: 512 used: 2
Remote-admin-user block retry-interval : 5 Min(s)
Remote-admin-user block retry-time : 3
Remote-admin-user block time : 5 Min(s)
Session timeout invalid enable : No
Which of the following statements is false?
Answer : B
Comprehensive and Detailed 150 to 200 words of Explanation From Datacom knowledge:
The false statement is B. From the AAA configuration output, the value of Remote-admin-user block time is clearly shown as 5 Min(s), which means the account lockout duration is 5 minutes, not 30 minutes.
Option A is true because Remote-admin-user block retry-time : 3 indicates that after 3 consecutive authentication failures, the account will be blocked. Option C is also true because the displayed Domain Name Delimiter is @, which is the separator used in usernames such as user@huawei.com. Option D is true as well because the output shows Local-user : total: 512 used: 2, meaning that the device supports a maximum of 512 local users, and currently 2 local users have been created.
This question checks the ability to correctly read AAA configuration output on Huawei devices. In HCIA-Datacom knowledge, it is important to distinguish between retry interval, retry count, and block time, because these values represent different security control parameters and are often confused during troubleshooting or configuration review.
During VLAN planning for a campus network, VLAN IDs for different service types must be allocated consecutively, without redundancy, to prevent omissions in future allocations.
Answer : B
This statement is false. In campus network VLAN planning, VLAN IDs do not have to be allocated strictly consecutively without any gaps. In fact, leaving some reserved VLAN IDs is often a practical and recommended design approach. VLAN planning should focus on clarity, scalability, maintainability, and service separation, rather than on forcing all VLAN IDs to be contiguous.
For example, an administrator may reserve certain VLAN ranges for user access, voice services, management, wireless services, guest access, future expansion, or specific departments. Such structured planning makes later network expansion easier and reduces the risk of service conflicts or disruptive renumbering. HCIA-Datacom emphasizes that good campus network planning should consider current requirements and future growth. Consecutive allocation may look tidy at first, but it can actually reduce flexibility and make later additions more difficult. Therefore, the idea that VLAN IDs must be assigned consecutively without redundancy to avoid omissions is not a correct design principle. Reasonable reservation and categorized allocation are often more beneficial in real enterprise campus networks.
The essence of communication is the transmission and exchange of information between two or more points. The three elements of communication are the sender, content, and transmission channel of the information. The receiver of the information is not included among these elements.
Answer : B
This statement is false because the receiver is one of the fundamental elements of communication. In basic communication theory, a complete communication process requires at least four essential elements: the sender, the information or message content, the transmission medium or channel, and the receiver. If the receiver is missing, communication cannot be completed because there is no endpoint to accept, interpret, or respond to the transmitted information.
In datacom networks, this concept maps directly to real networking scenarios. A source host generates data, the data is carried over some medium such as copper, fiber, or wireless, and a destination host receives the data. Network devices such as switches and routers assist the forwarding process, but the fundamental communication model still includes both communicating endpoints. HCIA-Datacom emphasizes the complete sender-to-receiver process when introducing network communication basics, protocol encapsulation, and forwarding. Therefore, excluding the receiver from the communication elements is conceptually incorrect. The correct understanding is that sender, receiver, information content, and channel together form the essential basis of communication.